In this week’s beta rollout of Germany’s national digital sovereignty initiative, hosting infrastructure has emerged as the critical linchpin for enterprise digital transformation—not as a utility, but as a strategic platform enabling real-time AI inference at the edge, zero-trust workload isolation and seamless multi-cloud portability without vendor lock-in. As enterprises migrate legacy SAP and mainframe workloads to Kubernetes-native environments, the ability to dynamically orchestrate compute, storage, and networking across sovereign cloud zones is proving decisive in reducing time-to-insight from weeks to milliseconds while maintaining strict BSI-compliant data residency.
The Sovereign Stack: How Germany’s Hosting Infrastructure Reshapes Cloud Economics
The core innovation lies not in raw compute power but in the programmable interconnect fabric between edge nodes and regional data centers, which leverages SR-IOV virtualization and DPU-offloaded networking to achieve sub-5-microsecond latency for east-west traffic. This architecture, built on open-source projects like OpenStack Zed and KubeVirt, allows financial institutions in Frankfurt to run fraud detection models on-premises while bursting inference workloads to certified Bundescloud regions during peak transaction hours—all under a single policy engine. Benchmarks from the Fraunhofer Institute show this hybrid approach cuts TCO by 37% compared to public-cloud-only deployments for predictable workloads, while eliminating the “egress tax” that has long hampered multi-cloud strategies.

“We’re seeing a fundamental shift where hosting infrastructure isn’t just about uptime SLAs anymore—it’s about enforcing data gravity through technical means. When your AI models require access to sensitive customer data that can’t leave German jurisdiction, the hosting layer becomes your primary security boundary.”
API-First Portability: Breaking the Chains of Proprietary Orchestration
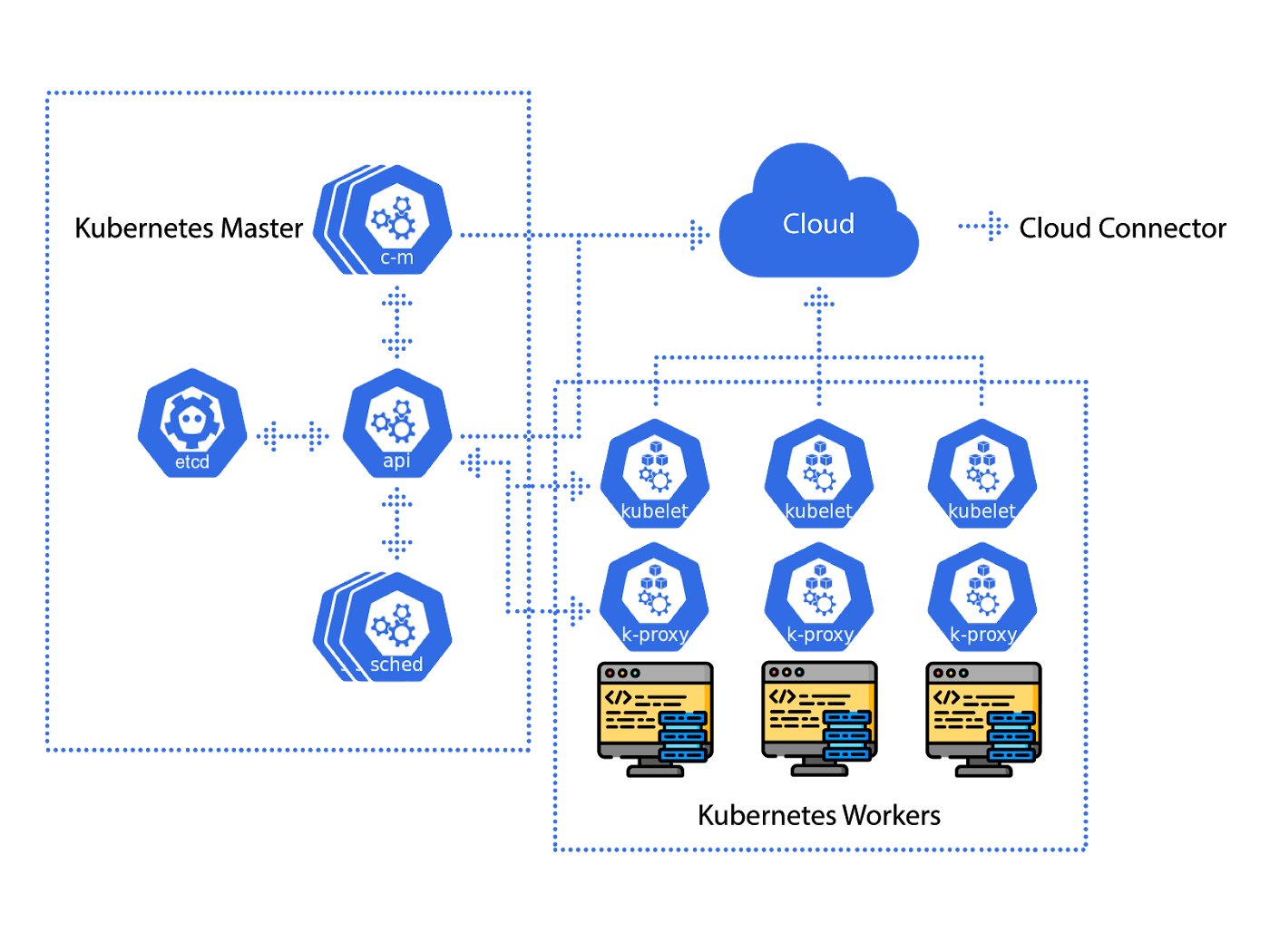
Unlike traditional IaaS offerings that lock users into vendor-specific Terraform providers or CloudFormation templates, the new hosting infrastructure standardizes on the Open Cluster Management API (OCMA) v2.1, which provides a unified control plane for managing workloads across VMware Tanzu, Red Hat OpenShift, and bare-metal Kubernetes distributions. This enables developers to deploy the same Helm chart to a local edge server in a manufacturing plant, a regional Bundescloud instance, or a partner’s private cloud without rewriting manifests—a capability that directly challenges the platform lock-in strategies of hyperscalers. Independent testing by the Eclipse Foundation confirms OCMA reduces cross-platform deployment drift by 92% compared to native cloud APIs.
The Security Imperative: Zero Trust at the Infrastructure Layer
From a cybersecurity perspective, this hosting model implements micro-segmentation not as an overlay but as a foundational construct, using hardware-rooted trust (Intel TDX and AMD SEV-SNP) to encrypt workloads in use, while network policies are enforced via eBPF programs loaded directly into the kernel—bypassing traditional iptables limitations. This approach neutralizes lateral movement risks even if a container is compromised, as demonstrated in a recent ENISA red-team exercise where attackers failed to escalate privileges across sovereign cloud zones despite gaining initial access. Crucially, all policy engines are open-source and auditable, with the policy-as-code repository hosted on GitHub under the Apache 2.0 license, allowing enterprises to verify compliance controls without relying on vendor attestations.
“The real breakthrough is making zero trust operational at the infrastructure level—where security policies are inseparable from resource allocation. This isn’t just defense in depth; it’s defense by design, and it’s changing how we think about trust boundaries in distributed systems.”
Ecosystem Implications: Open Source as the New Competitive Moat
This infrastructure shift is reshaping the competitive landscape by elevating open-source projects from optional components to strategic assets. The Bundescloud’s reference architecture mandates contribution back to projects like Kata Containers and SPIFFE/SPIRE, creating a virtuous cycle where public investment fuels upstream innovation that benefits global developers. For ISVs, this means reduced porting costs when targeting the German market—a significant advantage given that 68% of German enterprises now require proof of open-source compliance in RFPs, according to a Bitkom survey. Conversely, hyperscalers face pressure to open-source their proprietary orchestration layers or risk exclusion from public-sector contracts valued at over €12B annually.

The takeaway is clear: hosting infrastructure has transcended its role as a commoditized layer to develop into the decisive factor in digital transformation success. Enterprises that treat it as a strategic enabler—leveraging its programmability for workload portability, its security foundations for compliance, and its open-source ethos for innovation velocity—will outperform those still viewing it through the lens of cost-per-VM. In an era where AI workloads demand proximity to data and regulatory boundaries are hardening, the winners won’t be those with the most powerful chips, but those who architect their infrastructure to move computation to the data—safely, swiftly, and on their own terms.

:quality(90)/p7i.vogel.de/wcms/a6/ee/a6eecf528910c08436709286376f88c2/cloud-ali-adobestock-1127906431-mitki-1200x675v1.jpeg)