Google’s Gemini Nano On-Device AI Faces Scrutiny After Security Researchers Demonstrate Prompt Injection Vulnerability
Google’s Gemini Nano, the on-device AI model powering features like Summarize in the Pixel 8 Pro, is under fire this week following demonstrations by security researchers showcasing a relatively straightforward prompt injection vulnerability. The flaw allows malicious actors to bypass intended safety protocols and manipulate the model’s output, raising concerns about the security of sensitive data processed locally on user devices. This isn’t a remote code execution issue, but a critical failure in input sanitization that highlights the challenges of deploying large language models (LLMs) in untrusted environments.
The core issue, as detailed in reports surfacing this week and initially demonstrated by researchers at NCC Group, centers around Gemini Nano’s susceptibility to crafted prompts that redefine the model’s internal instructions. Unlike cloud-based LLMs where Google maintains tighter control over the input pipeline, on-device models like Gemini Nano operate within the confines of the user’s device, making them inherently more vulnerable to local manipulation. The YouTube video circulating (and triggering Google’s automated defenses, ironically – link) illustrates how a carefully constructed prompt can force Gemini Nano to reveal its system instructions, effectively exposing its “jailbreak” points.
The Implications of Local LLM Vulnerabilities
This isn’t simply an academic exercise. Gemini Nano processes potentially sensitive information – summaries of emails, transcripts of voice recordings, and even snippets of photos. A successful prompt injection attack could theoretically allow an attacker to extract this data, or worse, manipulate the model to perform actions on behalf of the user without their knowledge. The fact that this is happening on-device, where traditional security sandboxes are less effective, is particularly alarming. The vulnerability isn’t about stealing the model itself, but about hijacking its *functionality*.
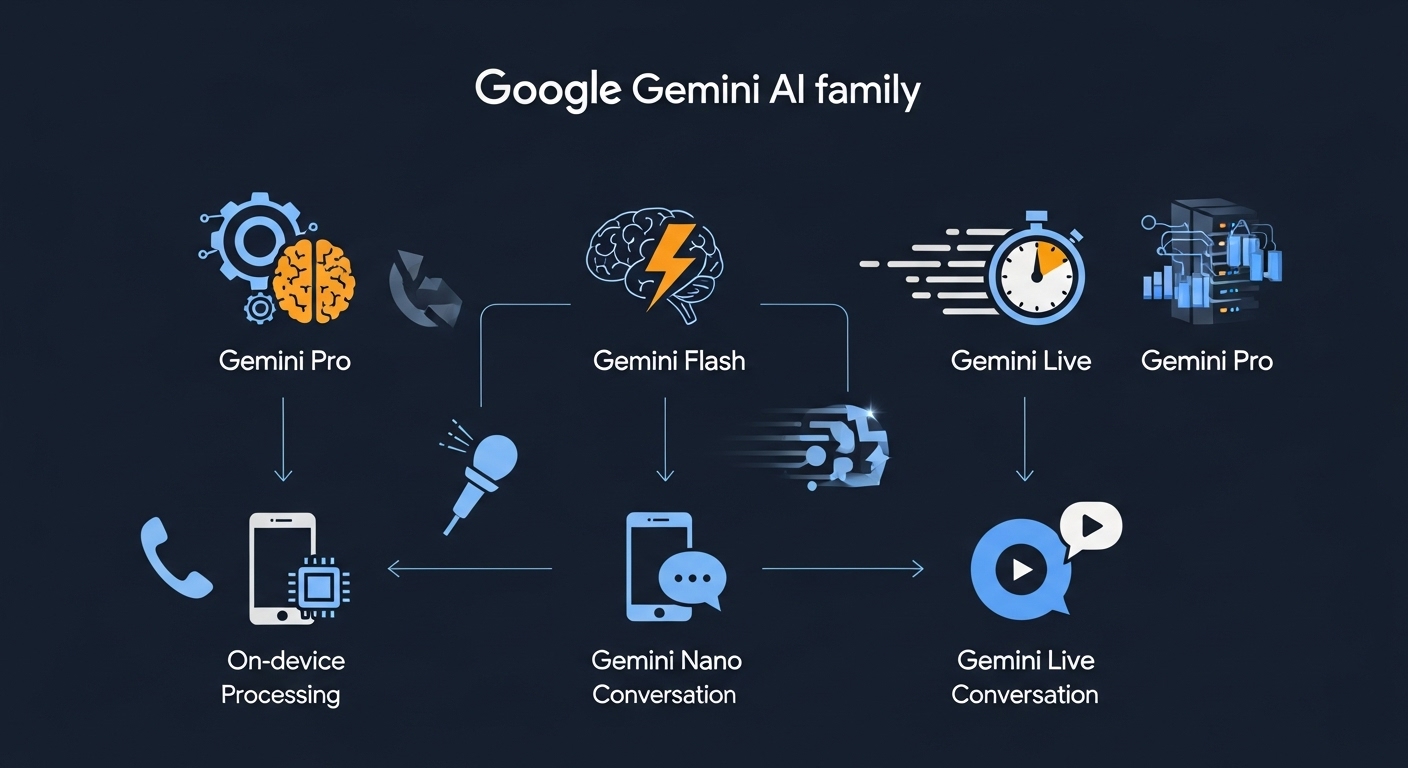
Architectural Considerations: Why Nano is Different
Gemini Nano, unlike its larger cloud-based siblings, is designed for extreme efficiency. It’s a quantized version of the Gemini family, meaning its parameters have been reduced to minimize computational requirements and memory footprint. This quantization, while crucial for on-device performance, appears to have approach at the cost of robust input validation. Larger models benefit from more complex safety layers and a greater capacity to recognize and reject malicious prompts. Nano’s streamlined architecture leaves it comparatively exposed. The model reportedly utilizes a 1.8 billion parameter architecture, a significant reduction from the larger Gemini models, which can exceed 100 billion parameters. This scaling down impacts its ability to generalize and defend against adversarial inputs.
The choice of architecture also plays a role. Gemini Nano leverages Google’s Tensor Processing Unit (TPU) architecture, optimized for matrix multiplication – the core operation in LLMs. However, the TPU’s focus on speed doesn’t inherently address security concerns. The on-device processing is handled by the Neural Processing Unit (NPU) within the Google Tensor G3 chip. The NPU’s efficiency is undeniable, but its security features are still maturing compared to established CPU/GPU security models.
What This Means for Enterprise IT
The vulnerability extends beyond individual users. Enterprises deploying Android devices with Gemini Nano-powered features must now reassess their security posture. The potential for data leakage and unauthorized actions is a significant concern, particularly in regulated industries. The incident underscores the need for robust Mobile Device Management (MDM) solutions that can monitor and control the behavior of on-device AI models.
“The rise of on-device AI is incredibly exciting, but it also introduces a new attack surface. We’re seeing a shift from focusing solely on cloud-based LLM security to understanding the unique vulnerabilities of these smaller, localized models. Input validation is paramount, but it’s clearly not enough. We need to explore techniques like differential privacy and federated learning to mitigate these risks.” – Dr. Anya Sharma, CTO, SecureAI Solutions.
The Broader Ecosystem: Open Source vs. Closed Gardens
This incident also reignites the debate surrounding open-source versus closed-source AI models. While Google’s Gemini Nano is a proprietary system, the open-source community is actively developing and refining LLMs with a strong emphasis on security. Projects like Llama 2 (Meta) and Mistral AI’s models benefit from the collective scrutiny of a global developer base, leading to faster identification and patching of vulnerabilities. The closed nature of Gemini Nano makes it more difficult for external researchers to independently assess its security. The reliance on Google’s internal security teams, while capable, inherently limits transparency.
the incident highlights the challenges of responsible AI development. Google’s emphasis on rapid feature deployment appears to have overshadowed the need for thorough security testing. The rush to integrate LLMs into consumer products has created a situation where vulnerabilities are discovered *after* deployment, rather than proactively addressed during the development lifecycle. This reactive approach is unsustainable in the long run.
API Access and Mitigation Strategies
Currently, direct API access to Gemini Nano is limited. It’s primarily accessed through Google’s native apps and services. However, as Google expands the availability of on-device AI capabilities to third-party developers, the risk of exploitation will increase. Developers will need to implement robust input validation and sanitization techniques to protect against prompt injection attacks. Google has released a security advisory outlining recommended mitigation strategies, including limiting the length and complexity of user prompts and implementing strict content filtering. Google’s Gemini Security Documentation provides further details.
One potential mitigation strategy involves employing a “guardrail” LLM – a smaller, dedicated model trained to identify and block malicious prompts before they reach Gemini Nano. This adds an extra layer of defense, but also introduces additional latency and computational overhead. Another approach is to leverage techniques like adversarial training, where the model is exposed to a diverse range of adversarial prompts during training to improve its robustness.
The Future of On-Device AI Security
The Gemini Nano vulnerability is a wake-up call for the industry. It demonstrates that on-device AI is not inherently secure and that significant investment is needed to address the unique security challenges it presents. The development of more robust input validation techniques, coupled with a greater emphasis on transparency and collaboration, is essential. The incident also underscores the importance of a layered security approach, combining proactive mitigation strategies with reactive incident response capabilities. NCC Group’s detailed analysis provides a comprehensive overview of the vulnerability and its implications. The ongoing “chip wars” and the push for localized AI processing will only intensify these security concerns. The race to deploy AI must not come at the expense of user safety and data privacy. Research on prompt injection attacks continues to evolve, highlighting the need for constant vigilance.
The 30-Second Verdict: Gemini Nano’s vulnerability isn’t a catastrophic flaw, but a critical reminder that on-device AI requires a fundamentally different security mindset. Expect Google to rapidly deploy patches and enhance its input validation mechanisms. The incident will likely accelerate the development of more secure on-device AI architectures.

