Apple has removed several Virtual Private Network (VPN) applications from the Russian App Store this week, specifically targeting services enabling users to circumvent Russia’s Deep Packet Inspection (DPI)-based internet censorship. This move, occurring as geopolitical tensions remain high, signals a significant escalation in Apple’s compliance with Russian regulations and raises serious questions about its commitment to user privacy and freedom of information.
The DPI Arms Race: How Russia Controls the Flow
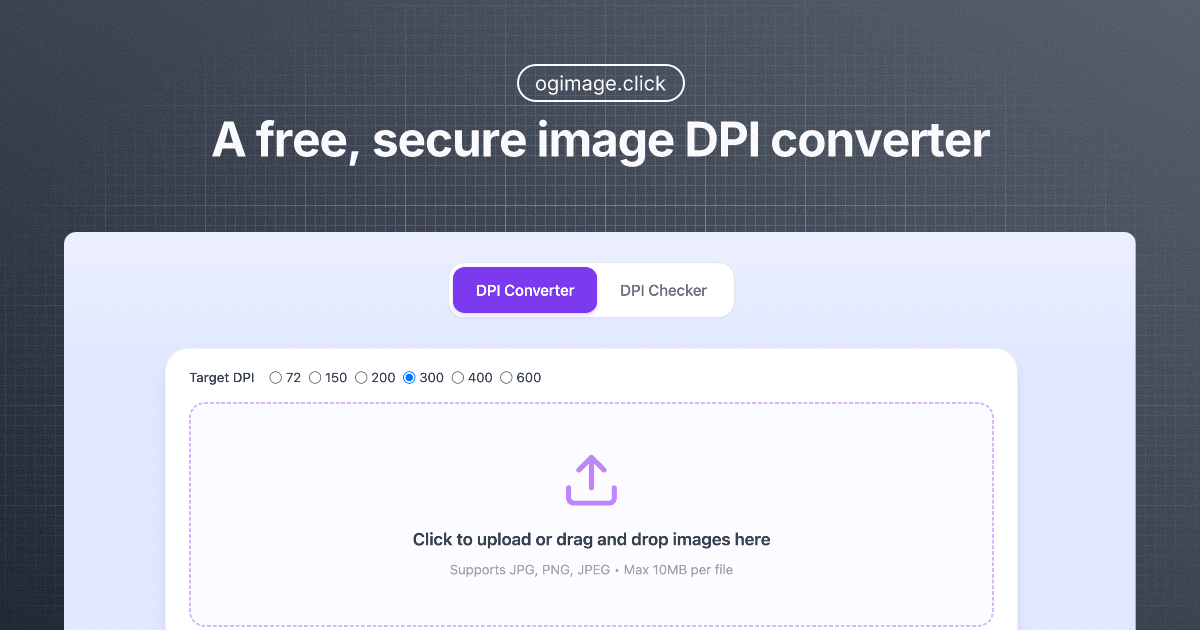
Russia’s censorship apparatus relies heavily on DPI, a technique that allows the government to inspect the contents of network packets and block access to websites and services deemed undesirable. VPNs, by encrypting internet traffic and routing it through servers in other countries, effectively bypass this DPI. The apps Apple removed – including prominent names like Proton VPN, ExpressVPN, and Surfshark – were specifically identified as tools facilitating this circumvention. This isn’t a blanket ban on VPNs globally; Apple continues to allow VPNs that comply with Russian regulations, which essentially require them to cooperate with the government’s censorship efforts. The technical challenge for Russia isn’t simply *detecting* VPN usage (though they’ve made strides in that area using techniques like TLS fingerprinting and identifying known VPN server IP addresses), but reliably *blocking* it without disrupting legitimate traffic. Here’s where the cat-and-mouse game intensifies, with VPN providers constantly adapting their protocols and obfuscation techniques.
What This Means for Enterprise IT
For multinational corporations operating in Russia, this development presents a complex challenge. Maintaining secure communication channels for employees becomes significantly harder. Even as corporate VPN solutions may still be viable, they are likely to face increased scrutiny and potential interference. The reliance on Apple devices within these organizations also becomes a point of vulnerability, as Apple’s actions demonstrate a willingness to prioritize local regulations over user privacy.
The core issue isn’t just about access to Facebook or Twitter (though that’s part of it). It’s about the fundamental ability to conduct business securely and without government surveillance. The Russian government’s motivations are clear: control the narrative, suppress dissent, and maintain a tight grip on information. Apple’s compliance, while framed as adherence to local laws, directly contributes to this outcome.
Beyond Russia: The Implications for Platform Lock-In
This situation highlights a critical tension inherent in Apple’s walled-garden ecosystem. While Apple touts the security and privacy benefits of its platform, it also exerts significant control over what applications are allowed on its devices. This control, as demonstrated in Russia, can be used to enforce censorship and suppress freedom of expression. The App Store’s stringent review process, while intended to protect users from malware and harmful content, can also be weaponized to silence dissenting voices. This isn’t unique to Apple, of course. Google’s Play Store faces similar criticisms, but Apple’s tighter control over its hardware and software arguably makes it a more potent enforcer of censorship.
The move also underscores the growing fragmentation of the internet. Different countries are increasingly erecting digital borders, creating a patchwork of regulations, and restrictions. This fragmentation makes it harder for users to access information freely and for businesses to operate globally. The long-term consequences could be a balkanization of the internet, with each country operating its own isolated digital sphere.
“Apple’s decision is a stark reminder that even the most privacy-focused companies are ultimately subject to political pressures. The fact that they’re complying with Russian demands to remove VPN apps sets a dangerous precedent, potentially emboldening other governments to push for similar restrictions.”
– Karim Hijazi, CEO of Silent Circle, a secure communications provider.
The Technical Underpinnings of VPN Detection and Blocking
Russia’s DPI systems aren’t static. They’re constantly evolving to identify and block VPN traffic. Early methods relied on identifying known VPN server IP addresses and port numbers. However, VPN providers quickly adapted by using obfuscated servers and dynamic IP addresses. More sophisticated techniques now involve analyzing the characteristics of encrypted traffic, looking for patterns that are indicative of VPN usage. This includes examining the TLS handshake process, the size and frequency of packets, and the use of specific encryption algorithms. The effectiveness of these techniques varies, and VPN providers are continually developing new methods to evade detection. One promising approach is the use of “stealth” protocols, such as Obfsproxy and Shadowsocks, which are designed to disguise VPN traffic as normal HTTPS traffic. However, even these protocols are not foolproof, and Russia is actively working to identify and block them.

The core of the problem lies in the asymmetry of the conflict. Russia has a centralized, well-funded censorship apparatus, while VPN providers are often smaller companies with limited resources. The battle is essentially a technological arms race, with each side constantly trying to outmaneuver the other. The recent Apple decision tips the scales in Russia’s favor, making it harder for users to bypass censorship.
The 30-Second Verdict
Apple’s actions in Russia are a betrayal of its stated commitment to user privacy and freedom of expression. This move sets a dangerous precedent and highlights the risks of relying on centralized platforms for secure communication.
The Open-Source Response and the Future of Circumvention
The situation in Russia is fueling a renewed interest in open-source VPN solutions and censorship-resistant technologies. Projects like WireGuard, a modern VPN protocol known for its speed and security, are gaining traction. The open-source nature of these projects allows for greater transparency and community scrutiny, making it harder for governments to censor them. However, even open-source VPNs are not immune to detection and blocking. The key to success lies in continuous innovation and the development of new techniques to evade censorship. The use of decentralized VPNs, built on blockchain technology, is also being explored as a potential solution. These VPNs distribute traffic across a network of nodes, making it harder for governments to identify and block them. However, decentralized VPNs are still in their early stages of development and face significant scalability and performance challenges.
The broader implications extend to the debate over platform neutrality. Should Apple, as a gatekeeper to a vast ecosystem of users, be allowed to enforce censorship on behalf of authoritarian governments? The answer, for many, is a resounding no. The future of the internet depends on preserving its openness and ensuring that users have the freedom to access information without fear of censorship.
“We’re seeing a concerning trend of tech companies prioritizing compliance with authoritarian regimes over the fundamental rights of their users. This isn’t just about VPNs; it’s about the future of a free and open internet.”
– Eva Galperin, Director of Cybersecurity at the Electronic Frontier Foundation (EFF).
The canonical URL for this story can be found here on Reuters. Further technical details on DPI can be found in this IEEE article. Information on the WireGuard protocol is available on its official website.

