Artemis I Crew Awaits Lunar Transfer: A Deep Dive into the Mission’s Technological Underpinnings
As of today, April 2nd, 2026, the Artemis I crew is in a stable Earth orbit, poised to initiate the trans-lunar injection burn that will send them on a trajectory towards the Moon. This isn’t merely a repeat of Apollo; it’s a complex orchestration of modern rocketry, advanced computing, and a renewed focus on deep-space communication – all underpinned by a surprisingly fragile cybersecurity landscape. The mission’s success hinges not just on the SLS rocket’s performance, but on the integrity of the software controlling every aspect of the journey, from navigation to life support.
The significance of Artemis I extends far beyond symbolic national pride. It’s a proving ground for technologies critical to establishing a sustained lunar presence, and, crucially, a testbed for the infrastructure needed for future missions to Mars. The data gathered during this flight will inform the development of everything from radiation shielding to closed-loop life support systems, and will validate the operational concepts for long-duration spaceflight.
The Orion Crew Vehicle: Beyond the Heat Shield
Much of the public focus has been on the Space Launch System (SLS) rocket, but the Orion crew vehicle is where the human element resides. Orion’s avionics suite, built around a radiation-hardened Lockheed Martin-developed system, relies on a distributed architecture with multiple redundant processors. This isn’t your typical automotive-grade redundancy; the processors are specifically designed to withstand the cumulative effects of cosmic radiation, a significant challenge in deep space. The core processing is handled by a PowerPC-based system, but increasingly, newer modules are incorporating ARM-based processors for specific tasks, leveraging their power efficiency. This hybrid approach is a pragmatic compromise between established reliability and the benefits of modern chip design.
But, the shift to ARM introduces new attack vectors. While radiation hardening mitigates some risks, it doesn’t address software vulnerabilities. The increased complexity of modern software stacks, including the real-time operating system (RTOS) and the various application layers, creates a larger surface area for potential exploits. The reliance on C and C++ for critical systems likewise presents inherent memory safety challenges.
Navigating the Lunar Gateway: The Role of Deep Space Network (DSN) and Secure Communications
Once in lunar orbit, the Artemis I crew will rely heavily on the Deep Space Network (DSN) for communication with mission control. The DSN, a network of massive radio antennas located around the globe, provides the crucial link for telemetry, command, and data transfer. But this reliance also introduces a single point of failure, and a potential target for disruption.
The Artemis missions are employing a new generation of secure communication protocols, leveraging elliptic-curve cryptography (ECC) for key exchange and digital signatures. This is a significant improvement over the older Diffie-Hellman key exchange algorithms, offering stronger security with shorter key lengths. However, the implementation of these protocols is critical. A flawed implementation can render even the strongest cryptography vulnerable. The sheer latency of deep-space communication – several seconds round trip – makes real-time intrusion detection and response extremely difficult.
“The biggest challenge isn’t necessarily breaking the encryption, it’s exploiting vulnerabilities in the software that *uses* the encryption. A buffer overflow in a telemetry parsing routine could provide an attacker with a foothold, even if the data itself is encrypted.” – Dr. Anya Sharma, Cybersecurity Analyst, Stellar Cybernetics.
The Lunar Gateway and the Emerging Space-Based Cybersecurity Threat
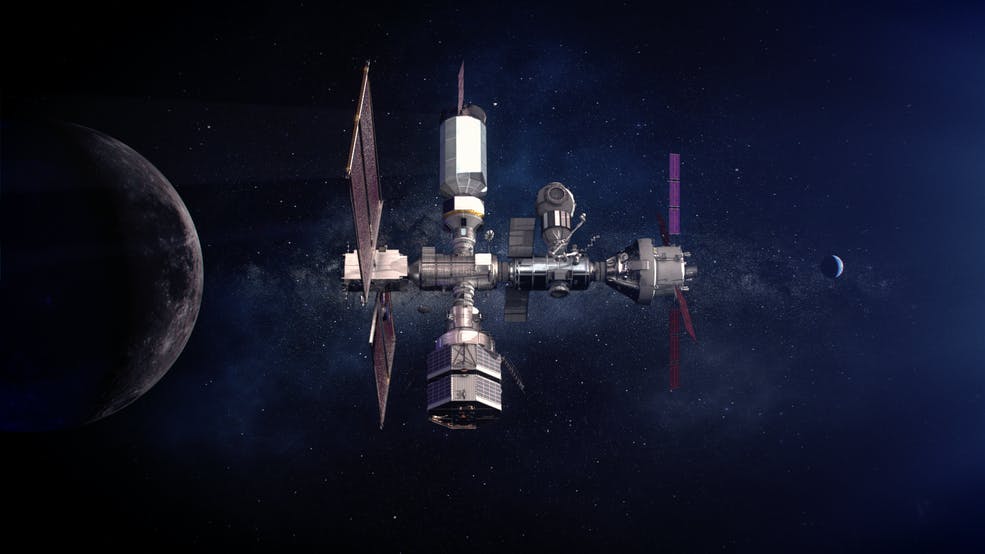
The planned Lunar Gateway, a small space station orbiting the Moon, will serve as a staging point for future lunar landings and a hub for scientific research. However, the Gateway also represents a new and potentially vulnerable node in the space infrastructure. Its reliance on interconnected systems – power generation, life support, communication, and navigation – creates a complex attack surface.
The increasing commercialization of space is exacerbating this threat. Private companies are developing and operating satellites, lunar landers, and other space-based assets, often with limited cybersecurity expertise. This creates opportunities for malicious actors to exploit vulnerabilities in these systems, potentially disrupting critical space services or even gaining control of valuable assets. The potential for kinetic attacks – physically damaging satellites or other space infrastructure – is also a growing concern.
API Access and the Open-Source Ecosystem: A Double-Edged Sword
NASA is increasingly embracing open-source software and providing APIs for accessing mission data. This is a positive trend, fostering innovation and collaboration. However, it also introduces new security risks. Open-source code is subject to public scrutiny, which can help identify vulnerabilities, but it also makes it easier for attackers to find and exploit them.
The APIs themselves must be carefully designed and secured. Rate limiting, authentication, and authorization are essential to prevent abuse. The data returned by these APIs must be sanitized to prevent injection attacks. The use of OWASP’s Top Ten vulnerabilities is a constant concern.
The Artemis program’s reliance on the ROS (Robot Operating System) framework for robotic missions is a prime example. While ROS provides a powerful and flexible platform for developing robotic applications, it also has known security vulnerabilities. NASA is working to address these vulnerabilities, but the open-source nature of ROS means that new vulnerabilities are constantly being discovered.
What This Means for Enterprise IT
The cybersecurity challenges faced by the Artemis program are not unique to space. Many of the same vulnerabilities – complex software stacks, reliance on open-source code, and the increasing threat of sophisticated attacks – are also present in enterprise IT environments. The lessons learned from Artemis can inform the development of more secure systems on Earth.
The 30-Second Verdict
Artemis I is a technological marvel, but its success depends on more than just powerful rockets and advanced spacecraft. A robust cybersecurity posture is essential to protect the mission from disruption and ensure the safety of the crew. The program’s vulnerabilities highlight the growing importance of cybersecurity in the space domain, and the need for a proactive and comprehensive approach to security.
The current mission is a critical stepping stone, but the real test will come with the Lunar Gateway and the establishment of a sustained lunar presence. The stakes are high, and the consequences of failure could be catastrophic. The future of space exploration depends on our ability to secure the digital frontier.
| Component | Radiation Hardness | Processor Architecture | Key Security Features |
|---|---|---|---|
| Orion Avionics | High (Radiation-Hardened) | PowerPC & ARM | ECC, Redundant Processors, Secure Boot |
| Deep Space Network | N/A (Ground-Based) | Various | Encryption, Authentication, Physical Security |
| Lunar Gateway Systems | Moderate (Shielding) | ARM & x86 | Firewalls, Intrusion Detection, Secure APIs |
“We’re seeing a convergence of terrestrial and space-based cybersecurity threats. The same actors who target critical infrastructure on Earth are now turning their attention to space, recognizing its strategic importance.” – Marcus Chen, CTO, Orbital Defense Systems.

