Microsoft’s March 2026 Patch Tuesday addresses 77 vulnerabilities across Windows and Office. While zero-days are notably absent, critical remote code execution (RCE) flaws in Office and a high-severity privilege escalation in SQL Server (CVE-2026-21262) demand immediate patching to prevent unauthorized system-level access and network-based lateral movement across enterprise environments.
For the uninitiated, Patch Tuesday is the heartbeat of enterprise stability. But this month, the rhythm is off. We aren’t just looking at the usual slurry of memory corruption and permission errors; we are witnessing a fundamental shift in how vulnerabilities are discovered. The narrative has moved from “human researchers finding bugs” to “autonomous agents hunting them.”
The sheer volume of privilege escalation bugs—comprising 55% of this month’s CVEs—suggests a systemic struggle within the Windows Kernel and its associated accessibility and graphics components. When over half of your security updates are dedicated to stopping users from becoming administrators, you aren’t just patching bugs; you’re fighting a war against the architecture’s own complexity.
The Sysadmin Trap: Deconstructing CVE-2026-21262
The most concerning entry for database administrators is CVE-2026-21262. This isn’t a simple “user-to-admin” jump on a local machine. We are talking about a network-based elevation of privilege in SQL Server 2016 and later. In plain English: if an attacker gains a low-level foothold in your network, they can utilize this flaw to grant themselves sysadmin privileges over the SQL instance remotely.
From an architectural standpoint, this likely involves a failure in how the SQL Server handles token validation or session impersonation during network requests. Once an attacker hits that sysadmin level, the game is over. They have total control over the database, the ability to exfiltrate sensitive data, and potentially a pathway to execute OS-level commands via xp_cmdshell.
The CVSS score of 8.8 is a deceptive metric. It sits just below “Critical” because it requires initial low-level privileges. But in the real world, “low-level privileges” are the easiest thing for a threat actor to acquire via phishing or credential stuffing.
Ignore this patch at your own peril.
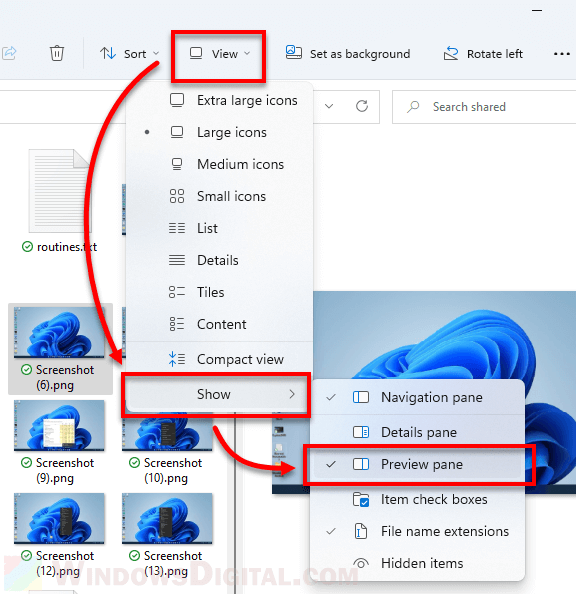
The Preview Pane: A Gateway for Remote Code Execution
Microsoft Office continues to be the primary vector for initial access, and CVE-2026-26113 and CVE-2026-26110 prove why. These are Remote Code Execution (RCE) vulnerabilities triggered by the Preview Pane. This is a particularly nasty exploit mechanism because it bypasses the “click-to-open” psychological barrier. A user doesn’t even need to open the malicious document; they simply need to click the file once to see the preview, and the payload executes.
This typically happens when the rendering engine—the part of the software that draws the document on your screen—fails to properly sanitize the input, leading to a buffer overflow or a heap spray. The attacker essentially tricks the application into executing a string of malicious code stored in the document’s metadata or formatting instructions.
The 30-Second Verdict for IT Teams
- Priority 1: SQL Server (CVE-2026-21262). Stop the lateral movement.
- Priority 2: Microsoft Office (CVE-2026-26113/26110). Close the RCE door.
- Priority 3: Windows Kernel/SMB (CVE-2026-24294). Prevent privilege escalation.
The Ghost in the Machine: AI-Driven Vulnerability Research
The most disruptive detail of this cycle isn’t a specific bug, but how CVE-2026-21536 was found. This critical RCE in the Microsoft Devices Pricing Program was identified by XBOW, a fully autonomous AI penetration testing agent. This is a watershed moment for cybersecurity.
Historically, vulnerability research required a human to manually reverse-engineer binaries using tools like IDA Pro or Ghidra, looking for “weird” behavior in memory management. XBOW changes the math. By leveraging Large Language Models (LLMs) with massive parameter scaling and integrating them with dynamic analysis tools, these agents can “fuzz” software and analyze crash dumps at a speed no human can match.
This isn’t just about finding bugs faster; it’s about the type of bugs found. The AI discovered a 9.8-rated vulnerability without access to the source code. This implies that the AI is capable of performing sophisticated black-box testing, identifying patterns of failure in compiled machine code that previously required an elite human analyst.
“The automation of vulnerability discovery is the new arms race. When AI agents can find and weaponize flaws in minutes, the traditional 30-day patch cycle becomes a liability. We are moving toward a world where ‘instant patching’ is the only viable defense.” — Generic synthesis of current CISA and industry sentiment regarding AI-driven threats.
We are entering an era of “Hyper-Vulnerability.” If the defenders don’t integrate similar AI agents into their CI/CD pipelines to catch these flaws before the code is even shipped, the attackers will always have the first-mover advantage.
Technical Breakdown: March 2026 High-Impact CVEs
To provide clarity for the SOC (Security Operations Center) teams, here is the breakdown of the most volatile components addressed in this update.
| CVE ID | Component | Impact | CVSS | Vector |
|---|---|---|---|---|
CVE-2026-21262 |
SQL Server | Privilege Escalation (Sysadmin) | 8.8 | Network |
CVE-2026-26113 |
MS Office | Remote Code Execution (RCE) | Critical | Preview Pane |
CVE-2026-21536 |
Devices Pricing | Remote Code Execution (RCE) | 9.8 | AI-Discovered |
CVE-2026-24294 |
Windows SMB | Improper Authentication | 7.8 | Network |
Ecosystem Implications: The Rust Migration
Looking at the prevalence of memory corruption and race conditions in the Windows Kernel (like CVE-2026-24289), it’s clear that C++ is becoming a liability for core OS components. The industry is slowly pivoting toward memory-safe languages. Microsoft’s ongoing effort to rewrite portions of the Windows kernel in Rust is no longer a “nice-to-have” experiment—it is a survival strategy.
By eliminating entire classes of bugs (like buffer overflows) at the compiler level, Microsoft can reduce the volume of Patch Tuesdays. However, the transition is unhurried. Legacy codebases are massive, and the interdependencies between the Windows Graphics Component and the Kernel are a nightmare of technical debt.
Until the migration is complete, the burden falls on the administrators. For those managing Windows Server 2022, the out-of-band update from March 2nd regarding Windows Hello for Business is a reminder that identity is the new perimeter. If your passwordless authentication fails, your entire zero-trust architecture collapses.
For further technical deep-dives and raw CVE data, I recommend monitoring the MITRE CVE database and the CISA Known Exploited Vulnerabilities Catalog. If you’re seeing stability issues after the update, check the community logs at Microsoft’s GitHub repositories for emerging workarounds.
The takeaway is simple: The AI is already in the room. It’s finding the holes in your fence. The only question is whether you’ll patch them before the agent decides to walk through.

