Jonathan Arriaga Obituary – Harrisburg, PA | 2026
Harrisburg, PA – Jonathan Ramirez Arriaga, a resident of Harrisburg, passed away on April 18, 2026, at Penn State Milton S. Hershey Medical Center. The news of his death has ... Read More

Saturday Edition
Stay updated with Archyde – your source for breaking news, global headlines, economy, entertainment, health, technology, and sports. Fresh stories daily.
Harrisburg, PA – Jonathan Ramirez Arriaga, a resident of Harrisburg, passed away on April 18, 2026, at Penn State Milton S. Hershey Medical Center. The news of his death has ... Read More
Continuous Coverage

Motorists travelling on Sydney’s Warringah Freeway will face significant disruptions starting this Saturday, October 28th, as Transport for…

Comedian Sinbad, 69, triumphantly returned to the stage this week at the Ice House Comedy Club in Pasadena,…

The air in Washington, D.C. Feels…thick. Not with humidity, but with a kind of performative absurdity that’s becoming…

Microsoft and OpenAI have restructured their long-term partnership, solidifying Azure as OpenAI’s primary cloud provider while granting OpenAI…
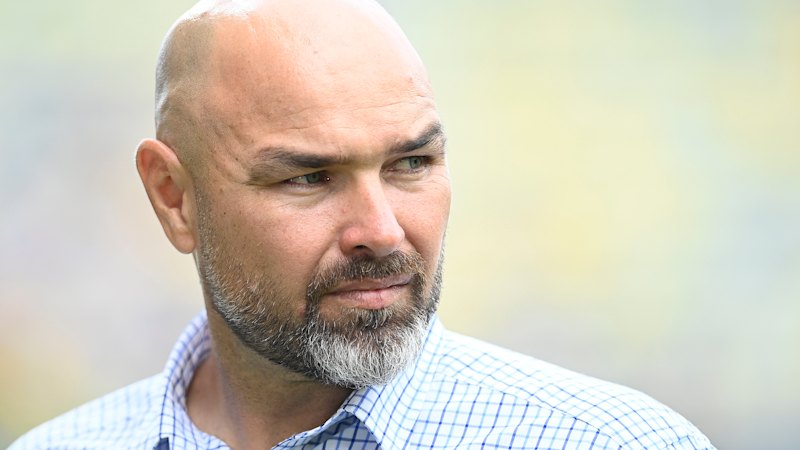
North Queensland Cowboys head coach Todd Payten is currently the sole NRL coach without a contract beyond the…

Uranium Mining Expansion in the U.S. Raises Groundwater Contamination Concerns Expanding uranium mining operations in the United States…
Global Affairs

The Cleveland Cavaliers defeated the Toronto Raptors 125-120 late Tuesday, taking a 3-2 series lead in their NBA…
Markets And Money

Shares of **Volkswagen (VWAGY)** are facing pressure Monday following the release of Q1 2026 earnings, revealing a 28%…
Digital Culture

Google Maps is now visibly flagging instances where businesses have deleted negative reviews, a move designed to increase…
Science And Wellbeing

A woman in Germany recently discovered the cause of her unexplained hair loss wasn’t a medical condition, but…
Screen And Sound

The Seattle Universal Math Museum in Kent Station, a hands-on learning center designed to develop mathematics engaging for…
Fixtures And Form
Archyde.com can confirm a startling trend in cycling safety: nearly 80% of collisions occur during daylight hours, challenging…