Ireland Brand Success Story: No Loans, Smart Cash Flow
Bobby Kerr, the man behind the hugely successful Irish coffee chain Bob & Bert’s, built a national brand from the ground up without a single bank loan. Kerr leveraged a ... Read More
Saturday Edition
Stay updated with Archyde – your source for breaking news, global headlines, economy, entertainment, health, technology, and sports. Fresh stories daily.
Bobby Kerr, the man behind the hugely successful Irish coffee chain Bob & Bert’s, built a national brand from the ground up without a single bank loan. Kerr leveraged a ... Read More
Continuous Coverage

Domaine de Vassal, a French vineyard housing 4,200 grape varietals, is undergoing a “gigantic operation” – a relocation…

Dubai is poised to become a major entertainment hub this May, hosting a diverse array of events including…

LEGO Bricks Meet Pokémon GO: A Deeper Dive into Niantic’s Augmented Reality Ecosystem Niantic, the developer behind the…

A three-acre parcel of residential land in Princeton, North Carolina, recently listed for sale, might seem a localized…

Brenda Song has opened up about the surprising origins of her relationship with Macaulay Culkin, revealing a long-held…

The US Open Cup, often overshadowed by its glitzier European counterparts, delivered a night of pure, unadulterated drama…
Global Affairs

U.S. Democrats, led by members of the House Armed Services Committee, directly questioned Pentagon Chief Lloyd Hegseth on…
Markets And Money
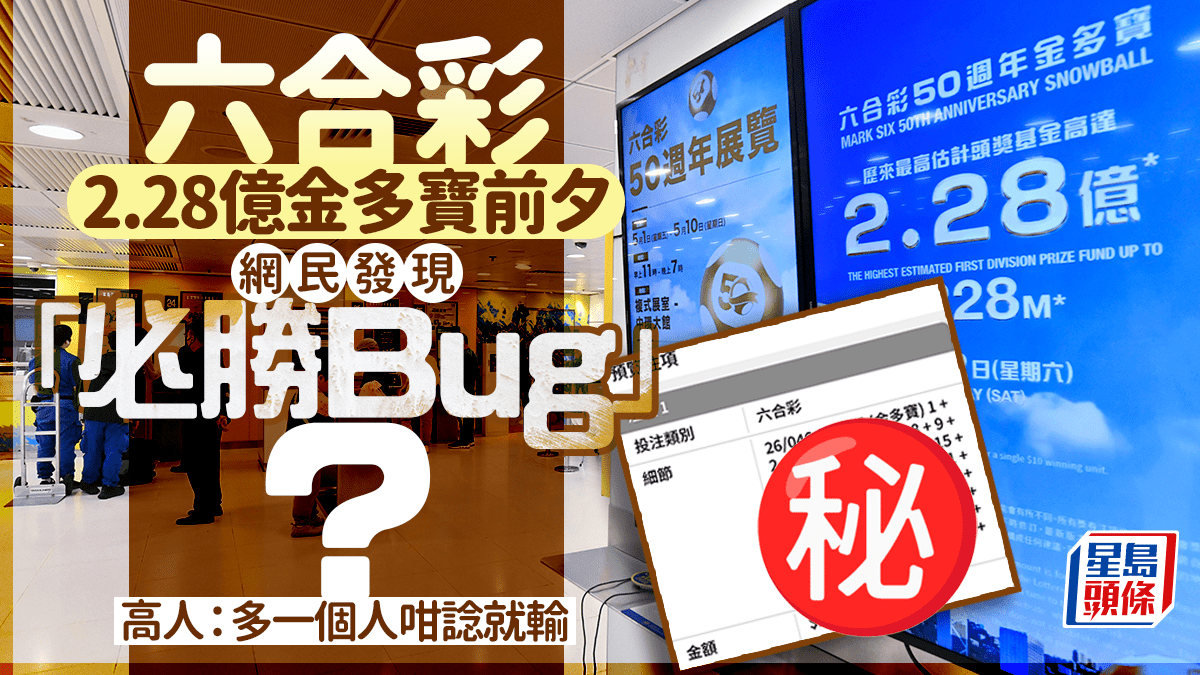
Hong Kong’s recent 六合彩 lottery drawing, offering a record-breaking HK$228 million (approximately US$29.2 million) jackpot, has sparked a…
Digital Culture

The Looming Threat of Evolvable AI: Beyond AGI, a Latest Class of Risk Emerges Researchers at the HUN-REN…
Science And Wellbeing
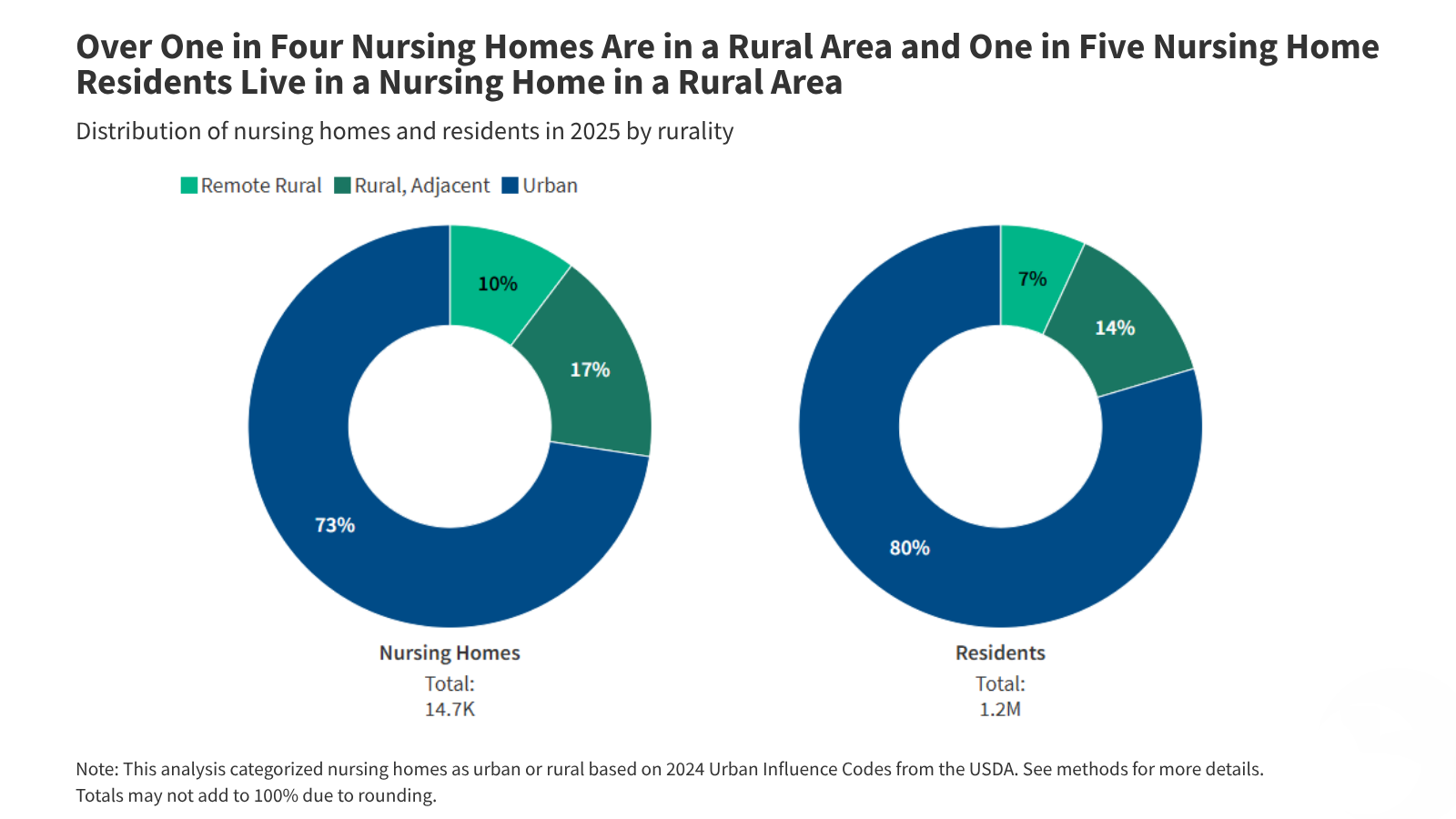
A recent analysis of Nursing Home Compare data reveals significant disparities in quality of care between rural and…
Screen And Sound

Marco Antonio Pérez, the composer behind the emotionally resonant ballad “Fuerte no soy,” recently detailed his creative process…
Fixtures And Form

Sean Strickland ignited controversy following a racially charged rant directed at his UFC 328 opponent, Khamzat Chimaev, escalating…