Microsoft has officially deprecated offline activation for Windows 10 and 11, mandating an internet connection for license validation. This shift moves the OS from a static, hardware-bound validation model to a dynamic, cloud-verified entitlement system, aimed at reducing piracy and streamlining the digital distribution of licenses.
Let’s be clear: this isn’t about “user convenience.” That’s the corporate gloss. From a systems architecture perspective, this is a strategic pivot toward an Account-Based Licensing (ABL) model. By killing the “phone-in” or manual key entry methods that didn’t require a handshake with a Microsoft server, Redmond is effectively turning your operating system into a subscription-adjacent service, even if you paid for a “lifetime” retail key.
For the average user, this is a minor annoyance. For the enterprise admin managing air-gapped systems or the privacy-conscious enthusiast running a clean x86 install on legacy hardware, it’s a digital fence being slammed shut.
The Death of the Static Key and the Rise of Cloud Entitlement
Historically, Windows activation relied on a combination of a Product Key and a Hardware ID (HWID). The HWID is a unique fingerprint generated from your motherboard, CPU, and MAC address. In the old “offline” world, you could theoretically validate a license via a phone system that used an Installation ID (IID) and a Confirmation ID (CID)—a primitive but effective asynchronous handshake.
By removing this, Microsoft is migrating the “source of truth” from the local registry to the Azure-backed activation servers. This allows Microsoft to implement real-time telemetry on license usage. They can now detect “key leakage” (when a single retail key is used across a thousand machines) in milliseconds rather than months.
It’s a move toward Platform Lock-in. By tethering the OS activation to a Microsoft Account (MSA), the operating system becomes a gateway to the wider ecosystem—OneDrive, Office 365, and the burgeoning AI Copilot integration. You aren’t just activating a kernel; you’re onboarding into a data-harvesting funnel.
The Technical Fallout for Air-Gapped Environments
The “Information Gap” in Microsoft’s official explanation is the total omission of air-gapped security. In high-security sectors—defense, nuclear, or critical infrastructure—machines are physically isolated from the internet to prevent exfiltration and zero-day exploits. Mandating an internet connection for activation creates a paradoxical security risk: you must either compromise your air-gap to activate the OS or run an “unactivated” version that periodically nags the user and restricts personalization.
- The HWID Conflict: When you swap a motherboard in an offline environment, the HWID changes. Without a manual override, the OS marks itself as non-genuine.
- The Latency Loop: Cloud activation introduces a dependency on DNS resolution and HTTPS handshakes. If the activation server is unreachable, the “Genuine Windows” check can trigger system-level warnings.
- Registry Persistence: Even with online activation, the
Software\Microsoft\Windows NT\CurrentVersion\DigitalProductIDkey remains, but it is now a pointer to a cloud token rather than a standalone proof of purchase.
Bridging the Gap: The Cybersecurity Perspective
From a security standpoint, this shift is a double-edged sword. On one hand, cloud-based validation makes it harder for “KMS Pico” style activators to spoof local licenses without being detected by the OS’s internal integrity checks. It creates a centralized point of failure. If the activation API experiences a global outage, new deployments worldwide grind to a halt.
“The transition to mandatory online activation is less about piracy and more about telemetry. By forcing a cloud handshake, Microsoft transforms the OS from a product into a persistent connection. This is the ‘SaaS-ification’ of the desktop.”
This mirrors the broader trend in the “Chip Wars” and software architecture. Just as ARM-based Windows laptops are pushing for tighter integration between hardware and cloud identity, the software layer is being stripped of its autonomy. We are seeing the end of the “standalone PC” era.
The 30-Second Verdict: Who Wins?
Microsoft wins. They gain a 100% capture rate of user identities and a real-time map of every active installation of Windows 11. The user loses the “right to be offline.” The only winners in the community are the developers of open-source activation scripts on GitHub, who will see a surge in traffic as users seek “digital license” workarounds to bypass the mandatory login.
The Architecture of Control: Comparing Activation Methods
To understand the gravity of this shift, we have to look at the mechanical difference between how Windows used to be validated versus the new mandated flow.
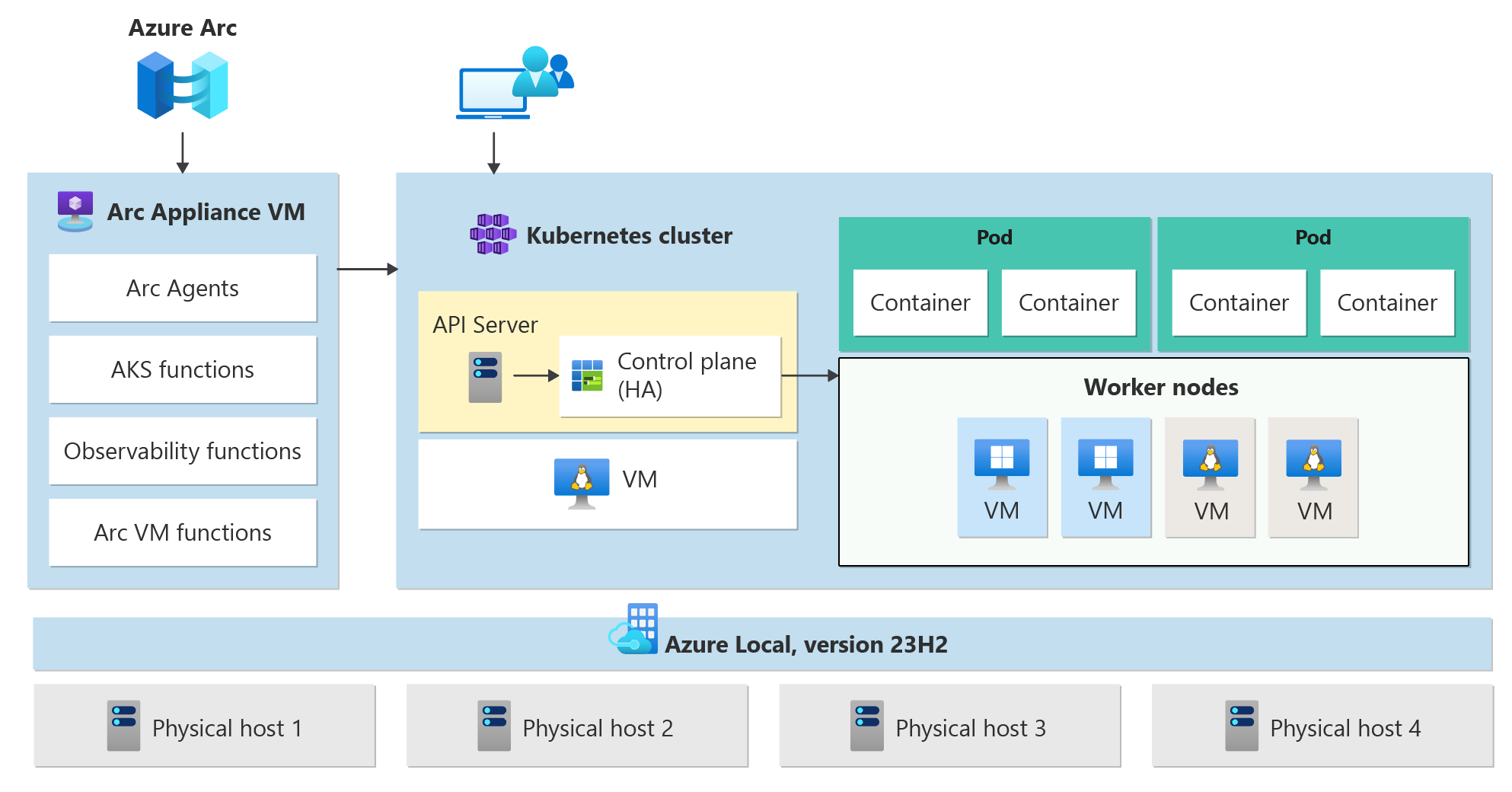
| Feature | Legacy Offline Activation | Modern Cloud Activation (2026) |
|---|---|---|
| Validation Source | Local Registry / Phone Server | Azure Activation API |
| Identity Link | Hardware ID (HWID) | Microsoft Account (MSA) / HWID |
| Air-Gap Support | Full (via Manual CID) | None (Official) |
| Telemetry | Periodic / Optional | Real-time / Mandatory |
| Recovery | Key-based reinstall | Account-based cloud recovery |
Final Analysis: The Strategic Pivot
This isn’t a bug; it’s a feature of the new corporate roadmap. By eliminating the offline path, Microsoft is preparing for a future where the OS is an AI-driven service. You cannot run a local LLM-integrated OS effectively if the system doesn’t realize exactly who you are and whether your subscription is current.
If you are an enterprise architect, start looking into KMS (Key Management Service) or Active Directory Based Activation (ADBA) for your internal networks. These are the only remaining “semi-offline” lifelines for professional environments. For the home user? Welcome to the cloud. Whether you like it or not, your Windows license is no longer a piece of property you own—it’s a permission slip granted by a server in Redmond.
The “Strategic Patience” of the elite tech user now involves deciding whether to migrate to a more open ecosystem or to spend their weekends tinkering with registry bypasses. In the war between local autonomy and cloud convenience, the cloud just won another decisive battle.