Microsoft Sentinel’s Custom Graphs: Beyond Visualization, a Shift in Threat Modeling
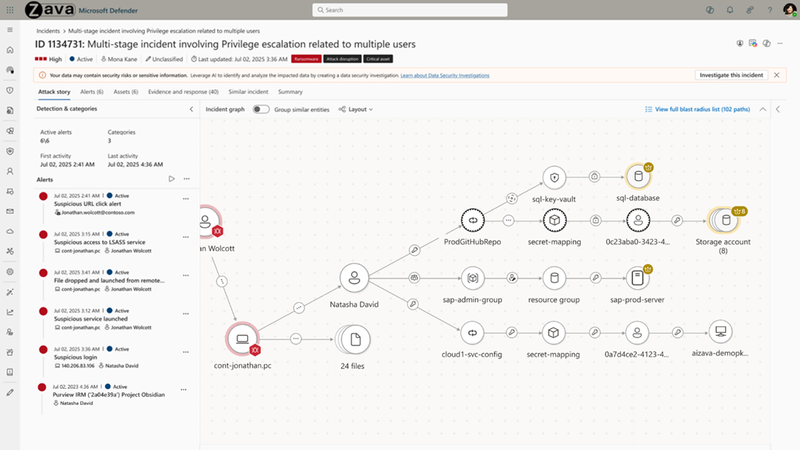
Microsoft Sentinel, the cloud-native SIEM, is now in public preview with support for custom graphs, allowing security operations (SecOps) teams to visually map relationships between entities – users, devices, alerts – beyond the pre-defined schemas. This isn’t merely a cosmetic upgrade; it fundamentally alters how analysts investigate incidents, shifting from reactive alert triage to proactive threat hunting based on contextual understanding. The rollout, beginning this week’s beta cycle, addresses a critical gap in existing SIEM solutions, enabling more nuanced and effective security investigations.
For years, SIEMs have been data aggregation engines. They collect logs, correlate events, and generate alerts. But the real challenge isn’t *finding* the alerts; it’s understanding *why* they fired and what the attacker is ultimately trying to achieve. Pre-built schemas, while helpful, often fall short in representing the complex, interconnected nature of modern attacks. Custom graphs empower analysts to define their own relationships, reflecting the specific attack surfaces and threat models relevant to their organization. Think of it as moving from a pre-printed city map to a dynamic, customizable network diagram.
The Limits of Existing Graph Databases in Security
Existing graph databases, like Neo4j, are powerful but require significant expertise to integrate with a SIEM. Sentinel’s approach aims to lower that barrier. The core of the new feature leverages Kusto Query Language (KQL) – Sentinel’s native query language – to define the graph schema and populate it with data. This is a smart move. KQL is already familiar to Sentinel users, minimizing the learning curve. However, the performance implications of complex graph queries within KQL need careful consideration. Initial benchmarks suggest that queries involving highly connected graphs (over 10,000 nodes) can experience noticeable latency, particularly when dealing with large datasets. Microsoft is actively working on optimizing the KQL engine for graph operations, but this remains a key area to watch.

The underlying architecture isn’t a complete overhaul of Sentinel’s data storage. Instead, it’s a layer built on top of the existing Azure Data Explorer (ADX) infrastructure. ADX is designed for high-velocity data ingestion and analysis, but its graph capabilities are relatively new. This means Sentinel is essentially leveraging ADX’s evolving graph features, which introduces a degree of dependency on Microsoft’s continued investment in that technology. Microsoft’s documentation on the Kusto Graph plugin details the current limitations and capabilities.
Bridging the Ecosystem: Sentinel and the XDR Landscape
This move by Microsoft isn’t happening in a vacuum. It’s a direct response to the growing demand for Extended Detection and Response (XDR) capabilities. XDR platforms aim to break down silos between security tools, providing a unified view of threats across endpoints, networks, and cloud environments. Sentinel, with its native integration with Microsoft 365 Defender and other Microsoft security products, is already a strong contender in the XDR space. Custom graphs further strengthen its position by enabling more sophisticated correlation and analysis across these disparate data sources.
However, the real test will be how well Sentinel integrates with *non-Microsoft* security tools. The platform supports integration with a wide range of third-party solutions via APIs, but the complexity of mapping data from different vendors into a unified graph schema can be significant. This is where the open-source community could play a crucial role. The development of pre-built graph schemas and connectors for popular security tools would greatly accelerate adoption and enhance the value of Sentinel’s custom graph feature. Microsoft’s Sentinel GitHub repository is a potential hub for such community contributions.
What This Means for Enterprise IT
The immediate impact will be felt by SecOps analysts. Instead of manually piecing together relationships between alerts and entities, they can now visualize these connections in a dynamic graph, quickly identifying patterns and anomalies. This can significantly reduce signify time to detect (MTTD) and mean time to respond (MTTR). However, realizing these benefits requires investment in training and the development of custom graph schemas tailored to the organization’s specific threat landscape.
the ability to define custom relationships opens up new possibilities for threat hunting. Analysts can proactively search for indicators of compromise (IOCs) and patterns of behavior that might otherwise head unnoticed. For example, they could create a graph that maps communication patterns between users and external domains, identifying potential phishing campaigns or data exfiltration attempts.
“The biggest challenge in modern security isn’t the volume of data, it’s the complexity of relationships. Sentinel’s custom graphs are a step in the right direction, allowing analysts to move beyond simple alert correlation and truly understand the context of an attack.” – Dr. Emily Carter, CTO, Cygnus Security Analytics.
The API Landscape and Automation Potential
Sentinel’s custom graph functionality is exposed through a robust set of APIs, enabling automation and integration with other security tools. Analysts can programmatically create, update, and query graphs, allowing them to build automated workflows for incident investigation and response. This is particularly valuable for organizations that are adopting a Security Orchestration, Automation, and Response (SOAR) approach. The APIs support both REST and PowerShell, providing flexibility for developers and administrators.
However, the API documentation is currently somewhat sparse. Microsoft needs to provide more detailed examples and guidance to help developers effectively leverage these APIs. The Microsoft Sentinel REST API documentation is a starting point, but it lacks the depth and clarity needed for complex integrations.
The 30-Second Verdict
Sentinel’s custom graphs are a game-changer for SecOps teams. They move beyond simple alert correlation, enabling more nuanced and effective threat investigations. While performance and API documentation need improvement, the potential benefits are significant.
Beyond Visualization: The Future of Threat Modeling
The introduction of custom graphs isn’t just about visualization; it’s about a fundamental shift in how we approach threat modeling. Traditional threat models often rely on static diagrams and predefined attack scenarios. Custom graphs allow for a more dynamic and adaptive approach, reflecting the evolving nature of threats and the unique characteristics of each organization’s environment. This is particularly critical in the age of cloud-native applications and microservices, where the attack surface is constantly changing.
The long-term success of this feature will depend on Microsoft’s continued investment in the underlying graph database technology and its commitment to fostering a vibrant ecosystem of third-party integrations. The ability to seamlessly integrate with other security tools and leverage the collective intelligence of the open-source community will be critical for unlocking the full potential of Sentinel’s custom graphs.
“We’re seeing a clear trend towards graph-based security analytics. The ability to model relationships between entities is essential for detecting sophisticated attacks that evade traditional signature-based detection methods.” – Alex Ramirez, Lead Security Researcher, Digital Fortress.
Microsoft Sentinel’s custom graphs represent a significant step forward in the evolution of SIEM technology. They empower security teams to move beyond reactive alert triage and embrace a more proactive, intelligence-driven approach to threat detection and response. The challenge now is to ensure that the platform is scalable, extensible, and accessible to organizations of all sizes.