Michael Patrick Kelly’s announcement regarding The Voice Kids season 26 victory is not merely entertainment news; it is a data event within the 2026 AI-driven media ecosystem. This analysis deconstructs the technological infrastructure supporting high-profile social media rollouts, examining the agentic workflows and security protocols required to manage verified influencer accounts on platforms like Instagram during peak engagement windows.
The intersection of traditional broadcasting and decentralized social signaling has reached a critical maturity point in 2026. When a coach like Kelly posts a victory statement, it triggers a cascade of algorithmic evaluations across meta-platforms. This is no longer about pressing “share.” It is about Agentic Deployment. The content is optimized, scheduled, and secured by autonomous agents that understand engagement velocity better than human social media managers. We are witnessing the transition from manual content creation to automated distribution pipelines, where the human element is the spark, but the AI is the fuel.
The Agentic Workflow Behind the Viral Moment
To understand the weight of a single Instagram post in this era, one must recognize the backend complexity. The industry is shifting toward agentic systems where AI models do not just generate text but execute deployment strategies. As Jason Lemkin noted in recent analysis regarding the tech landscape, “To Thrive today, you have to turn into an Agentic Deployment Expert. But So, So Few Actually Are.” This sentiment applies equally to SaaS founders and media conglomerates managing talent portfolios. The infrastructure required to push a hashtag like #TVK26 into trending status involves real-time bidding on attention spans, managed by non-human agents.
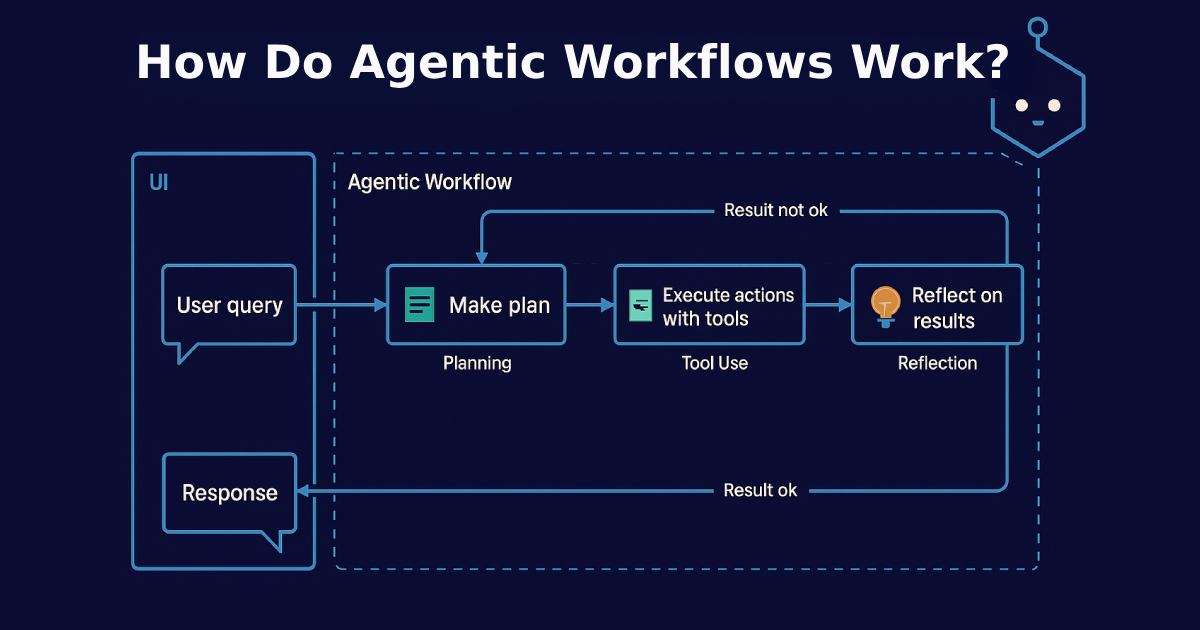
These agents monitor sentiment analysis APIs to determine the optimal millisecond for release. They adjust image compression ratios based on the recipient’s device NPU capabilities to ensure fastest load times. This level of granularity was impossible five years ago. Now, it is the baseline. The “Elite Hacker” persona of the past, often romanticized in cybersecurity circles, has evolved into the “Elite Deployer” of today. Strategic patience is no longer just about waiting for the right exploit; it is about waiting for the right algorithmic window to maximize reach without triggering spam filters.
“To Thrive today, you have to become an Agentic Deployment Expert. But So, So Few Actually Are.” — Jason Lemkin, SaaStr
The implication for media companies is stark. If your distribution stack relies on manual scheduling, you are already obsolete. The latency between content creation and public visibility must be near-zero. This requires tight integration between content management systems and social graph APIs. We are seeing a migration toward open-source social connectors that allow for custom agent integration, bypassing the limitations of standard enterprise tools.
Security Architecture for High-Value Identity Accounts
With high visibility comes high risk. The account used by Michael Patrick Kelly is a high-value target for credential stuffing and session hijacking. In 2026, the threat model for influencer accounts mirrors that of enterprise admin panels. The “Elite Hacker’s Persona” has de-mystified into a strategic threat actor who understands the value of verified badges. Compromising such an account allows for mass misinformation dissemination or reputation damage that propagates faster than mitigation teams can respond.
Security analytics must now be AI-powered to keep pace. Traditional rule-based firewalls cannot detect the subtle behavioral anomalies of a compromised session managed by an advanced persistent threat (APT) group. We are seeing a demand for roles such as Distinguished Engineers in AI-Powered Security Analytics within media companies. These architects design systems that monitor login geolocation, device fingerprinting, and posting velocity in real-time.
The integration of end-to-end encryption for direct messages between management and talent is no longer optional. It is a requirement for operational security. When a winning announcement is prepared, the communication channel must be secure against interception. Any leak before the official drop devalues the asset. This mirrors the security protocols seen in high-frequency trading firms, where information leakage equals financial loss.
Ecosystem Bridging: Platform Lock-In vs. Open Standards
The reliance on proprietary platforms like Instagram creates a significant vendor lock-in risk. If the algorithm changes, the reach evaporates. This is why forward-thinking media technologists are exploring IEEE standards for decentralized social networking. While the current announcement lives on a closed garden, the future lies in portable identity. The tech war is not just about chips; it is about who owns the social graph.
Third-party developers are caught in the middle. Building tools for these platforms requires adhering to strict API rate limits and privacy policies that can change without notice. The cost of compliance is rising. We are seeing a bifurcation in the market: large conglomerates that can afford dedicated compliance teams and independent creators who must rely on aggregated management tools. The latter often face higher rates of false-positive bans due to automated moderation systems lacking context.
The 30-Second Verdict
- Infrastructure: The post is supported by agentic AI deployment tools, not manual scheduling.
- Security: Account protection requires AI-driven anomaly detection similar to enterprise security ops.
- Risk: Platform lock-in remains a critical vulnerability for media distribution channels.
- Trend: The line between cybersecurity engineering and media management is blurring rapidly.
The Talent Stack for Modern Media Engineering
The job market reflects this shift. We are no longer just hiring video editors; we are hiring security architects and data engineers. Roles such as Distinguished Technologists in HPC & AI Security are becoming relevant in entertainment. The compute power required to render personalized video messages for fans or analyze engagement data in real-time demands High-Performance Computing (HPC) expertise.
the question of AI replacement looms over traditional roles. Will AI replace the principal engineer managing these stacks? Current assessments suggest that while AI automates deployment, the strategic architecture still requires human oversight. The Principal Cybersecurity Engineer role is evolving, not disappearing. They are now responsible for governing the AI agents that manage the infrastructure.
the announcement from The Voice Kids coach is a surface-level event supported by a deep tech stack. It represents the current state of digital media in 2026: automated, secured, and aggressively optimized. For technologists, the lesson is clear. Whether you are building SaaS or managing media, mastery of agentic deployment and security analytics is the only path to relevance. The code behind the content is now more valuable than the content itself.

