The Trump administration’s FY2027 budget proposes cutting $707 million from CISA, effectively dismantling the agency’s election security program and slashing 860 positions. This move reduces the U.S. Primary civilian cybersecurity agency to a $2 billion operation, shifting critical infrastructure defense toward private-sector reliance and decentralized oversight.
This isn’t a mere budgetary trim; it is a fundamental architectural shift in how the United States handles its national attack surface. For the uninitiated, CISA (the Cybersecurity and Infrastructure Security Agency) functions as the central Security Operations Center (SOC) for the federal government and a vital telemetry hub for the private sector. By stripping away nearly a billion dollars and hundreds of specialized roles, the administration is essentially decommissioning the “early warning system” that identifies nation-state actors before they breach critical nodes.
The timing is particularly volatile. As we move through April 2026, the industry is already reeling from a wave of DOGE-driven layoffs that have gutted middle-management and technical implementation layers across several federal agencies. We are witnessing a mass exodus of talent—the kind of people who understand how to map a zero-day exploit to a specific APT (Advanced Persistent Threat) group—moving toward the private sector where the compensation is higher and the bureaucracy is lower.
The Technical Erosion of the KEV Catalog and Vulnerability Orchestration
One of the most critical, yet overlooked, casualties of these cuts is the maintenance of the Known Exploited Vulnerabilities (KEV) catalog. In the world of vulnerability management, the KEV is a gold standard. It moves the industry away from the flawed CVSS (Common Vulnerability Scoring System) model—which often overestimates the risk of theoretical bugs—toward a model based on actual, observed exploitation in the wild.
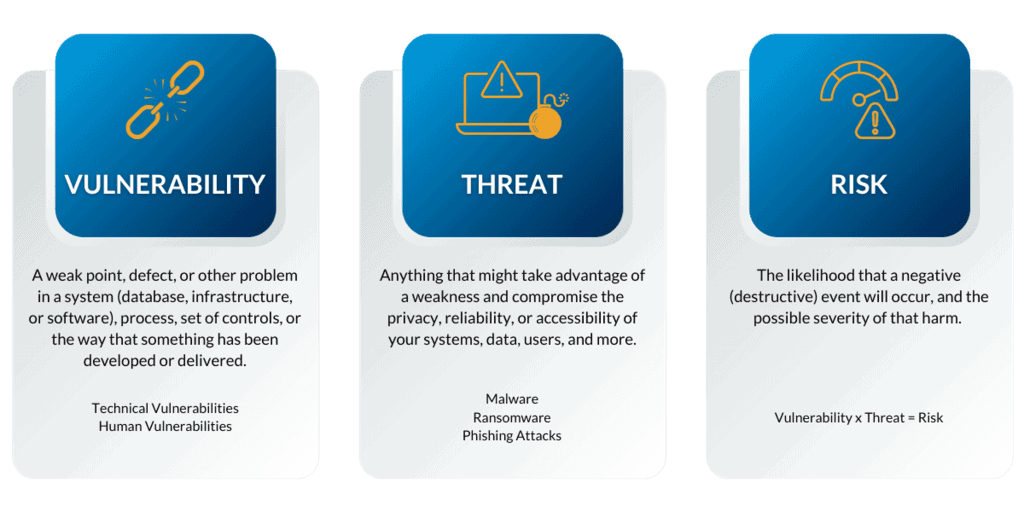
When you cut 860 positions, you aren’t just losing “paper pushers.” You are losing the analysts who perform the forensic work required to validate these vulnerabilities. If the KEV catalog stagnates, the “patching race” tilts heavily in favor of the attacker. Enterprises rely on this data to prioritize their patching cycles; without it, IT teams are forced back into the “patch everything” madness, leading to operational instability and increased downtime.
the loss of “Cyber Hygiene” services—free vulnerability scanning and guidance for tiny-town governments—creates a massive security vacuum. Most small municipalities operate on legacy x86 architectures with unpatched Windows Server instances and zero-budget security stacks. CISA was the only entity providing them with a baseline of visibility. Removing that visibility doesn’t make the vulnerabilities move away; it just makes the municipalities blind to them.
“CISA provides the connective tissue between the intelligence community and the private sector. Severing that link doesn’t remove the threat; it just removes the alarm system. We are moving from a posture of proactive defense to one of reactive cleanup.”
Decentralizing Election Security: A Distributed System Failure
The total elimination of the election security program is a gamble on a distributed system that lacks a unified protocol. U.S. Elections are not a single monolithic database; they are a fragmented ecosystem of thousands of local jurisdictions, each using different hardware, from proprietary voting machines to basic spreadsheets.
CISA’s role was to act as the orchestration layer, providing standardized security frameworks and incident response (IR) support. By killing this program, the administration is pushing the responsibility down to the local level. From a technical standpoint, this is a disaster. Local clerks are not cybersecurity experts; they cannot defend against a sophisticated spear-phishing campaign or a supply-chain attack on voting software vendors.
Without federal oversight, we risk the emergence of “shadow IT” in election offices—where local officials implement their own haphazard security solutions that may actually introduce new vulnerabilities. This fragmentation is a gift to adversaries who prefer to target the weakest link in a chain rather than the strongest.
The 30-Second Verdict: Risk vs. Efficiency
- The Goal: Reduce federal spending and eliminate “redundant” bureaucracy via DOGE.
- The Reality: A significant increase in the national attack surface due to the loss of centralized telemetry.
- The Technical Debt: A projected surge in unpatched CVEs across critical infrastructure as the KEV catalog loses its operational velocity.
- The Bottom Line: We are trading systemic resilience for short-term fiscal optics.
The Geopolitical Attack Surface and the Talent Gap
From the perspective of a state-sponsored actor, these budget cuts are a signal. In cybersecurity, “deterrence by denial” means making the cost of an attack so high—through robust defenses—that the adversary gives up. By gutting CISA, the U.S. Is effectively lowering the cost of entry for attackers.
We are seeing a shift in the “War for Talent.” The specialized skills required to manage national-level cybersecurity—deep knowledge of BGP hijacking, memory corruption bugs, and NIST framework implementation—are rare. When the federal government signals that these roles are expendable, those experts move to the private sector or, in some cases, to consulting firms that will charge the government ten times the original salary to fix the problems created by the cuts.
This creates a dangerous dependency on a few “Big Tech” players. If the government can no longer perform its own analysis, it becomes entirely dependent on the telemetry provided by companies like Microsoft, CrowdStrike, or Google. This isn’t just a budget issue; it’s a sovereignty issue. We are outsourcing the visibility of our national security to a handful of corporations whose primary incentive is shareholder value, not national defense.
The following table illustrates the shift in the operational model proposed by the FY27 budget:
| Capability | Current CISA Model (FY25/26) | Proposed Model (FY27) |
|---|---|---|
| Vulnerability Tracking | Centralized KEV Catalog / Active Validation | Fragmented / Private Sector Led |
| Election Security | Federal Coordination & IR Support | Local/State Responsibility (Unfunded) |
| Threat Telemetry | Cross-Sector Information Sharing | Siloed / Proprietary Vendor Data |
| Human Capital | Dedicated Federal Cyber Analysts | Contractor-Heavy / Outsourced |
The Path Forward: Mitigation for the Private Sector
For CTOs and CISOs, the takeaway is clear: the federal safety net is fraying. Organizations can no longer rely on CISA to be the primary source of threat intelligence or the first responder during a national crisis. We must move toward a “Zero Trust” architecture not just in our networks, but in our expectations of government support.
Investment must shift toward open-source intelligence (OSINT) and stronger peer-to-peer sharing networks, such as ISACA or industry-specific ISACs (Information Sharing and Analysis Centers). If the central hub is gone, the only way to survive is to build a more resilient, decentralized mesh of security professionals who can share data in real-time without waiting for a federal directive that may never come.
The administration may call this “efficiency.” In the language of engineering, it’s called removing the redundancy from a mission-critical system. And in any other field, that’s how you invite a catastrophic system failure.

