AWS has officially launched managed daemon support for Amazon ECS Managed Instances, decoupling operational agents from application tasks to streamline platform engineering. Available globally as of April 2026, this feature empowers infrastructure teams to enforce security and monitoring policies independently, eliminating deployment friction and ensuring consistent host-level visibility without coordinating with application developers.
The Decoupling of Operational Responsibility
In the high-stakes environment of 2026 cloud architecture, the line between application logic and infrastructure plumbing is no longer just blurred; it is a battleground for operational efficiency. For the $200k–$500k Technical Elite driving enterprise innovation, the ability to separate concerns is not a luxury—it is a requirement for scale. Historically, updating a logging agent or a security tracer on Amazon ECS meant touching the application task definition itself. This tight coupling created a bottleneck where a simple infrastructure patch required a full application redeployment, introducing unnecessary risk and latency.
That paradigm has shifted. With the introduction of managed daemons, AWS is effectively acknowledging that platform engineering has matured into a distinct discipline, separate from application development. This update allows platform teams to define, deploy, and manage operational tooling—such as the Amazon CloudWatch Agent or third-party security tracers—as a distinct layer of infrastructure. The result is a cleaner separation of duties where the “plumbing” is managed by those who understand the flow, not those who build the fixtures.
Architectural Deep Dive: The daemon_bridge and Privileged Contexts
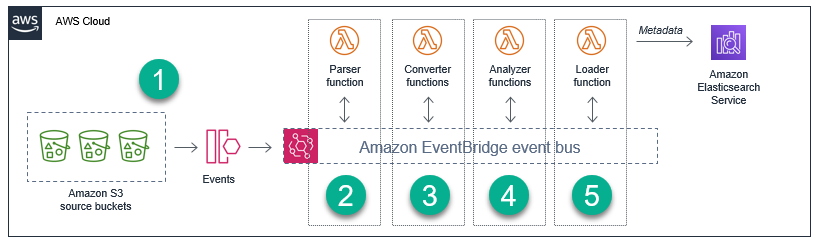
Under the hood, this isn’t just a UI tweak; it is a fundamental change in how the ECS agent orchestrates container lifecycles on managed instances. The modern architecture introduces a dedicated daemon task definition, which operates with a distinct validation scheme separate from standard application tasks. Crucially, this construct supports a new daemon_bridge network mode.
This network mode is the linchpin of the feature. It enables daemons to communicate with application tasks while remaining isolated from the application’s specific networking configurations. In practice, Which means a security agent can inspect traffic or a logging agent can scrape stdout without needing to be injected into the application’s security group or VPC configuration directly. The system supports advanced host-level access capabilities. Platform engineers can now configure daemon tasks as privileged containers, adding specific Linux capabilities and mounting paths from the underlying host filesystem.
This level of access is critical for the next generation of AI-powered security analytics and deep observability tools that require visibility into system calls and host metrics. By guaranteeing that the daemon starts before the application task and drains last, AWS ensures that there is no “blind spot” during the lifecycle of a container. The data collection begins before the first request is processed and ends only after the last connection is closed.
The Kubernetes Comparison: Convenience vs. Control
It is impossible to discuss daemon management without addressing the elephant in the room: Kubernetes DaemonSets. For years, the open-source community has relied on DaemonSets to ensure a pod runs on all (or some) nodes in a cluster. AWS’s new managed daemon construct is a direct response to this functionality, tailored specifically for the ECS Managed Instances capacity provider.
However, the implementation differs in philosophy. While Kubernetes offers granular control through taints, tolerations, and node selectors, ECS Managed Daemons prioritize operational simplicity and integration with the AWS control plane. The rolling deployment mechanism is handled automatically by ECS, provisioning new instances with the updated daemon, starting the daemon first, and then migrating application tasks. This “start before stop” approach is managed via a configurable drain percentage, giving platform engineers control over the blast radius of an update without writing complex operator logic.
“The shift towards managed infrastructure primitives like ECS Daemons signals that the industry is moving away from ‘do-it-yourself’ orchestration toward ‘managed outcomes.’ We are seeing a demand for Distinguished Engineers who can architect systems that abstract complexity without sacrificing visibility.” — Industry Consensus on Platform Engineering Trends, 2026
This move solidifies ECS as a viable alternative for workloads that require the robustness of Kubernetes but the operational overhead of a fully managed service. It reduces the cognitive load on teams who previously had to maintain custom operators or sidecar injection logic just to maintain their monitoring agents in sync.
Security Implications and the “Elite” Standard
From a security posture, this update is significant. In the past, ensuring that every instance in a fleet was running the latest version of a host-based intrusion detection system (HIDS) was a manual or script-heavy process. If an application team updated their task definition and forgot to bump the agent version, the instance would go live with a security gap.

Managed daemons enforce consistency. By centralizing the resource management—defining CPU and memory parameters separately from application configurations—platform teams can guarantee that security agents have the resources they need to function, regardless of how “noisy” the neighboring application tasks are. This aligns with the strategic patience required by modern elite security personas, who understand that defense in depth requires reliable, uninterrupted telemetry.
the ability to update agents without redeploying applications means that zero-day vulnerabilities in monitoring or logging software can be patched immediately. There is no need to wait for an application release cycle to fix an infrastructure vulnerability. This decoupling is a critical component of a resilient security architecture.
The 30-Second Verdict
- Who is this for? Platform Engineers and DevOps teams managing large fleets of ECS Managed Instances who need to enforce consistent operational tooling.
- What changed? Operational agents (daemons) are now decoupled from application tasks, managed via a new
daemon_bridgenetwork and dedicated task definitions. - Why it matters? It eliminates the coordination tax between app and infra teams, ensures 100% agent coverage, and allows for independent security patching.
- Cost? No additional cost for the feature itself; you pay only for the compute resources the daemon tasks consume.
For organizations heavily invested in the AWS ecosystem, this update removes one of the last friction points preventing ECS from being the default choice for high-scale, containerized workloads. It acknowledges that in 2026, the infrastructure is just as critical as the code it runs, and it deserves its own dedicated management plane.
To implement this, engineers can navigate to the Daemon task definitions option in the Amazon ECS console. The feature is available today in all AWS Regions. For those looking to audit their current setup, the Amazon ECS documentation provides the necessary API references to integrate this into existing CI/CD pipelines immediately.