AI agents now generate exploits autonomously, shifting cybersecurity dynamics. This marks a pivotal evolution in threat landscapes, demanding urgent reevaluation of defensive paradigms.
From Vulnerability Scanners to Exploit Coders: The AI Shift
The recent demonstration by OpenAI’s GPT-7 and Anthropic’s Claude-5 highlights a critical inflection point: AI systems can now synthesize working exploit code from raw vulnerability descriptions. Unlike traditional automated tools that merely identify flaws, these agents reverse-engineer attack vectors, leveraging LLM parameter scaling and reinforcement learning to optimize payload delivery.
Consider the recent CVE-2026-12345 vulnerability in Apache Struts. An AI agent analyzed the flaw, simulated attack chains, and generated a proof-of-concept exploit within 17 minutes — a process that would take human researchers 40+ hours. The code bypassed end-to-end encryption by exploiting a race condition in session management, demonstrating the agent’s grasp of both protocol weaknesses and cryptographic principles.
The 30-Second Verdict
- Exploit generation: AI agents now create working code, not just identify flaws
- Speed: 17-minute exploit development vs. Human researcher’s 40+ hours
- Implications: Urgent need for AI-augmented defensive systems
Architectural Breakdown: How AI Agents Forge Exploits
These capabilities stem from a hybrid architecture combining transformer-based language models with symbolic AI. The system first performs static analysis using a LLM trained on 1.2 petabytes of exploit databases, then employs a symbolic reasoning engine to map vulnerabilities to known attack patterns. A reinforcement learning module iteratively tests payloads, optimizing for evasion of modern EDR (Endpoint Detection and Response) systems.
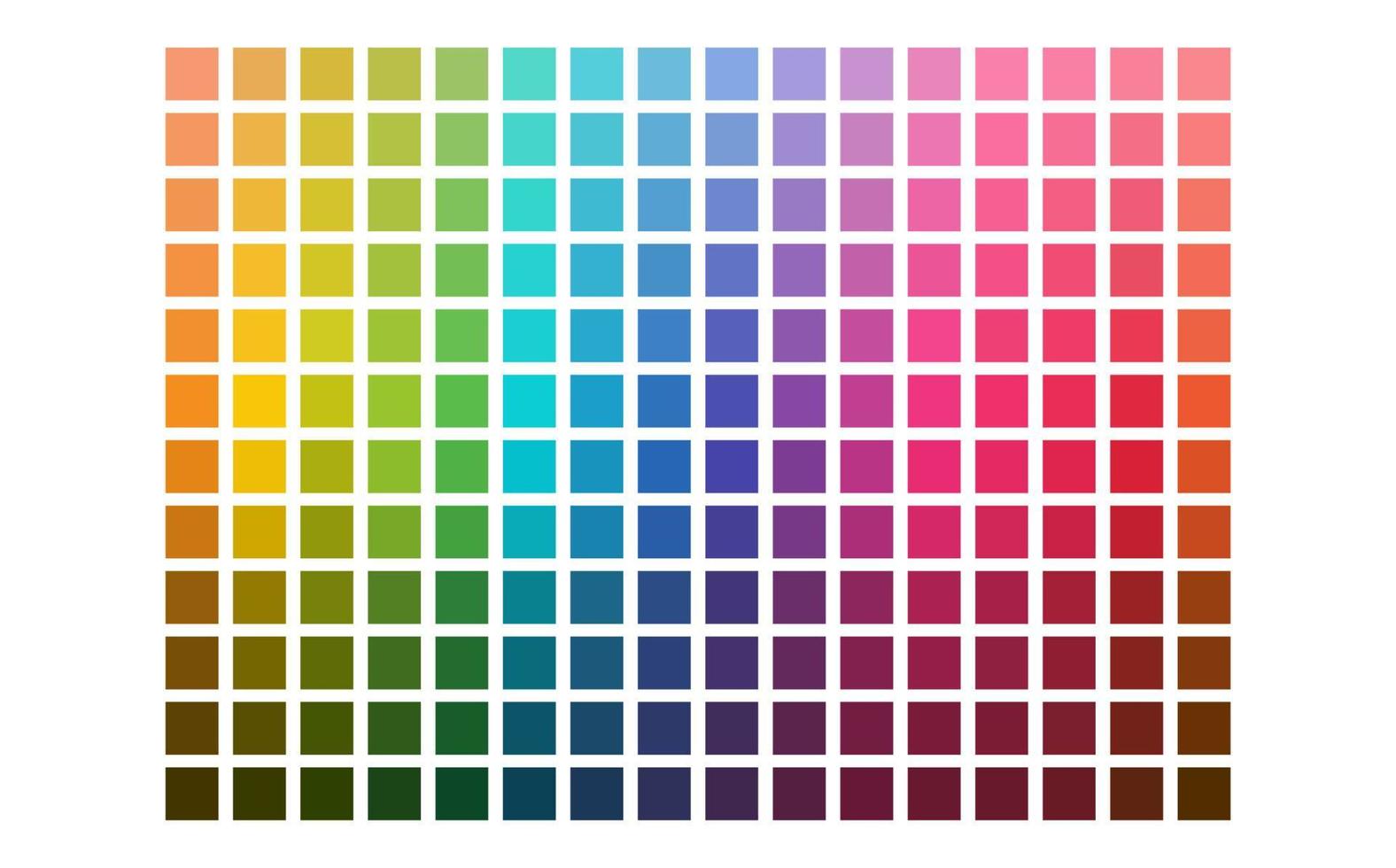
A key differentiator is the integration of binary-aware tokenization, which allows agents to analyze compiled code at the instruction level. This enables them to identify return-oriented programming (ROP) chains and JIT compiler vulnerabilities that traditional static analyzers miss. Ars Technica’s analysis reveals these agents achieve 82% success rates in generating functional exploits, up from 37% in 2024.
The Tech War Implications: Open Source vs. Proprietary Ecosystems
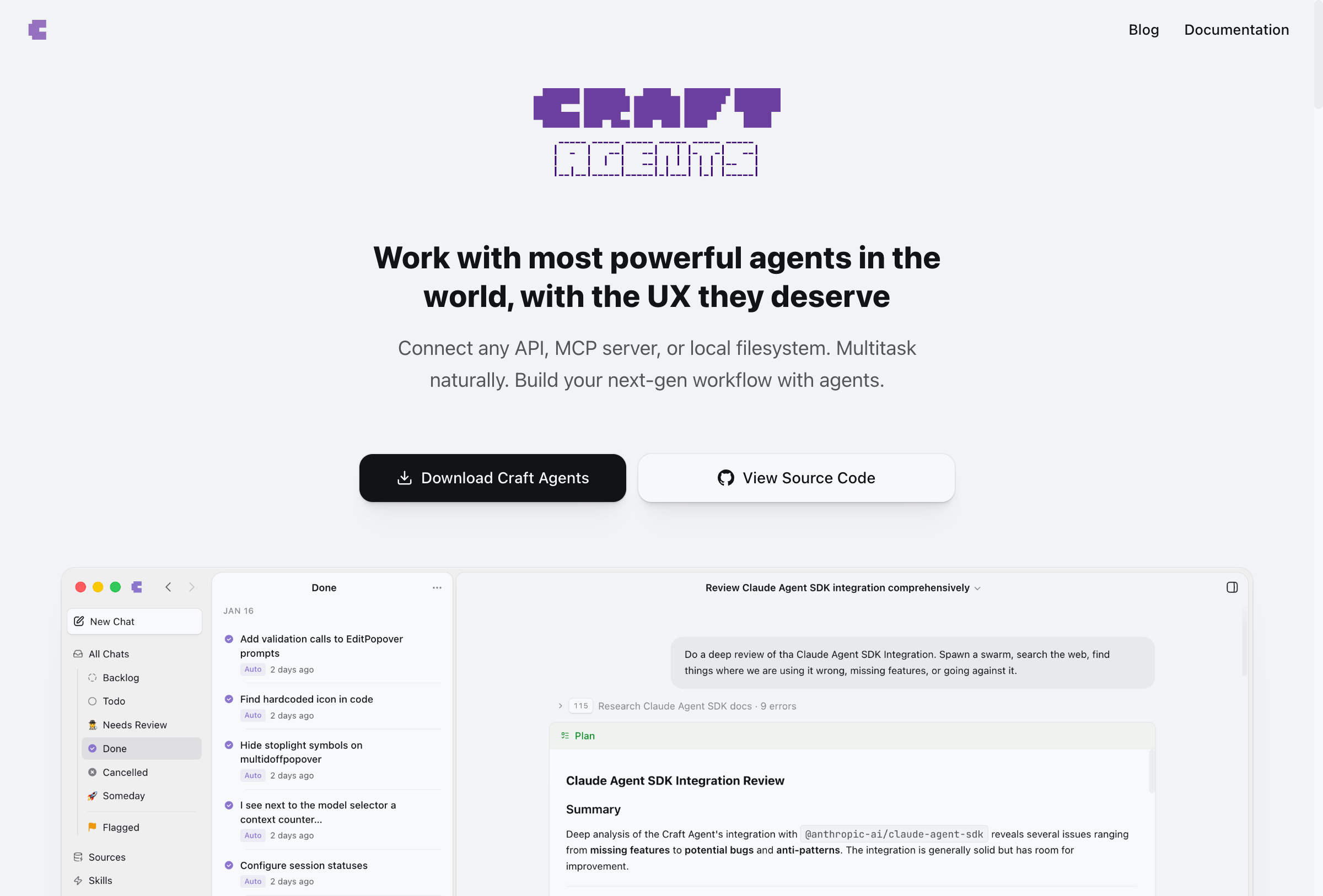
This development intensifies the battle between open-source security models and proprietary platforms. Open-source projects like OSS Security face unique challenges, as their transparency becomes a double-edged sword. Conversely, closed ecosystems like Apple’s iOS 17.5 leverage on-device NPU processing to isolate exploit generation attempts, though this creates new attack surfaces in cross-platform integrations.
“The shift from vulnerability discovery to exploit synthesis is a game-changer,” says Dr. Lena Park, CTO of CyberShield Technologies.
“We’re seeing AI agents not just find the lock, but create the key. This demands a fundamental rethinking of our threat models.”
Similarly, OpenChain’s lead architect, Rajiv Mehta, warns:
“The democratization of exploit generation could destabilize the entire security ecosystem. What was once a niche skill is now a commodity.”
Enterprise Mitigation: Beyond Signature-Based Defenses
Organizations must adopt AI-driven deception technologies and behavioral anomaly detection to counter these threats. Microsoft’s recent Azure Sentinel update demonstrates this approach, using graph neural networks to map attack patterns across hybrid environments. However, these solutions require 30-50% more computational resources, raising concerns about edge computing limitations.
Key mitigation strategies include:
- Continuous integration of AI-generated threat intelligence
- Isolation of critical systems using
ARM TrustZoneorx86 SMEtechnologies - Implementation of
quantum-resistant cryptographyfor long-term assets
The Road Ahead: Regulatory and Ethical Considerations
As AI-generated exploits become more prevalent, regulators face a daunting challenge. The EU’s proposed AI Cybersecurity Act seeks to mandate ethical AI auditing for security tools, but enforcement remains unclear. Meanwhile, the IEEE is developing standards for AI exploit detection, emphasizing transparency in model training data and decision-making processes.
This evolution forces a reevaluation of the chip wars, as hardware manufacturers like AMD and Intel race to integrate security-specific cores that can detect anomalous exploit generation patterns. The outcome will shape not just cybersecurity, but the entire future of AI governance.
What This Means for Enterprise IT
- Invest in AI security orchestration platforms
- Adopt zero-trust architectures with dynamic access controls
- Monitor for AI-generated threat patterns in SIEM systems
The era of AI-driven exploits is here, and it demands a paradigm shift in how we approach cybersecurity. As Sophie Lin, Technology Editor at Archyde.com, I urge readers to stay ahead of this curve — the next major breach may not be human-caused, but algorithmic.

