Identity-Based Ransomware Escalates Threat to Cloud Infrastructure
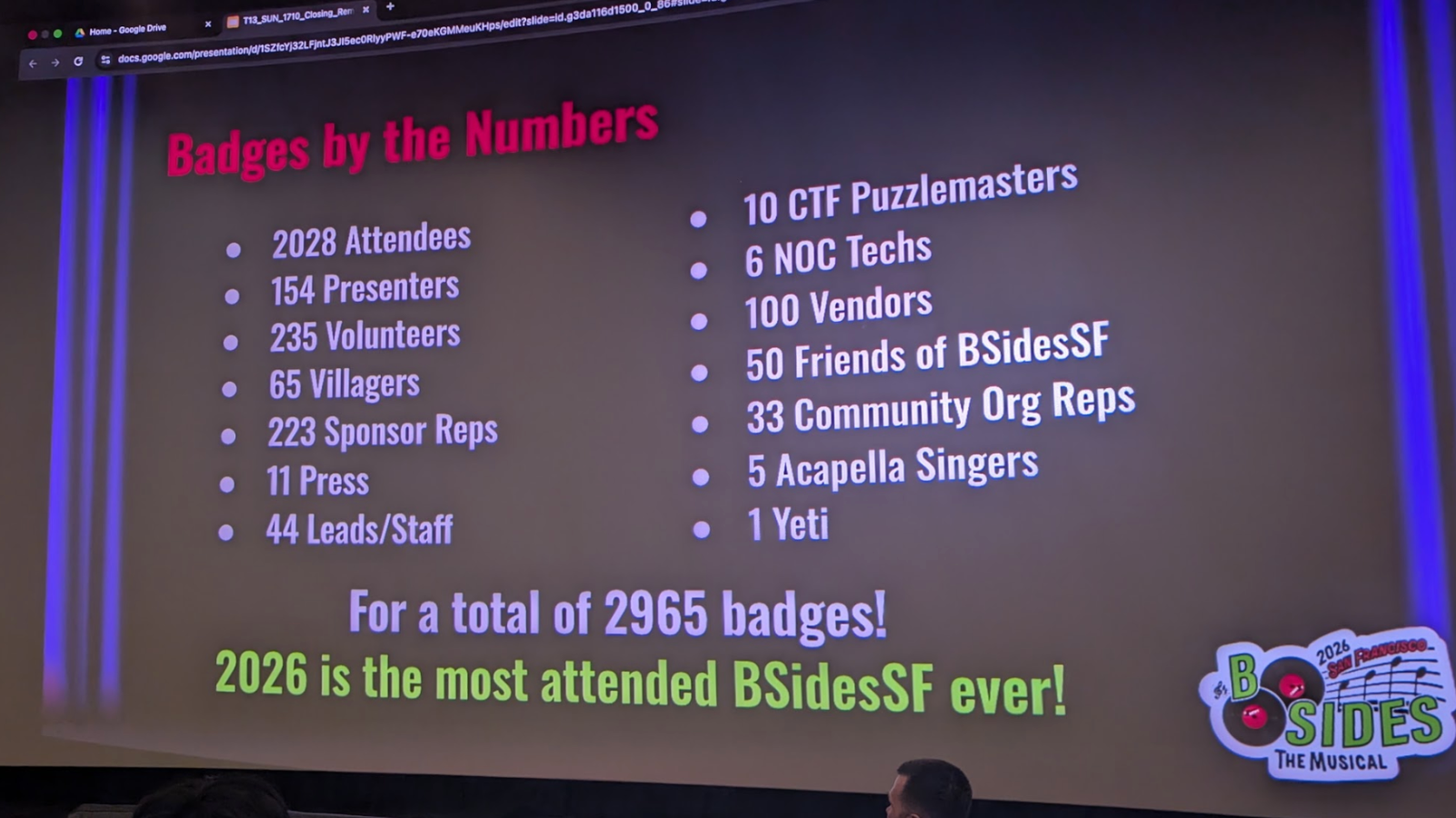
Researchers at BSides SF revealed a concerning trend: a surge in ransomware attacks targeting Software-as-a-Service (SaaS) and cloud assets, not through traditional network exploits, but by compromising user identities. This isn’t about cracking encryption. it’s about *becoming* you. The attacks leverage stolen credentials and insufficient multi-factor authentication (MFA) to gain access, then deploy ransomware that encrypts data within the SaaS application itself. This impacts businesses of all sizes, particularly those heavily reliant on cloud-based productivity suites and customer relationship management (CRM) systems. The core vulnerability lies in the human element and the often-lax security practices surrounding identity management.
The shift towards identity-based attacks isn’t entirely new, but the sophistication and scale are increasing. We’ve seen phishing campaigns evolve to bypass even relatively robust email security filters, and credential stuffing attacks are becoming more automated and effective. Although, the BSides SF presentation highlighted a new tactic: attackers are actively targeting third-party integrations within SaaS platforms. These integrations, while offering convenience, often inherit the permissions of the user account, providing a wider attack surface. Think of a marketing automation tool connected to your CRM – compromise the marketing tool, and you potentially compromise the entire CRM database.
The Rise of the “Lateral Identity Movement”
This isn’t simply about gaining access to one account. Attackers are demonstrating a capability for “lateral identity movement” – once inside, they exploit trust relationships between different cloud services and applications to escalate privileges and spread the ransomware. This is where the architectural weaknesses of many cloud environments become glaringly apparent. Many organizations haven’t fully mapped their identity perimeter, leaving blind spots that attackers are eager to exploit. The problem is exacerbated by the proliferation of shadow IT – applications and services adopted by employees without IT oversight – which often lack proper security controls.
The implications extend beyond data encryption. Attackers are increasingly employing “double extortion” tactics, threatening to leak sensitive data *even if* the ransom is paid. This is particularly damaging for organizations subject to strict data privacy regulations like GDPR or CCPA. The financial and reputational costs can be substantial. The disruption to business operations can be crippling, especially for organizations that lack robust disaster recovery plans.
The Role of Conditional Access and Zero Trust
The standard response – stronger passwords and MFA – is a good start, but it’s no longer sufficient. Attackers are finding ways to bypass even sophisticated MFA implementations, such as through SIM swapping or push notification fatigue. The real solution lies in adopting a Zero Trust security model, which assumes that no user or device is inherently trustworthy, regardless of their location or network connection. This requires implementing granular access controls, continuously verifying user identity, and monitoring for anomalous behavior.
Microsoft’s Conditional Access policies, for example, allow administrators to define specific conditions under which access to cloud resources is granted or denied. These conditions can include device compliance, location, user risk score, and application sensitivity. Similarly, Google Cloud Identity-Aware Proxy (IAP) provides a centralized access control layer for web applications running on Google Cloud Platform. However, implementing these solutions effectively requires a deep understanding of your cloud environment and your users’ access patterns. It’s not a “set it and forget it” approach.
The challenge is that many organizations are still struggling with the complexity of managing identities across multiple cloud providers. The lack of interoperability between different identity providers makes it difficult to enforce consistent security policies. This is where identity governance and administration (IGA) solutions can help, providing a centralized platform for managing user access and entitlements. However, even the best IGA solution is only as good as the data it receives. Accurate and up-to-date identity information is crucial.
What This Means for Enterprise IT
Enterprises need to move beyond perimeter-based security and embrace a Zero Trust architecture. This means implementing strong authentication mechanisms, enforcing least privilege access, and continuously monitoring for threats. Regular security audits and penetration testing are also essential to identify and address vulnerabilities. Investing in employee training is equally important – users need to be aware of the risks of phishing and other social engineering attacks.
organizations should carefully evaluate the security posture of their third-party vendors. Ensure that vendors have robust security controls in place and that they are compliant with relevant industry standards. Regularly review vendor access privileges and revoke access when it is no longer needed. The supply chain is often the weakest link in the security chain.
The API Economy and the Expanding Attack Surface
The proliferation of APIs is another contributing factor to the rise of identity-based ransomware. APIs provide a convenient way for applications to integrate with each other, but they also create new attack vectors. If an API is not properly secured, attackers can exploit it to gain access to sensitive data or to launch ransomware attacks. API security requires a multi-layered approach, including authentication, authorization, rate limiting, and input validation. Tools like Kong and Google Cloud Apigee provide API management capabilities, but they need to be configured correctly to be effective.

The increasing adoption of serverless computing also adds to the complexity. Serverless functions are often invoked by APIs, and they can be vulnerable to injection attacks and other security threats. Securing serverless functions requires a different approach than securing traditional applications. Tools like Snyk can help identify vulnerabilities in serverless code.
“We’re seeing a fundamental shift in how ransomware operates. It’s no longer about exploiting software vulnerabilities; it’s about exploiting human trust and the inherent complexities of modern cloud environments. The focus is on gaining legitimate access and then abusing that access for malicious purposes.” – Jake Williams, CTO, Breach & Attack Simulation Platform, Yubico.
The 30-Second Verdict
Identity is the new perimeter. Traditional security measures are no longer sufficient to protect against the evolving threat landscape. Organizations must adopt a Zero Trust security model and invest in robust identity governance and administration solutions. The cost of inaction is far greater than the cost of prevention.
The BSides SF presentation underscored a critical point: the current security paradigm is failing to keep pace with the sophistication of attackers. We need a fundamental rethink of how we approach security in the cloud. This requires a shift in mindset, a commitment to continuous improvement, and a willingness to embrace new technologies and approaches. The future of cybersecurity depends on it.
The Impact on Open Source and Platform Lock-In
Interestingly, this trend also impacts the open-source ecosystem. While open-source tools often provide greater transparency and flexibility, they can also be more vulnerable to supply chain attacks if not properly vetted. Attackers may target open-source libraries and frameworks to inject malicious code, which can then be distributed to unsuspecting users. This highlights the importance of using trusted sources for open-source software and regularly scanning for vulnerabilities.
the rise of identity-based ransomware could exacerbate platform lock-in. Cloud providers are increasingly offering integrated security solutions, which can make it difficult for organizations to switch providers without incurring significant costs and risks. This creates a vendor lock-in situation, where organizations are dependent on a single provider for their security needs. The push for interoperability and open standards is more critical than ever.
The situation demands a proactive, layered defense. It’s not enough to simply react to attacks; organizations must anticipate them and take steps to prevent them from happening in the first place. This requires a holistic approach to security, encompassing people, processes, and technology. The stakes are high, and the time to act is now.