TikTok has evolved from a short-form video platform into a global social commerce engine, leveraging hyper-personalized recommendation algorithms to drive a massive gray market in emerging economies. By integrating shopping APIs directly into the feed, ByteDance has fundamentally altered how hardware—from iPhones to Samsung devices—is distributed and verified globally.
The snippet currently circulating in West African markets—promising “authentic” LG and Samsung devices in Senegal to finish the era of “copies”—is a textbook example of the “Algorithm-to-Doorstep” pipeline. It isn’t just a sales pitch; it is a symptom of a systemic shift in the global supply chain. We are seeing the death of the traditional retail storefront in favor of a decentralized, feed-driven marketplace where trust is brokered not by a brand’s physical presence, but by the perceived authenticity of a creator’s content.
This is the latest frontier of the tech war. It’s no longer just about who owns the most data; it’s about who controls the transaction layer of the Global South.
The Algorithmic Engine Driving Gray-Market Hardware
At the core of this phenomenon is ByteDance’s recommendation engine, which operates on a scale of parameterization that dwarfs traditional e-commerce search. Unlike Amazon, which relies on intent-based search (you look for a phone), TikTok utilizes interest-based discovery. Using a sophisticated neural network architecture, the platform identifies users with a high propensity for hardware upgrades and pushes “authentic” deals directly into their consciousness.
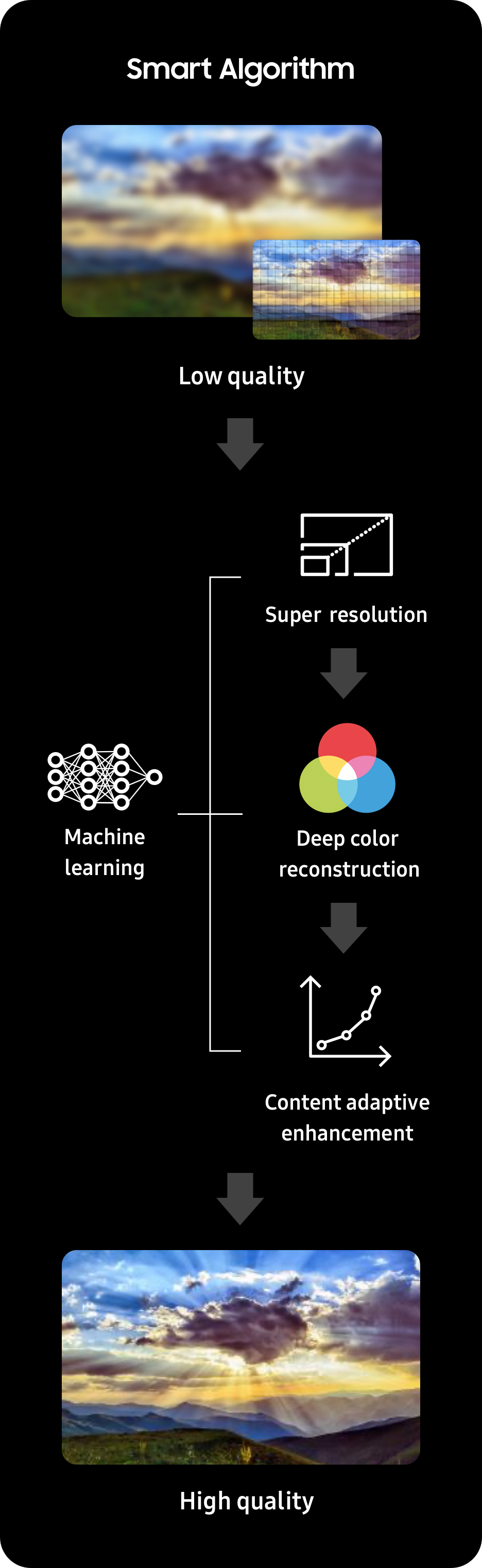
From a technical standpoint, this is an optimization problem. The algorithm analyzes user engagement with specific hardware keywords and visual cues (like the shimmer of a titanium frame) to segment audiences. When a seller in Senegal posts about “authentic” Samsung devices, the NPU (Neural Processing Unit) on the user’s device helps process the video’s metadata in real-time, ensuring the content hits the exact demographic most likely to be frustrated by “copies.”
The danger lies in the “Information Gap.” The platform’s API allows for seamless checkout, but it does not inherently verify the hardware’s provenance. There is no blockchain-backed ledger for IMEI numbers integrated into the TikTok Shop checkout flow. This creates a vacuum where sophisticated “super-clones”—devices that mimic the UI and basic specs of a flagship phone but run a skinned version of Android instead of iOS—can be marketed as authentic.
The Hardware Gap: Distinguishing Silicon from Super-Clones
To the average consumer, a “copy” is obvious. To a tech analyst, the battle is fought at the SoC (System on a Chip) level. Authentic flagship devices from Apple or Samsung utilize cutting-edge 3nm or 4nm process nodes, providing massive leaps in power efficiency and thermal management. Super-clones, though, typically rely on aging MediaTek or Unisoc chipsets that are overclocked to mimic benchmark scores.
If you are buying a “authentic” device via a TikTok lead in 2026, you aren’t just buying a phone; you are gambling on the silicon. A genuine device will have a secure enclave for biometric data and end-to-end encryption that is hardware-accelerated. A clone will often emulate these features in software, creating a massive cybersecurity vulnerability.
“The rise of social-commerce hardware sales in emerging markets has created a ‘verification crisis.’ We are seeing an increase in devices that pass basic software checks but fail at the kernel level, often containing pre-installed backdoors that bypass standard OS security.”
The technical breakdown of the difference is stark:
| Feature | Authentic Flagship (2026) | High-End “Super-Clone” |
|---|---|---|
| Processor | Custom ARM-based 3nm SoC | Generic 7nm/12nm SoC (Overclocked) |
| NPU Performance | Dedicated AI cores for on-device LLMs | Software-emulated AI functions |
| Security | Hardware Root of Trust (RoT) | Software-level spoofing |
| Display | LTPO OLED with variable refresh | Standard AMOLED or high-end LCD |
Trust Architecture and the Failure of Platform Governance
Why does this persist? Because the friction of verification is higher than the friction of purchase. ByteDance has optimized the “Buy” button, but they have not optimized the “Verify” button. For a user in Dakar or Saint-Louis, the social proof of a viral video outweighs the technical necessity of checking a device’s firmware signature.

This is a failure of trust architecture. In a closed ecosystem, the manufacturer controls the distribution. In the TikTok ecosystem, the distribution is democratized, but the accountability is fragmented. The sellers claiming “Fini les arnaques” (End of scams) are utilizing the same psychological triggers as the scammers they claim to replace: urgency, exclusivity, and the promise of “authenticity” in a sea of fakes.
From a developer’s perspective, the only way to solve this is through an open-source hardware verification API that can be called during the checkout process. Imagine a system where the seller must upload a cryptographically signed token from the device’s secure enclave before the listing can be marked as “Verified Authentic.” Until that exists, the “authentic” label on a TikTok ad is essentially vaporware.
The Geopolitical Stakes of the ByteDance Ecosystem
This isn’t just about phones in Senegal. This is about the “Chip Wars” and the expansion of the Chinese tech stack. By facilitating the flow of hardware through social channels, ByteDance is effectively building a shadow logistics network that bypasses traditional Western-led distribution channels.
If the platform becomes the primary gateway for hardware acquisition in the Global South, the influence shifts from the manufacturer to the curator. The algorithm decides which brands survive and which clones thrive. This creates a dangerous precedent for platform lock-in, where the “discovery” of a product is more essential than the product’s actual engineering.
We are seeing a convergence of ARM architecture, LLM-driven marketing, and decentralized logistics. It is a potent mix that favors the agile and the aggressive over the established and the regulated.
The 30-Second Verdict
- The Tech: TikTok’s recommendation engine is now a primary driver for gray-market hardware distribution.
- The Risk: “Super-clones” are becoming indistinguishable from authentic hardware to the untrained eye, posing severe security risks.
- The Gap: There is a critical lack of hardware-level verification (IMEI/Firmware) within social commerce APIs.
- The Bottom Line: In the 2026 hardware landscape, “authentic” is a marketing term, not a technical specification, unless verified via a secure root of trust.
For those navigating this landscape, the advice remains the same: trust the silicon, not the feed. If you cannot verify the bootloader or the hardware signature via a trusted third-party tool like community-vetted open-source diagnostics, you aren’t buying a flagship—you’re buying a very expensive piece of mimicry.

