Luciano Schipelliti, a 28-year-old Haverhill resident, has pleaded guilty to wire fraud for orchestrating a $350,000 cryptocurrency investment scheme. The conviction highlights persistent vulnerabilities in retail crypto onboarding and the efficacy of federal blockchain forensics in tracing illicit fund flows across decentralized ledgers.
The blockchain was designed to be immutable, a ledger of truth etched in silicon, and math. Yet, the human interface remains the weakest link in the stack. This week, U.S. Senior District Court Judge F. Presided over the sentencing phase of Luciano Schipelliti, a case that serves as a grim reminder that while smart contracts execute automatically, social engineering executes manually. Schipelliti’s guilty plea to wire fraud isn’t just a legal footnote. it is a data point in the ongoing war between decentralized finance (DeFi) protocols and centralized regulatory enforcement.
We are not looking at a sophisticated zero-day exploit or a flash loan attack that drained a liquidity pool. We are looking at the oldest hack in the book: trust. Schipelliti allegedly convinced victims to transfer funds into what they believed were legitimate investment vehicles. In the architecture of modern cybercrime, the “platform” is often a mirage—a centralized database wrapped in a Web3 frontend, designed to mimic the aesthetics of legitimacy while functioning as a black hole for capital.
The Architecture of Deception: Cloned Frontends and Centralized Backends
To understand the mechanics of this $350,000 extraction, one must look past the legal charges and examine the technical implementation. Most investment schemes of this magnitude in 2026 rely on a hybrid architecture. The victim interacts with a sleek, responsive frontend—often a Progressive Web App (PWA) that mimics the UI of established exchanges like Coinbase or Kraken. However, the backend is entirely centralized and controlled by the bad actor.
When a user deposits crypto, the transaction is recorded on-chain, but the “balance” displayed to the user is merely a string in a SQL database controlled by the scammer. There is no interaction with a smart contract for yield generation; the “returns” are fabricated numbers updated via an admin panel. This disconnect between the on-chain reality and the off-chain presentation is where the fraud lives.
Chainalysis data from early 2026 indicates that while pure smart contract hacks have decreased due to better auditing tools, “rug pulls” and fake investment platforms have surged by 14%. The technical barrier to entry for launching a fake exchange has never been lower, thanks to open-source templates available on GitHub that clone major exchange interfaces with minimal modification.
Wire Fraud in the Age of Immutable Ledgers
The charge of wire fraud is particularly potent in this context. Unlike securities fraud, which requires proving the existence of an unregistered security, wire fraud focuses on the transmission of data. In Schipelliti’s case, the digital transmission of value across state lines via the internet constitutes the wire. This legal framework allows federal prosecutors to bypass the murky definitions of what constitutes a “token” or a “security” under the Howey Test, focusing instead on the intent to defraud during the transmission process.
This distinction is critical for the cybersecurity community. It means that even if a project claims to be a decentralized protocol, if there is a central point of control where funds are misappropriated through deceptive communication, the DOJ will treat it as traditional fraud. The blockchain provides the evidence trail, but the legal hammer is forged in traditional statutes.
“The misconception is that crypto scams are untraceable. In reality, the public ledger provides a higher fidelity audit trail than traditional banking. The challenge isn’t tracing the funds; it’s the jurisdictional hopscotch once those funds hit a mixer or a privacy coin.” — Elena Rostova, Senior Forensic Analyst at TRM Labs
Rostova’s insight underscores the cat-and-mouse game of 2026. While Schipelliti was caught, likely due to the funds remaining in traceable wallets or being cashed out through KYC-compliant on-ramps, more sophisticated actors utilize privacy-enhancing technologies (PETs) to break the link. However, the guilty plea suggests that operational security (OpSec) failures—perhaps reusing IP addresses or failing to sanitize metadata—led to his identification.
The Forensic Trail: From Haverhill to the Blockchain
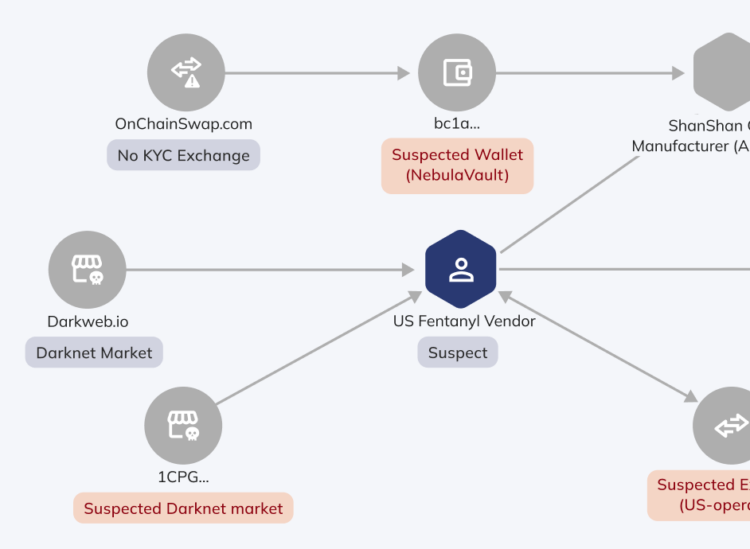
Investigating a case like this requires a convergence of traditional detective work and blockchain analytics. Investigators likely utilized cluster analysis to group addresses controlled by Schipelliti. By analyzing transaction graphs, they could identify patterns consistent with consolidation wallets—addresses where funds from multiple victims are swept before being moved to an exchange for liquidation.
In 2026, tools like Elliptic and Chainalysis Reactor have become standard issue for federal task forces. These platforms ingest mempool data in real-time, tagging addresses associated with known illicit activities. The speed at which these tags are applied has increased dramatically, reducing the window of opportunity for bad actors to launder funds through decentralized exchanges (DEXs).
the integration of AI-driven pattern recognition has allowed investigators to flag suspicious behavior before funds are fully drained. If a wallet exhibits behavior consistent with a “honeypot” contract or a known scam template, automated alerts can be triggered. In Schipelliti’s case, the digital footprint was likely substantial, given the relatively modest sum of $350,000, which often lacks the resources for high-end laundering services.
Regulatory Friction and the End of Pseudonymity
This conviction arrives at a pivotal moment for the crypto ecosystem. As we move deeper into 2026, the tension between privacy and compliance is reaching a breaking point. The Travel Rule, which requires Virtual Asset Service Providers (VASPs) to share sender and receiver information, is being strictly enforced across major jurisdictions. This creates a hostile environment for the cash-out phase of any investment scheme.
For the average developer and user, this signals a shift toward “Compliant DeFi.” Protocols are increasingly integrating identity layers, such as Ethereum Name Service (ENS) with verified credentials, to satisfy regulatory requirements without sacrificing the user experience. However, this likewise centralizes the attack surface. If identity data is stored on-chain or in linked databases, it becomes a target for phishing and social engineering attacks, ironically increasing the risk of the very crimes Schipelliti committed.
The 30-Second Verdict for Enterprise Security
- Vulnerability: Human trust, not code exploits, remains the primary vector for capital loss.
- Mitigation: Enterprises must enforce strict allow-listing for wallet interactions and utilize hardware security modules (HSMs) for treasury management.
- Outlook: Expect increased DOJ focus on “fake exchange” infrastructure hosting, targeting the server providers and domain registrars facilitating these scams.
The guilty plea of Luciano Schipelliti is a victory for the Department of Justice, but it is not a patch for the underlying vulnerability. As long as the promise of high yield exists, there will be bad actors willing to build the infrastructure to capture it. The technology to secure these networks exists—multi-sig wallets, time-locked contracts, and formal verification. The challenge remains cultural: convincing the market that if an investment sounds too good to be true, the code probably says so, too.
For the tech community, the lesson is clear. We must build systems that verify, not just trust. In a world of deepfakes and cloned interfaces, the only truth is the one you can cryptographically prove.

