TeamPCP, a financially motivated cybercrime group, has deployed the ‘CanisterWorm’ wiper malware targeting Iranian infrastructure via cloud supply chains. Leveraging compromised GitHub Actions for vulnerability scanners Trivy and KICS, the worm utilizes Internet Computer Protocol (ICP) canisters for resilient command-and-control, executing data destruction on systems matching Iranian timezones and locales.
The distinction between a script kiddie and a strategic threat actor often lies in infrastructure persistence. This weekend, the lines blurred further as TeamPCP demonstrated a sophisticated grasp of cloud-native exploitation, moving beyond simple phishing to poison the very tools developers trust to secure their code. The campaign, dubbed ‘CanisterWorm’ by researchers at Aikido, isn’t just another ransomware variant; it represents a shift toward serverless, blockchain-resilient command-and-control (C2) architectures that traditional takedowns cannot easily sever.
The Death of the Perimeter in Cloud-Native Warfare
Traditional cybersecurity models assume a perimeter—a firewall guarding the castle. TeamPCP ignored the castle walls entirely and walked through the front door of the cloud control plane. The group’s initial access vector wasn’t a zero-day in Windows or a phishing email to an HR director. It was exposed Docker APIs and misconfigured Kubernetes clusters.
By targeting the orchestration layer, the attackers bypassed endpoint detection entirely. When a worm propagates through a Kubernetes cluster, it doesn’t need to infect a laptop; it infects the node. From there, lateral movement is trivial. The group’s reliance on the Trivy vulnerability scanner supply chain highlights a critical vulnerability in the DevSecOps ecosystem: we trust our security tools implicitly.
When a tool like Trivy or KICS (Checkmarx Infrastructure as Code Scanner) is compromised, it gains elevated privileges within the CI/CD pipeline. These tools require broad access to scan code for secrets and vulnerabilities. By injecting credential-stealing malware into the GitHub Actions workflow of these scanners, TeamPCP effectively turned the security guard into the burglar. The malware snarfed SSH keys, cloud credentials, and Kubernetes tokens, granting the attackers root-level access to the victim’s cloud environment before the wiper payload was even deployed.
Why Internet Computer Protocol (ICP) Changes the Takedown Game
The most technically arresting aspect of this campaign is the use of Internet Computer Protocol canisters for C2 infrastructure. In traditional botnets, security firms coordinate with ISPs and hosting providers to sinkhole domains or seize servers. ICP canisters operate differently. They are tamperproof, blockchain-based smart contracts that combine code and data.

Because these canisters exist on a decentralized network, there is no central server to raid. As long as the operators pay the requisite “cycles” (virtual currency fees) to the network, the canister remains reachable. This creates a “hydra” effect for defenders: cutting off one node does nothing if the logic is replicated across the distributed ledger.
For the malware author, this means resilience. For the enterprise, it means that signature-based blocking of a C2 domain is futile. The malware doesn’t phone home to evil-server.com; it interacts with a smart contract address that can rotate its logic or serve different payloads (like the Rick Roll video observed by researchers) without changing the underlying binary on the infected host.
The 30-Second Verdict on ICP Malware
- Persistence: High. Decentralized hosting resists standard takedown requests.
- Detection: Hard. Traffic looks like standard blockchain RPC calls.
- Mitigation: Network egress filtering for non-standard blockchain ports and monitoring for unexpected ICP library calls in production environments.
Supply Chain Poisoning: The Trivy and KICS Vector
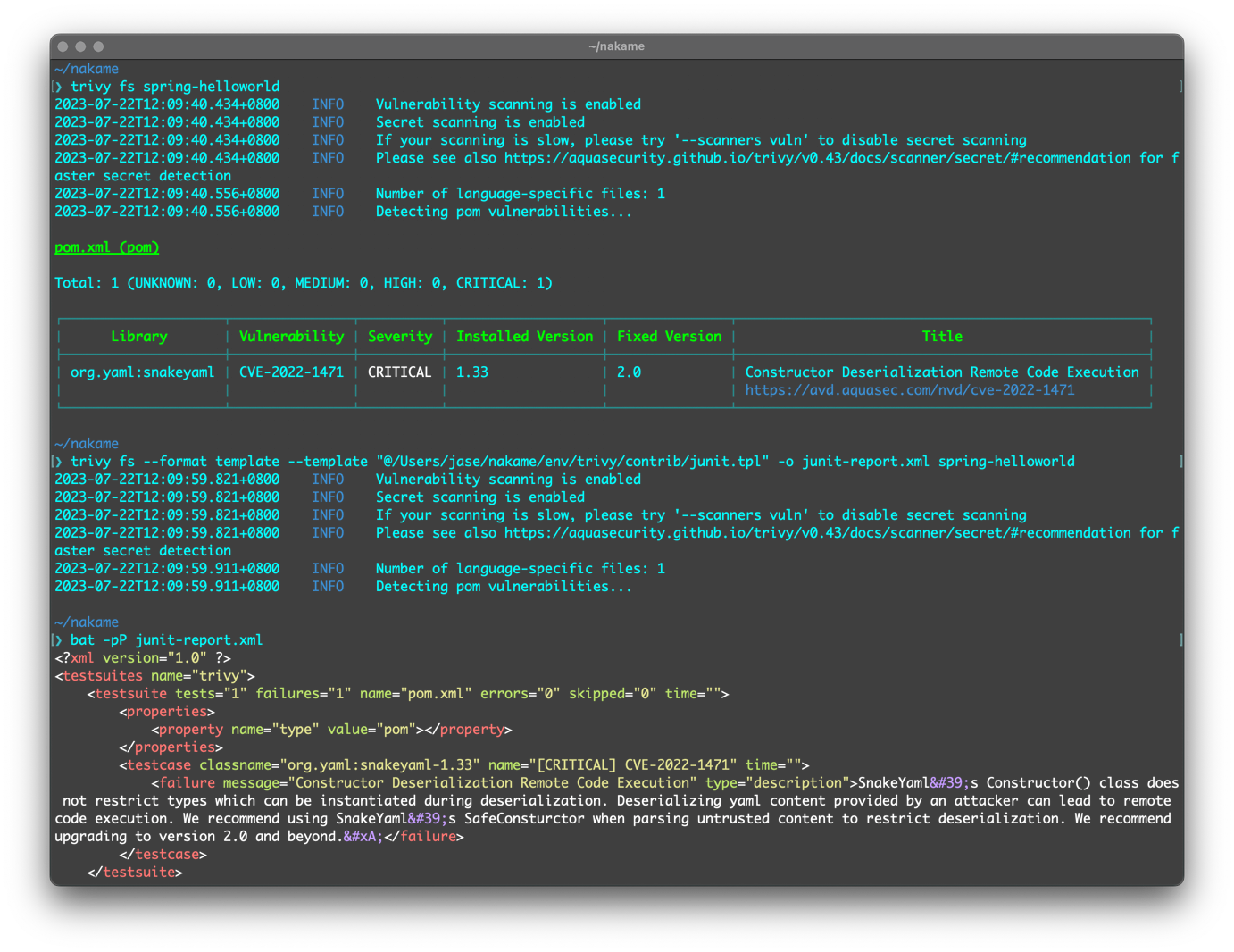
The infection chain began with a supply chain attack against Aqua Security’s Trivy scanner. On March 19, malicious code was injected into official releases on GitHub Actions. This wasn’t a one-off; it was a systemic compromise of the build pipeline. Wiz researchers noted that the attackers published malicious versions capable of exfiltrating sensitive data directly from the build environment.
By March 23, the same infrastructure was used to compromise Checkmarx’s KICS scanner. This rapid succession suggests an automated pipeline for compromising open-source security tools. The goal appears to be twofold: financial extortion via stolen credentials and geopolitical signaling via the Iran-specific wiper.
The “Chaotic Evil” persona described by security researcher Charlie Eriksen—flashing between data theft, wiper deployment, and Rick Rolling—suggests a group testing the boundaries of detection. They are probing how long they can retain malicious packages prominent in GitHub searches. As noted by Risky Business, attackers are now buying GitHub stars and pushing meaningless commits to keep their malicious repos at the top of search results, exploiting the platform’s trust metrics.
“The group industrializes existing vulnerabilities, misconfigurations, and recycled tooling into a cloud-native exploitation platform that turns exposed infrastructure into a self-propagating criminal ecosystem.” — Assaf Morag, Flare
Enterprise Mitigation: Beyond Patching
Patching the specific Trivy or KICS versions is necessary but insufficient. The broader lesson here is about supply chain integrity. Enterprises relying on open-source security tools must implement strict pinning of dependency versions. Allowing CI/CD pipelines to pull the “latest” tag is a security anti-pattern in 2026.
the use of ICP canisters necessitates a review of egress traffic. Security teams should audit outbound connections from their build agents and production clusters. Unexpected connections to blockchain nodes or ICP endpoints should trigger immediate isolation.
The “Elite Hacker” persona analysis suggests that strategic patience is key for defenders. TeamPCP is not rushing; they are establishing a foothold. The wiper component, which checks for Farsi language settings and Iranian timezones, indicates a targeted intent, but the credential harvesting is indiscriminate. This dual-purpose approach maximizes ROI for the attackers: if the geopolitical target isn’t hit, the financial theft still pays the bills.
Immediate Action Items for DevSecOps
- Audit GitHub Actions: Review all workflow runs for the past 30 days for unauthorized secret access.
- Pin Dependencies: Move from semantic versioning (e.g.,
v1.0) to specific commit hashes for all critical security tools. - Rotate Credentials: Assume any cloud credentials stored in environments using compromised scanners are breached. Rotate AWS keys, Azure Service Principals, and Kubernetes tokens immediately.
- Monitor ICP Traffic: Implement firewall rules to block or alert on traffic to known Internet Computer Protocol nodes if not business-critical.
The CanisterWorm campaign is a stress test for the open-source ecosystem. It proves that trust is the most vulnerable protocol in the stack. As we move deeper into an era of AI-assisted coding and automated deployment, the surface area for these attacks expands. The code might be open, but the supply chain is increasingly opaque. Defenders must shift from trusting the source to verifying the build.

