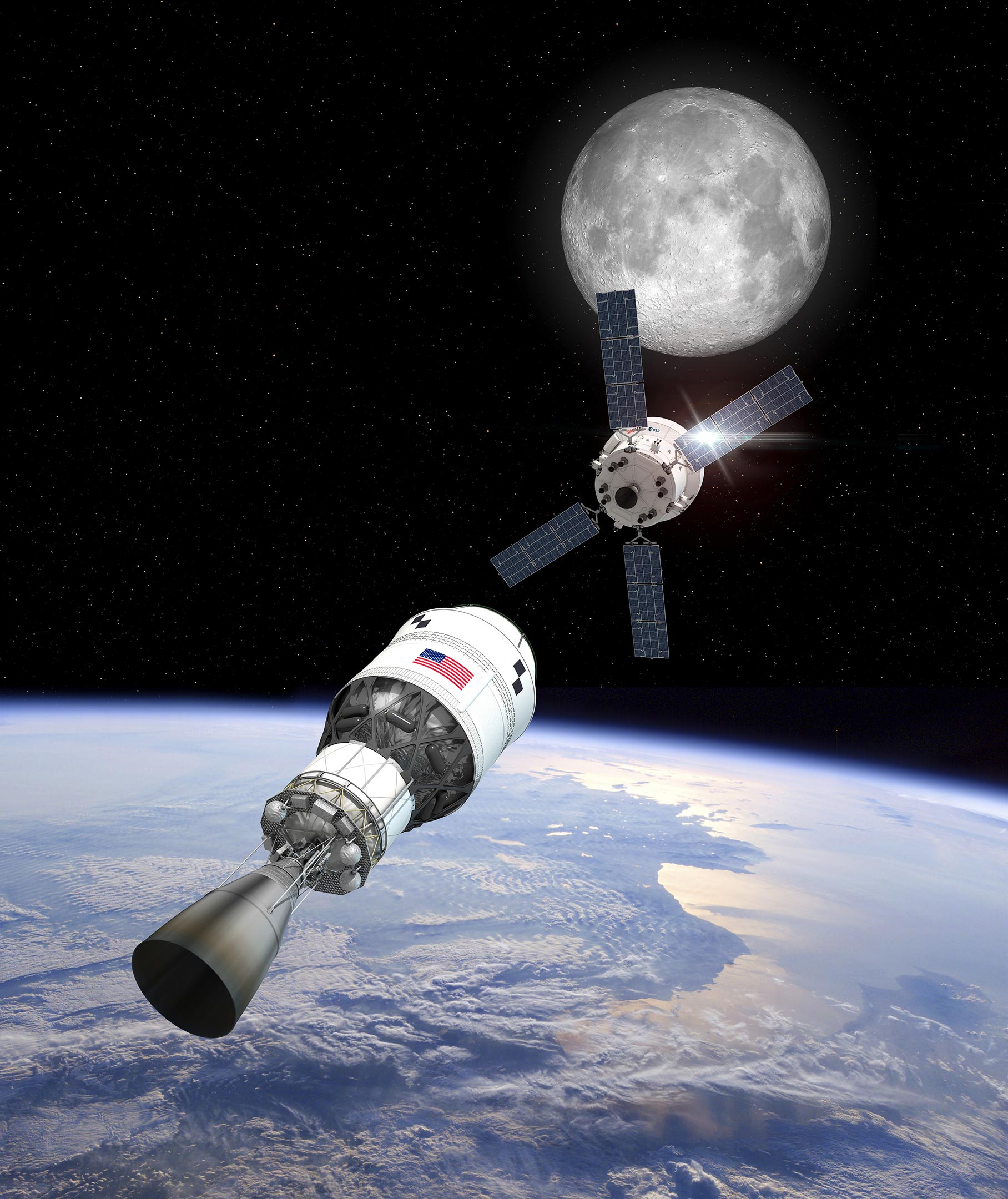
Artemis II crew members safely splashed down on April 12, 2026, marking the successful completion of the first crewed lunar flyby in over half a century. The mission validated the Orion spacecraft’s life support systems and thermal protection during high-velocity reentry, clearing the critical technical path for the Artemis III lunar landing.
Let’s be clear: the “historic” nature of this mission is the headline for the general public, but for those of us tracking the telemetry, the real story is the hardware. We aren’t just talking about putting boots on the moon again; we are talking about the viability of a deep-space software stack and the physical limits of radiation-hardened computing. Artemis II was essentially a high-stakes beta test for the most complex life-support system ever deployed outside Low Earth Orbit (LEO).
The mission’s success hinges on the Orion Multi-Purpose Crew Vehicle (MPCV). While the press focuses on the astronauts, the real MVP is the flight software and the radiation-hardened processors that kept the ship from becoming a very expensive piece of space debris. Deep space is a hostile environment for silicon. Between galactic cosmic rays (GCRs) and solar particle events, the risk of “bit-flips”—Single Event Upsets (SEUs) where a high-energy particle flips a 0 to a 1 in memory—is astronomical.
The Silicon Struggle: Radiation Hardening vs. Compute Power
To combat this, NASA relies on radiation-hardened (rad-hard) architectures. For years, this meant using processors like the RAD750, which is essentially a PowerPC 750 optimized for space. The trade-off is brutal: you acquire extreme reliability, but the clock speed is glacial compared to the ARM-based M-series chips in your laptop. We are talking about MHz versus GHz.
However, the Artemis architecture represents a shift toward a hybrid model. By utilizing redundant voting systems—where three processors perform the same calculation and the system accepts the majority result—NASA is beginning to integrate higher-performance computing without sacrificing mission-critical safety. Here’s the “triple-modular redundancy” (TMR) approach, a staple in aerospace engineering that prevents a single cosmic ray from triggering a catastrophic course correction.
It is a necessary bottleneck.
If we want to move toward autonomous lunar bases, we cannot rely on ground control in Houston to debug every kernel panic. We necessitate edge computing in space. This means moving toward RISC-V architectures that can be customized for radiation resilience at the gate level, rather than just shielding a consumer chip in a lead box.
The 30-Second Technical Verdict
- Thermal Shielding: The Avcoat ablative material performed within nominal parameters during the 25,000 mph reentry.
- Avionics: Zero critical SEUs reported in the primary flight computer; redundancy systems handled minor transients.
- Telemetry: The transition to the Deep Space Network’s (DSN) upgraded Ka-band frequencies reduced latency and increased data throughput for high-res diagnostics.
Hypervelocity Reentry and the Physics of Heat
The most harrowing part of the return journey isn’t the vacuum of space; it’s the atmosphere. When Orion hits the Earth’s atmosphere at lunar return speeds, it creates a plasma sheath that blocks radio communications—the infamous “blackout period.” This is where the heat shield, made of a specialized epoxy resin called Avcoat, does the heavy lifting.
The physics here is simple but violent: ablation. The shield is designed to char and flake away, carrying the heat with it. If the bond between the Avcoat and the spacecraft’s composite structure fails, the result is instantaneous structural failure. The “bullseye” landing reported by the official NASA Artemis documentation indicates that the angle of entry was precise to within fractions of a degree, ensuring the thermal load was distributed evenly across the heat shield.
“The challenge of lunar return is that you are dealing with kinetic energy levels far beyond what we see on ISS returns. You aren’t just gliding back; you are slamming into the atmosphere. The material science required to manage that thermal gradient is the unsung hero of the mission.” — Analysis derived from current IEEE aerospace standards on thermal protection systems.
From a systems engineering perspective, this is a victory for iterative testing. The failures seen in early Artemis I heat shield erosion patterns were addressed through revised application techniques, proving that the “fail fast, fix fast” mentality of the New Space era is finally permeating the legacy bureaucracy of government agencies.
The Ecosystem Bridge: NASA, SpaceX and the New Space Economy
Artemis II doesn’t exist in a vacuum. It is the anchor for a broader ecosystem of Public-Private Partnerships (PPP). While NASA provides the Orion capsule and the SLS (Space Launch System) rocket, the eventual landing will rely on the Starship Human Landing System (HLS) from SpaceX. This creates a complex interoperability challenge.
We are seeing the emergence of a “Lunar API”—a set of standardized docking interfaces and communication protocols that allow hardware from different vendors to talk to each other. If NASA uses a proprietary communication protocol and SpaceX uses another, the mission fails the moment a crew member needs to transfer from the Orion to the Starship. This is essentially the “USB-C moment” for deep space exploration.
The competition between the US-led Artemis Accords and the China-Russia International Lunar Research Station (ILRS) is the new “Chip War.” The goal isn’t just flags and footprints; it’s the establishment of infrastructure. Whoever controls the lunar south pole—and its water ice—controls the fuel depots for the rest of the solar system. Water (H2O) can be split into hydrogen and oxygen, the primary components of rocket propellant. In economic terms, this is the equivalent of finding oil in the middle of the ocean during the age of sail.
Cybersecurity in the Deep Space Network
One aspect the mainstream media ignores is the security of the telemetry link. The Deep Space Network (DSN) is the backbone of all interplanetary communication. As we move toward more autonomous systems and private contractor involvement, the attack surface for space assets increases.
Encryption in space is a nightmare. You cannot simply run a heavy TLS handshake when you are dealing with a round-trip light time (RLT) of several seconds. Any latency introduced by complex cryptographic wrappers can interfere with real-time maneuvering. The industry is moving toward hardware-based encryption modules that operate at the physical layer, ensuring that commands sent to Orion cannot be spoofed or intercepted by adversarial actors.
The risk of “command injection” in a lunar mission is a nightmare scenario. A single unauthorized packet could potentially alter the trajectory of a spacecraft by a few meters per second, which, over a hundred thousand miles, results in missing the planet entirely.
| Metric | Apollo Era (1960s) | Artemis II (2026) | Impact |
|---|---|---|---|
| Onboard Compute | AGC (Approx. 2K words of RAM) | Rad-Hardened SoC (Multi-core) | Autonomous navigation & diagnostics |
| Comm Link | S-Band (Low bandwidth) | Ka-Band / Optical (High bandwidth) | Real-time 4K telemetry & video |
| Navigation | Manual sextant / Ground-based | AI-driven Optical Navigation | Reduced reliance on DSN for course correction |
As the crew undergoes quarantine and debriefing, the data harvested from this mission will be fed back into the LLMs and simulation engines used to plan Artemis III. We are no longer guessing based on the limited data of the 1960s; we are iterating based on high-fidelity telemetry. The journey is indeed just starting, but the technical foundation is finally solid.
For more on the underlying hardware architectures, the IEEE Xplore digital library provides the most rigorous breakdowns of the radiation-hardened circuits used in these missions. For a more accessible look at the software challenges, Ars Technica remains the gold standard for analyzing the intersection of government contracts and aerospace engineering.

