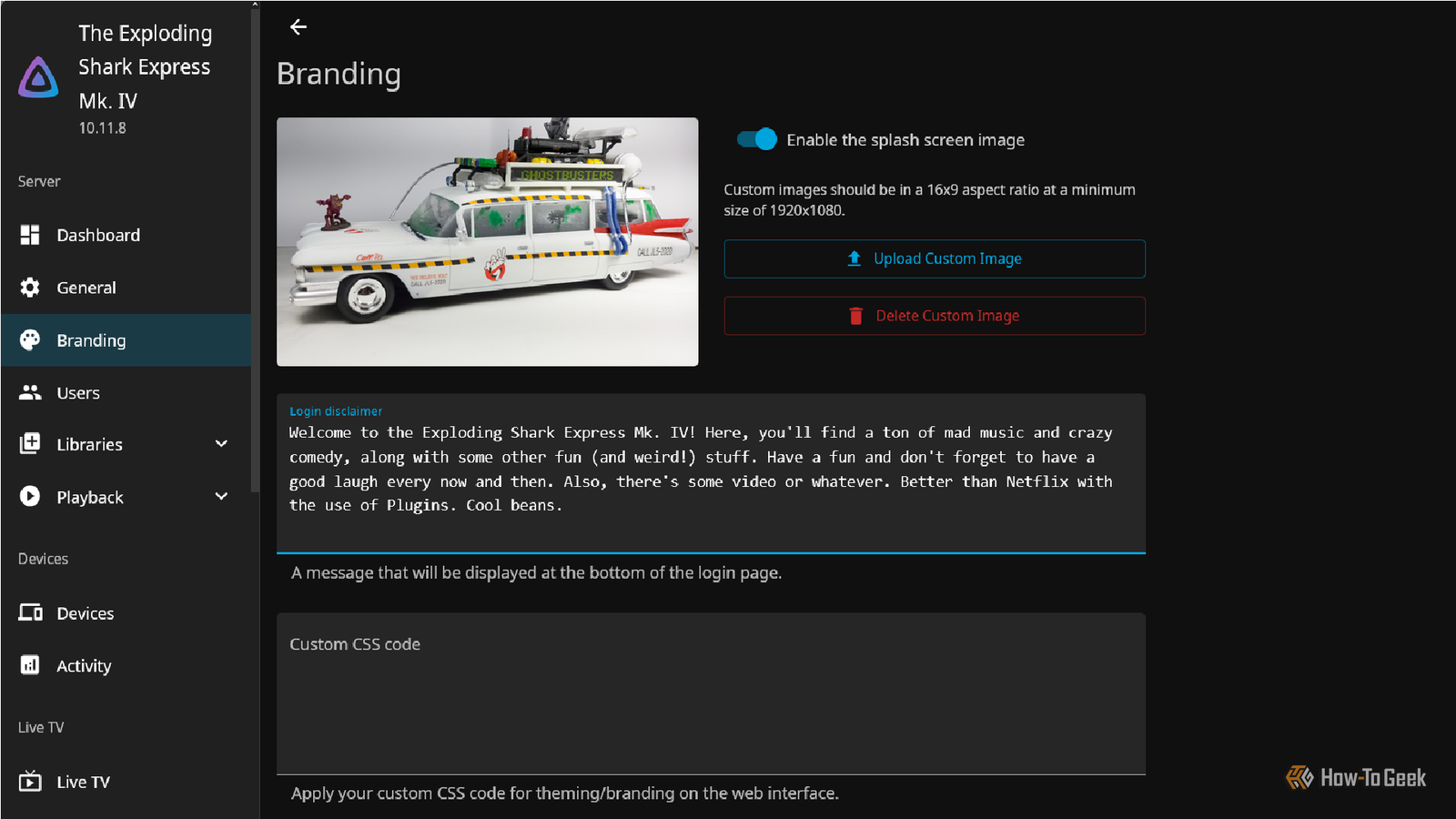
6 Jellyfin Plugins for a Netflix-Like Experience
Jellyfin is the premier open-source media server allowing users to reclaim their data from streaming giants. While it lacks the polished discovery algorithms of Netflix or Spotify, strategic plugin integration ... Read More