High-resolution live wallpapers trending on TikTok in March 2026 represent more than aesthetic customization; they signal a shift in NPU utilization and potential AI-driven security vectors. As 8K dynamic backgrounds become mainstream, they stress-test 2026 hardware architectures while introducing executable code risks that require immediate AI Red Teaming and advanced security analytics to mitigate enterprise exposure.
The Hidden Compute Cost of 8K Aesthetics
What appears as a seamless visual loop on a smartphone or desktop interface is actually a rigorous stress test for modern System-on-Chip (SoC) designs. In 2026, rendering true 8K live wallpapers requires significant offloading to Neural Processing Units (NPUs) rather than relying solely on traditional GPU rasterization. This shift is necessary to maintain battery efficiency while handling real-time AI upscaling and particle physics simulations embedded in the wallpaper metadata. Users chasing the #livewallpaper8K trend often overlook the thermal throttling implications. When a device attempts to sustain 60 frames per second at 7680×4320 resolution, the power draw spikes exponentially compared to standard 4K static images.
We are seeing a divergence in hardware capability. Flagship devices equipped with dedicated AI engines can handle the inference load required for procedural generation within the wallpaper itself. Though, mid-range hardware often resorts to pre-rendered video loops, which lack interactivity but preserve thermal headroom. This fragmentation creates a inconsistent user experience where the “live” element is merely a marketing veneer on lower-end devices. The technical reality is that true interactivity demands local model inference, pushing the boundaries of on-device privacy and compute resources.
Security Vectors in Dynamic Media Files
The transition from static JPEGs to executable dynamic wallpapers reintroduces legacy security risks under a novel AI guise. Historically, wallpaper engines have been vectors for malware delivery because they require elevated permissions to render over the desktop environment. In the AI era, this risk is compounded. A wallpaper file is no longer just a media container; it can harbor scripts that trigger API calls or exploit vulnerabilities in the rendering engine. This is where the role of the AI Red Teamer becomes critical. These adversarial testers are no longer optional; they are essential for validating that media files do not contain hidden prompts or scripts capable of escaping the sandbox.
Enterprise environments are particularly vulnerable. A seemingly innocuous background image downloaded by an employee could contain adversarial perturbations designed to trick internal security classifiers. The industry is responding by integrating security analytics directly into the media pipeline. Companies like Netskope are architecting next-generation security analytics to inspect these flows before they reach the endpoint. The goal is to treat media files with the same scrutiny as executable binaries, scanning for anomalous behavior patterns that indicate a compromise.
“We are seeking an exceptional Distinguished Engineer to architect next-generation security analytics… To detect threats in real-time across cloud and endpoint environments.” This requirement highlights the industry’s pivot toward proactive threat hunting in non-traditional data streams like media assets.
The Elite Hacker’s Strategic Patience
While consumers focus on resolution, adversarial actors are employing strategic patience. The current landscape suggests that elite hackers are not rushing to exploit every new wallpaper trend immediately. Instead, they are waiting for the AI infrastructure to mature, allowing them to develop more sophisticated persistence mechanisms. The analysis of the Elite Hacker’s Persona reveals a shift toward long-term infiltration rather than smash-and-grab tactics. In the context of live wallpapers, this means waiting for a specific rendering engine update to become ubiquitous before deploying a zero-day exploit that targets the NPU driver itself.
This patience allows attackers to maximize impact. By targeting the underlying AI models that generate or upscale the wallpaper content, adversaries can potentially inject backdoors into the training data or the inference pipeline. This is a supply chain attack vector that bypasses traditional perimeter defenses. The implication for developers is clear: security must be baked into the model weights and the rendering pipeline, not just the file container. The Principal Security Engineer roles emerging at major tech firms reflect this need for deep architectural security knowledge that spans both AI and traditional cybersecurity domains.
Resource Consumption Comparison: Static vs. AI Live
| Feature | Static 8K Image | AI-Generated Live Wallpaper |
|---|---|---|
| Primary Compute Unit | GPU (Rasterization) | NPU + GPU (Inference + Render) |
| Idle Power Draw | Negligible | High (Continuous Inference) |
| Security Surface | Low (File Parse Only) | High (Script Execution + API Calls) |
| Thermal Impact | Minimal | Significant (Thermal Throttling Risk) |
Enterprise Mitigation and Ecosystem Bridging
The broader tech war over ecosystem lock-in plays out in these customization features. Closed ecosystems like iOS have historically restricted live wallpapers to preserve battery life and security, while open platforms like Android and Windows allow greater flexibility at the cost of increased vulnerability surface. In 2026, the distinction is blurring as AI agents manage system resources. The challenge is ensuring that these agents do not prioritize aesthetics over security posture. Third-party developers must adhere to stricter guidelines regarding API access for background processes.
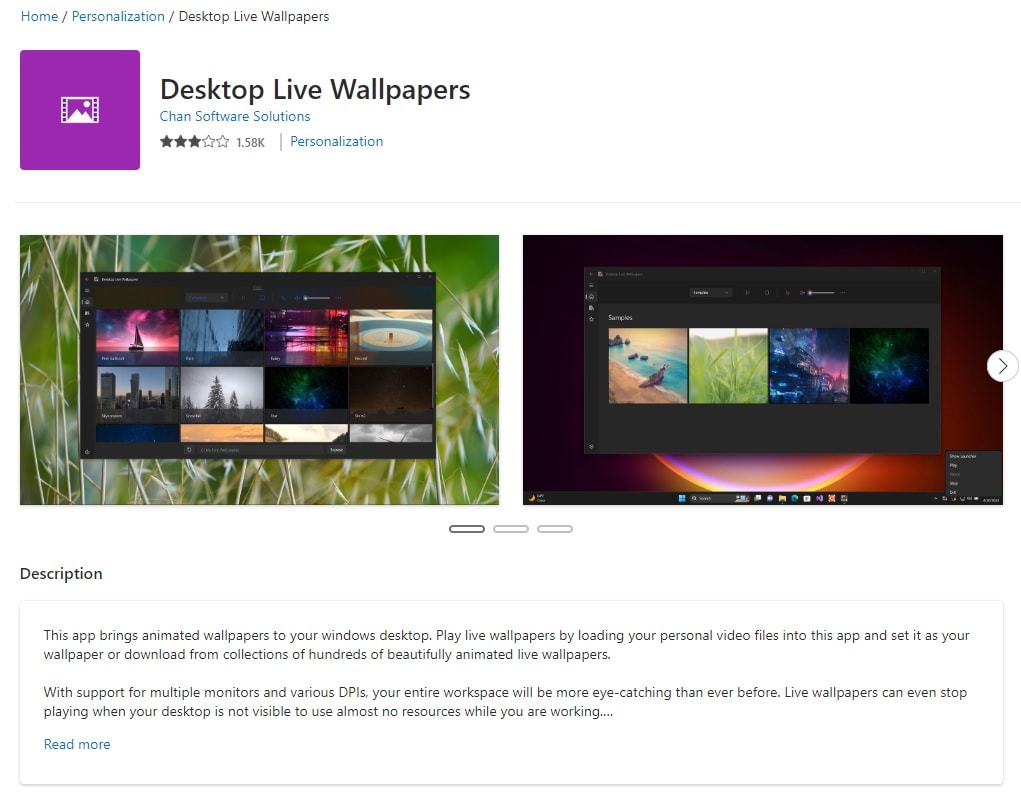
Developers should refer to established security standards when building these applications. The security analytics required to monitor these applications are becoming more sophisticated, leveraging machine learning to detect anomalies in resource usage that might indicate a compromised wallpaper engine. Open-source communities are also stepping up, auditing code on platforms like GitHub to ensure transparency in how these wallpapers interact with the operating system. Users should prioritize wallpapers from verified developers who publish their code for community review.
The 30-Second Verdict
For the average user, the risk of downloading a random 8K live wallpaper from TikTok in 2026 outweighs the aesthetic benefit. The compute cost is high, and the security vetting is often non-existent. Enterprise IT should block unsigned dynamic wallpaper engines by default. For enthusiasts, stick to open-source projects where the code is verifiable and the resource usage is documented. The future of desktop customization is AI-driven, but until security analytics catch up to the rendering capabilities, caution is the only viable strategy.
The convergence of high-fidelity media and AI inference creates a new attack surface that demands vigilance. As we move further into 2026, the line between a visual asset and a security threat will continue to thin. The industry’s response, driven by roles in AI Red Teaming and Security Analytics, will determine whether this trend remains a harmless customization or becomes a significant vector for compromise. Stay skeptical, verify the source, and monitor your NPU usage.

