Stryker, a global medical device leader, suffered a massive network collapse targeting its Microsoft environment. The attack, claimed by Iranian-aligned group Handala Hack, utilized destructive wiper tactics to neutralize endpoints, likely as retaliation for recent geopolitical airstrikes, disrupting critical internal infrastructure across its global Windows-based ecosystem.
This isn’t your run-of-the-mill ransomware play. There was no ransom note, no countdown timer, and no negotiation for Bitcoin. This was a scorched-earth operation designed for maximum operational friction. When a state-aligned actor decides to move from espionage to destruction, the goal isn’t profit—it’s the systematic erasure of the target’s ability to function.
The timing is surgical. Coming on the heels of US and Israeli airstrikes on Iran, the attack on Stryker serves as a loud, digital signal. It demonstrates that the “cyber-kinetic” loop is tightening; physical munitions in the air are now being mirrored by wiper binaries on the ground.
The Intune Paradox: When Management Tools Grow Weapons
The most chilling detail of this breach isn’t the scale, but the mechanism. Although Stryker’s official communications claim there is “no indication that ransomware or malware” was involved, the evidence from the field—specifically reports of wiped Intune-managed devices—points to a far more sophisticated “Living-off-the-Land” (LotL) attack.
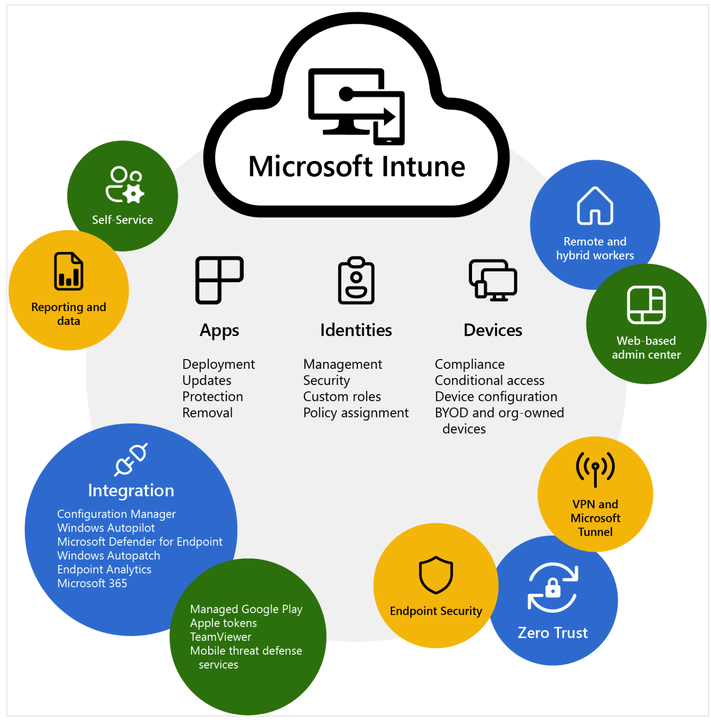
For the uninitiated, Microsoft Intune is a cloud-based endpoint management tool. It allows IT admins to push updates, configure security policies, and, crucially, remotely wipe devices to protect corporate data if a laptop is stolen. In a standard environment, this is a security feature. In a compromised environment, it is a weapon of mass destruction.
If the Handala Hack group gained access to a Global Administrator account or a privileged Intune role within Stryker’s Entra ID (formerly Azure AD) tenant, they wouldn’t necessitate to deploy a custom piece of malware. They could simply issue a “Factory Reset” or “Wipe” command via the official Microsoft API. To the device, this looks like a legitimate command from the company’s own headquarters. It bypasses traditional EDR (Endpoint Detection and Response) tools because the command is signed and authorized by the management server.
It’s an architectural nightmare.
The 30-Second Verdict: Why This Matters
- Not Ransomware: This was a “wiper” event aimed at destruction, not extortion.
- Tenant Takeover: The likely vector was a compromise of the Microsoft cloud management layer, not a traditional phishing-to-exe pipeline.
- MedTech Fragility: The attack highlights how critical healthcare infrastructure relies on a fragile, centralized cloud identity plane.
The Architecture of a Wipe: x86 vs. ARM
The reports indicate that both computers and phones were neutralized. This suggests the attackers didn’t just target Windows x86 kernels; they hit the entire managed ecosystem, including iOS and Android devices running on ARM architecture. This universality is the hallmark of an MDM (Mobile Device Management) compromise.
In a traditional malware attack, the hacker must write different payloads for different CPU architectures. A Windows .exe won’t run on an iPhone. However, by targeting the Microsoft Intune management plane, the attackers effectively abstracted the hardware. They didn’t need to care about the OS or the chip; they just needed the “Wipe” button in the cloud console.
“The shift from deploying custom malware to leveraging native cloud management tools represents a critical evolution in state-sponsored attacks. We are seeing a move toward ‘Administrative Sabotage,’ where the attacker doesn’t break into the house—they steal the master key and use the homeowner’s own security system to lock them out.”
This shift renders many legacy security benchmarks irrelevant. We are no longer just fighting “bad code”; we are fighting “bad permissions.”
Geopolitical Fallout and the Single Point of Failure
Stryker is a linchpin in the medical device supply chain. When their Windows network goes dark, the ripple effects move from the server room to the operating room. While Stryker maintains that the incident is contained to the “internal Microsoft environment,” the sheer scale of the disruption suggests a failure in identity segmentation.
This incident exposes the danger of the “Single Pane of Glass” philosophy. Big Tech has pushed enterprises toward total consolidation—one identity provider, one management console, one cloud ecosystem. While this reduces complexity for the IT admin, it creates a catastrophic single point of failure. If the Entra ID tenant is popped, the entire kingdom falls.
We are seeing this play out across the board, from the SolarWinds supply chain compromise to the recent volatility in the CISA-tracked state-sponsored campaigns. The “chip wars” aren’t just about who makes the best H100 GPUs; they are about who controls the identity layer that manages the devices those chips power.
Enterprise Mitigation: Beyond the Password
If your organization is running a heavy Microsoft stack, the Stryker event should be a wake-up call. Relying on a complex password is like putting a deadbolt on a cardboard door. The path forward requires a ruthless approach to identity hygiene.
First, the implementation of Privileged Identity Management (PIM). No one should have “Global Admin” rights by default. Access should be “Just-In-Time” (JIT), requiring a secondary approval and a time-limited window. This prevents a single compromised credential from becoming a permanent skeleton key.
Second, the adoption of hardware-backed MFA. SMS and app-based push notifications are vulnerable to SIM swapping and MFA fatigue attacks. FIDO2-compliant hardware keys (like YubiKeys) are the only way to effectively neutralize the credential theft that likely enabled the Handala Hack group.
Finally, enterprises must implement “out-of-band” recovery. If your backup management is tied to the same Microsoft tenant that just got wiped, you are effectively dead in the water. Immutable backups stored in a logically air-gapped environment are the only insurance policy that actually pays out during a wiper event.
The Stryker attack wasn’t just a breach; it was a demonstration. The message from the Iranian-aligned actors is clear: your management tools are our weapons. The only defense is to stop trusting the “God-mode” of the cloud.
For a deeper dive into the technical specifics of wiper patterns, the MITRE ATT&CK framework provides a comprehensive breakdown of “Data Destruction” techniques that every CISO should be auditing against this week.

