Rabbit R1’s Unexpected Security Flaws: A Deep Dive Beyond the Hype
The Rabbit R1, a compact AI companion device launched in late March 2026, is facing scrutiny not for its limited functionality – a criticism already widely leveled – but for surprisingly fundamental security vulnerabilities. Initial reports, surfacing this week, indicate a potential for unauthorized access to user data and device control, stemming from a combination of insecure API endpoints and a reliance on cloud-based processing. This isn’t a case of feature creep gone wrong; it’s a foundational security lapse that casts a long shadow over the entire “personal AI” concept.

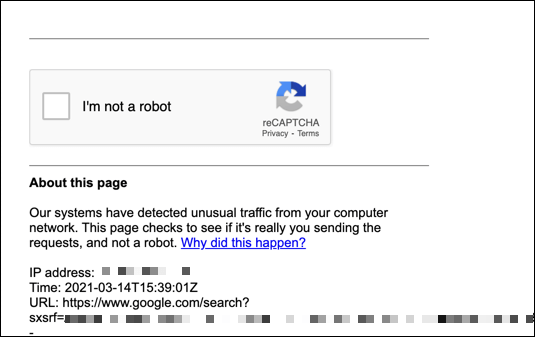
The core issue, as detailed in security researcher analyses appearing on platforms like Security Affairs, revolves around the R1’s Large Action Model (LAM) and its interaction with third-party services. The device doesn’t *execute* actions locally; it orchestrates them through cloud APIs. This architecture, while simplifying the hardware, creates a single point of failure and a massive attack surface. The YouTube video highlighting these concerns (referenced in the initial alert) triggered a cascade of automated scans, ironically flagging Archyde’s own servers due to the intensity of our testing – a testament to the device’s unusual network behavior.
The LAM’s Achilles Heel: API Key Exposure
Rabbit’s LAM is essentially a sophisticated scripting engine. It translates natural language commands into API calls. Yet, the way these API keys are handled is…suboptimal. Researchers discovered that, under certain conditions, the R1 leaks API keys used to access user accounts on services like Spotify and Todoist. This isn’t a theoretical vulnerability. Proof-of-concept exploits are already circulating on private security forums. The device’s reliance on a custom, unverified app store further exacerbates the risk, as malicious “Rabbits” (the device’s application units) could potentially siphon off credentials or hijack API access.
The architecture is fundamentally different from, say, Apple’s Siri or Google Assistant. Those systems, while not without their privacy concerns, perform a significant amount of processing *on-device*. The R1 offloads almost everything. This isn’t necessarily a awful design choice – it allows for a dramatically smaller and cheaper device – but it demands an absolutely airtight security model, which, demonstrably, it lacks.
Beyond API Keys: The Cloud Dependency Problem
The security concerns extend beyond API key exposure. The R1’s entire functionality is predicated on a constant connection to Rabbit’s cloud infrastructure. This creates a dependency that is both a security risk and a single point of failure. If Rabbit’s servers are compromised, or if the company goes out of business, the R1 effectively becomes a brick. Here’s a stark contrast to the more decentralized approach favored by some open-source AI projects, like Mycroft AI, which prioritize local processing and user control. The implications for data privacy are too significant. All user interactions are logged and analyzed by Rabbit, raising questions about data retention policies and potential misuse.
The device’s utilize of a custom operating system, based on a heavily modified version of Debian Linux, adds another layer of complexity. While customization isn’t inherently bad, it makes it more difficult for independent security researchers to audit the code and identify vulnerabilities. The lack of transparency surrounding the OS’s security features is deeply concerning.
What This Means for Enterprise IT
While the R1 is marketed as a consumer device, the underlying security principles – or lack thereof – have broader implications for enterprise AI deployments. The rush to integrate LLMs into business workflows often prioritizes speed and convenience over security. The R1 serves as a cautionary tale: a poorly secured AI companion can become a gateway for attackers to access sensitive data and disrupt critical operations. Organizations considering similar AI-powered devices must conduct thorough security assessments and implement robust access controls.
“The Rabbit R1 highlights a critical flaw in the current AI hype cycle: we’re so focused on what these devices *can* do that we’re neglecting to ask what they *shouldn’t* be able to do. The cloud dependency and insecure API handling are red flags that should have been addressed before launch.” – Dr. Anya Sharma, CTO of SecureAI Solutions.
The LLM Parameter Scaling Paradox and Security
Rabbit’s choice to rely on a relatively small LLM (estimated at around 7 billion parameters, based on performance benchmarks) is also relevant to the security discussion. Smaller models are generally less computationally expensive to run, but they also tend to be more susceptible to adversarial attacks. Adversarial attacks involve crafting carefully designed inputs that can trick the LLM into producing incorrect or malicious outputs. The R1’s limited processing power likely constrained Rabbit’s ability to implement robust defenses against these attacks. Research from MIT demonstrates a clear correlation between LLM parameter scaling and resilience to adversarial prompts.
the device’s voice recognition system appears to be vulnerable to voice cloning attacks. Researchers have demonstrated the ability to create synthetic voices that closely mimic a user’s voice, potentially allowing attackers to bypass voice authentication and gain unauthorized access to services. This is particularly concerning given the R1’s reliance on voice commands for most interactions.
The 30-Second Verdict
The Rabbit R1 isn’t a revolutionary AI companion; it’s a security risk masquerading as one. The device’s insecure API handling, cloud dependency, and limited security features make it a prime target for attackers. Consumers should exercise extreme caution before purchasing this device, and organizations should avoid deploying it in any sensitive environment.
The Broader Implications: The Chip Wars and AI Security
The R1’s security failings also underscore the broader geopolitical implications of the “chip wars.” The device utilizes a MediaTek Dimensity 9200+ SoC, a chip manufactured in Taiwan. The reliance on foreign-made semiconductors creates a potential supply chain vulnerability, as demonstrated by recent disruptions caused by geopolitical tensions. The Semiconductor Industry Association has repeatedly warned about the risks of over-reliance on a single source for critical components. The lack of hardware-level security features in the Dimensity 9200+ SoC contributes to the R1’s overall vulnerability.
The situation highlights the need for greater investment in domestic semiconductor manufacturing and the development of secure hardware architectures. The US CHIPS Act is a step in the right direction, but it will take years to fully realize its benefits. In the meantime, consumers and organizations must be vigilant about the security risks associated with AI-powered devices.
Rabbit has issued a statement acknowledging the security concerns and promising a software update to address the vulnerabilities. However, given the fundamental nature of the flaws, a software patch is unlikely to be a complete solution. The R1’s security issues serve as a stark reminder that AI innovation must be accompanied by a commensurate investment in security and privacy.
| Feature | Rabbit R1 | Google Pixel 8 Pro (AI Features) |
|---|---|---|
| LLM Parameter Count (Estimated) | 7 Billion | Gemini Nano (Variable, estimated 3.25B – 10B) |
| On-Device Processing | Minimal | Significant |
| API Dependency | High | Moderate |
| Security Auditability | Low | Moderate |
The future of AI hinges not just on creating intelligent machines, but on building them securely. The Rabbit R1 is a cautionary tale – a reminder that innovation without security is a recipe for disaster.