After Two Decades, Gmail Finally Lets You Ditch the Embarrassing Username
Google has, after 22 years, begun rolling out a feature allowing Gmail users to change their usernames – the portion of their email address *before* the @gmail.com. This move, initially appearing in beta this week, addresses a long-standing user frustration and represents a subtle but significant shift in Google’s approach to user identity and platform lock-in. The change isn’t simply cosmetic. it has implications for account recovery, federated identity, and the broader competitive landscape of email providers.
The Legacy of ‘Geeky Hunks’ and the Problem with Immutable Identities
For years, Gmail’s insistence on a permanent username felt increasingly anachronistic. In the early 2000s, the scarcity of desirable usernames justified the rigidity. Now, with billions of accounts, that constraint is artificial. The inability to change a username created a persistent pain point, particularly for users who chose usernames during their teenage years or before fully understanding the implications of a publicly visible digital identity. This isn’t merely about aesthetics; a professional using a childhood nickname in their email address can face credibility issues. The technical challenge, as Google likely discovered, wasn’t the username change itself, but the cascading effects on linked services and account recovery mechanisms. The core issue is maintaining data integrity across a vast, interconnected system.
Under the Hood: How Google is (Likely) Handling the Transition
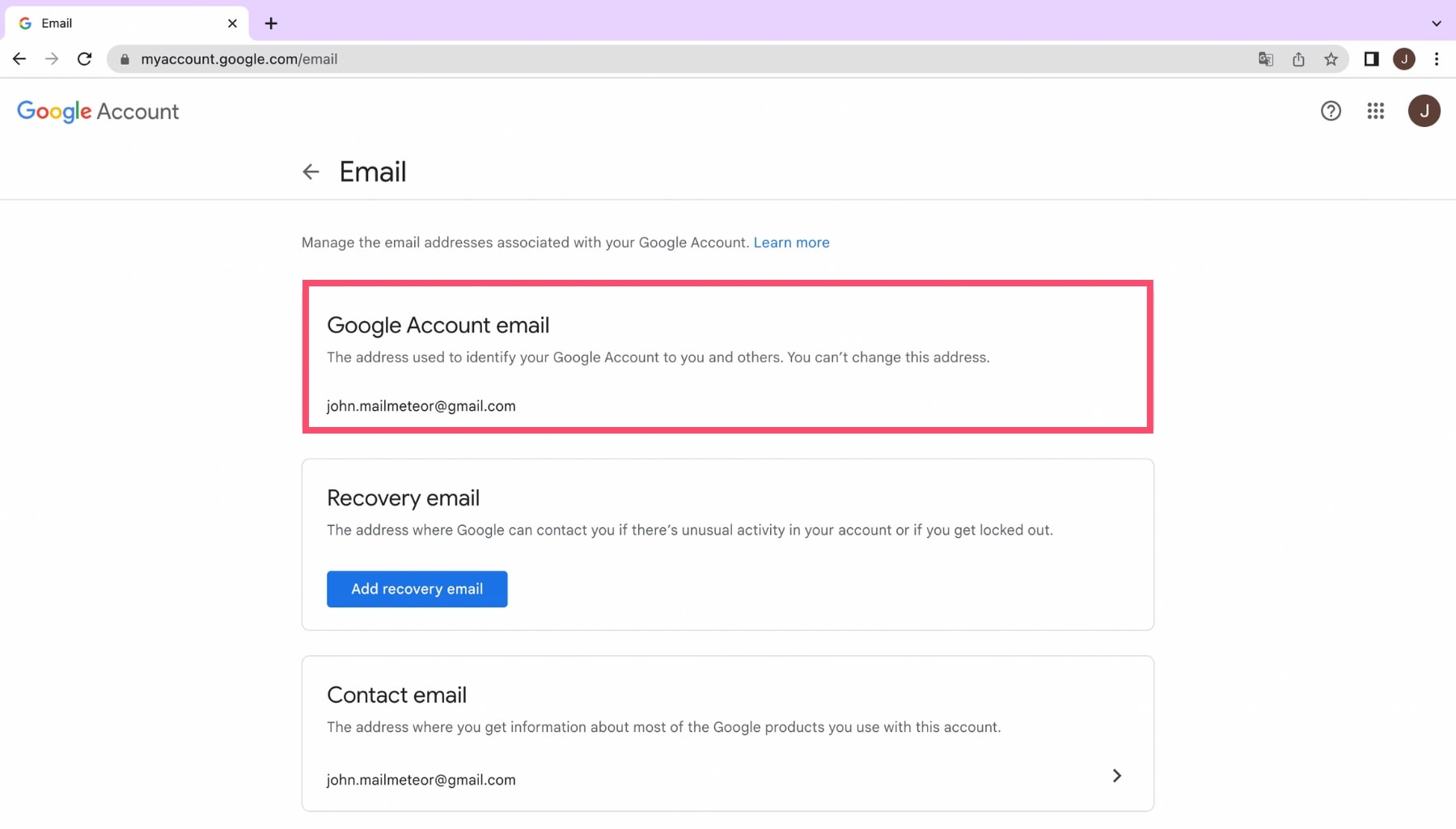
The implementation isn’t a simple database rename. Gmail’s backend infrastructure relies heavily on a distributed, sharded database architecture. A direct username change would require propagating that change across countless systems, introducing a significant risk of data inconsistency. Instead, Google is almost certainly employing a phased approach involving a new user ID mapping. When a user changes their username, the system creates a new internal identifier linked to the old one. Incoming emails are routed based on the new username, although the old username continues to function as an alias for a period, forwarding messages to the new address. This minimizes disruption and allows for a controlled rollout. The process likely leverages Google’s existing infrastructure for handling alias addresses, but with a crucial difference: the old username is eventually decommissioned, unlike a standard alias.
The transition also necessitates updates to Google’s account recovery systems. Traditionally, username was a key component of account verification. Now, Google will likely rely more heavily on multi-factor authentication (MFA) and recovery email addresses/phone numbers. This shift is a positive development, as it strengthens account security overall. It’s also worth noting the potential impact on Google Workspace accounts. While the initial rollout is focused on personal Gmail accounts, extending this functionality to Workspace will be crucial for enterprise adoption.
The Ecosystem Effect: Platform Lock-In and the Rise of Federated Identity
This change, while user-friendly, subtly reinforces Google’s ecosystem. While it makes Gmail more appealing, it also makes leaving more difficult. Users who have deeply integrated their Gmail address into various online services are now less likely to switch providers, even if a competitor offers superior features. This is a classic example of platform lock-in. However, the move also coincides with a broader industry trend towards OpenID Connect and other federated identity protocols. These protocols allow users to use a single identity provider (like Google) to log in to multiple websites and applications. Google’s decision could be interpreted as a strategic move to strengthen its position as a dominant identity provider in this emerging landscape.
“The ability to change a Gmail username is a long-overdue feature. It’s not just about convenience; it’s about giving users more control over their digital identity. However, it also subtly increases Google’s stickiness. The real question is whether Google will embrace fully decentralized identity solutions in the future.”
– Dr. Anya Sharma, CTO, SecureIdentity Solutions
Security Considerations: Phishing and Account Takeover
While the username change is generally positive, it introduces new security challenges. Phishing attacks could become more sophisticated, as attackers could impersonate users with newly changed usernames more easily. Google will need to implement robust fraud detection mechanisms to mitigate this risk. The transition period, where both the old and new usernames are active, creates a window of opportunity for account takeover attacks. Users should be vigilant about monitoring their account activity and enabling MFA. The system’s reliance on forwarding during the transition also introduces a potential vulnerability: a compromised forwarding rule could redirect sensitive emails to an attacker.
What This Means for Enterprise IT
For organizations heavily reliant on Gmail and Google Workspace, this change requires careful planning. IT administrators need to update internal documentation and training materials to reflect the new username change policy. They also need to ensure that any automated systems that rely on Gmail usernames are updated accordingly. The potential for confusion and disruption is significant, particularly in large organizations with complex IT infrastructures. A phased rollout, coupled with clear communication to employees, is essential.
The 30-Second Verdict
Gmail’s username change is a welcome improvement, but it’s not a revolution. It addresses a long-standing user frustration and subtly strengthens Google’s ecosystem. Security remains paramount, and users should exercise caution during the transition. The move signals a broader shift towards user empowerment, but also highlights the inherent tension between user control and platform lock-in.
The canonical URL for this announcement is Google’s official blog post. Further technical details on OpenID Connect can be found on the OpenID Connect website. For a deeper dive into distributed database architectures, see the CAP theorem paper by Eric Brewer.