WhatsApp Web’s mobile-off functionality challenges conventional design, leveraging end-to-end encryption and session management to redefine cross-device synchronization. This update redefines user convenience, but at what security cost?
Why WhatsApp Web’s Mobile-Off Mode Is a Game-Changer (For Now)
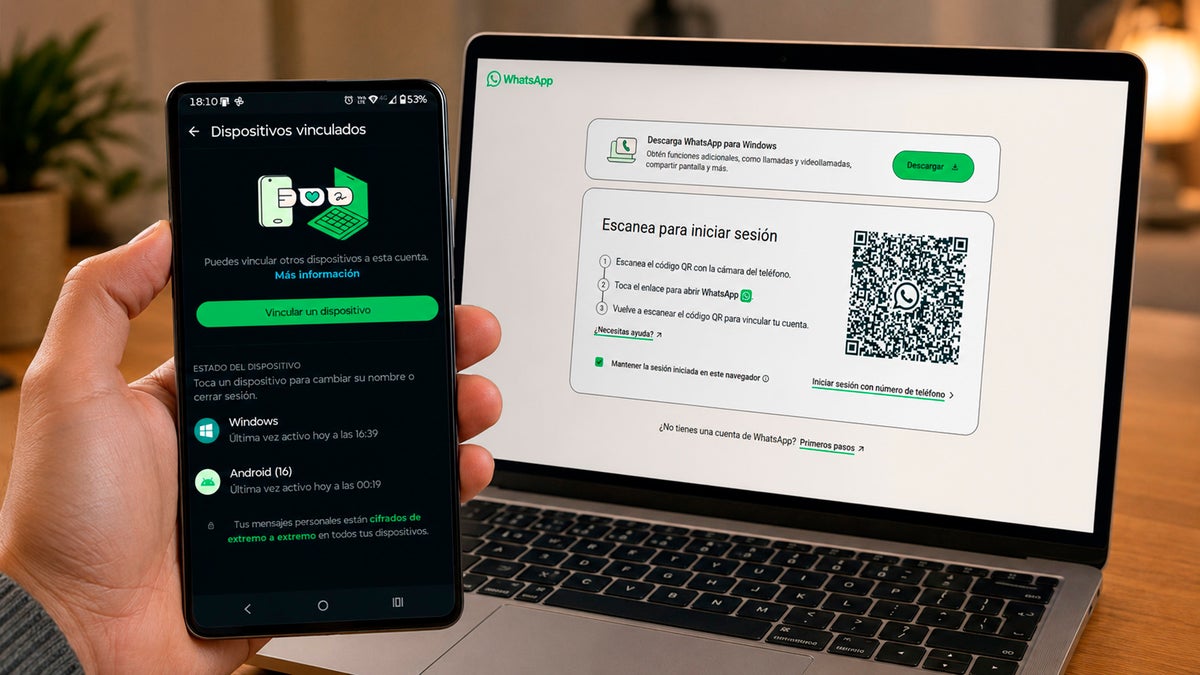
WhatsApp’s recent beta rollout enables desktop users to maintain active sessions even when the mobile device is powered off. This shift hinges on a reengineered session persistence protocol, where the desktop app caches session keys in secure enclave memory, bypassing the traditional QR code handshake. While the feature promises uninterrupted communication, it introduces critical security trade-offs.
Under the hood, WhatsApp employs a session-store module that serializes encryption keys using Apple’s Keychain Services on iOS and Windows Credential Manager on desktops. This allows the desktop client to reauthenticate via a pre-shared symmetric key, eliminating the need for real-time mobile device connectivity. However, this approach violates the WebAuthn standard’s zero-trust principles, as the session remains valid without re-verification.
The 30-Second Verdict
- Pros: Continuous access during mobile downtime, reduced latency for frequent users.
- Cons: Elevated risk of physical device compromise, potential for session hijacking.
- Verdict: A convenience feature with non-trivial security implications.
How the Mobile-Off Mode Breaks WhatsApp’s Architecture
Traditionally, WhatsApp Web relies on a bidirectional WebSocket connection between the mobile app and desktop client. When the phone is off, this link collapses, forcing the desktop app to terminate sessions. The new mode circumvents this by storing session tokens in hardware-backed secure enclaves, a move that aligns with Android’s Keystore and Apple’s Secure Enclave.
However, this architecture creates a single point of failure. If a desktop device is lost or stolen, the cached keys could be extracted via side-channel attacks, as demonstrated in 2023 research on TPM (Trusted Platform Module) vulnerabilities. WhatsApp’s implementation reportedly uses 32-byte AES-256 keys, but the lack of