German enterprises are currently navigating a high-stakes collision between sophisticated state-sponsored cyber-adversaries and the EU’s tightening regulatory framework, specifically the NIS2 Directive. As of mid-May 2026, the mandate for granular incident reporting and supply chain transparency is forcing a total architectural overhaul of legacy IT infrastructures across the DACH region.
The cybersecurity landscape in Germany has shifted from a peripheral IT concern to a boardroom existential threat. This isn’t just about patching vulnerabilities. it is about systemic resilience in an era of AI-augmented polymorphic malware.
The NIS2 Pivot: Beyond Compliance Checkboxes
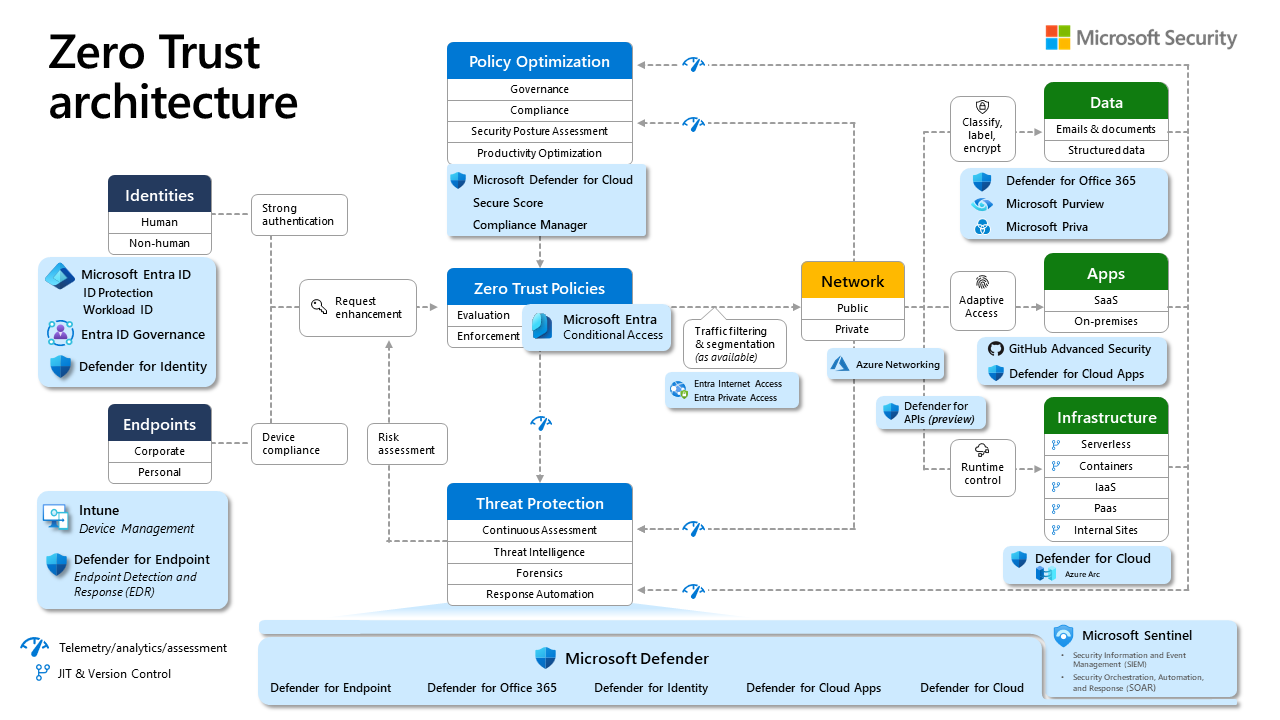
The implementation of the NIS2 Directive has effectively ended the era of “security through obscurity.” German firms are no longer just defending perimeters; they are being legally coerced into adopting Zero Trust architectures. The technical burden here is immense. Moving from a traditional VPN-based remote access model to a identity-centric Zero Trust Network Access (ZTNA) requires the deployment of sophisticated policy engines that verify every request, regardless of origin.
For the CTOs I speak with, the primary friction point isn’t the policy—it’s the technical debt. Many German Mittelstand companies are still running monolithic ERP systems that lack modern API hooks for OAuth 2.0 or OpenID Connect, making the integration of granular authentication protocols a nightmare of middleware engineering.
“The challenge isn’t just the regulation; it’s the architectural fragility of our legacy stack. When the law demands real-time reporting of a breach, but your internal telemetry logs are siloed in an on-premise server from 2014, you aren’t just non-compliant—you’re blind.” — Dr. Elena Fischer, Cybersecurity Architect at a leading German industrial IoT firm.
The AI Arms Race: Polymorphic Threats vs. Defensive LLMs
We are seeing a marked increase in AI-driven exploit generation. Threat actors are utilizing Large Language Models to automate the discovery of zero-day vulnerabilities in proprietary German software. By training models on specific codebase patterns, attackers can generate polymorphic code that evades traditional signature-based detection systems.
To combat this, the German tech sector is pivoting toward Managed Detection and Response (MDR) platforms that utilize behavioral analysis rather than static definitions. The core of this defense relies on high-velocity telemetry processing—ingesting petabytes of packet data and applying anomaly detection via NPU-accelerated edge devices.
The Technical Reality of Modern Defense
- Endpoint Detection: Shifting away from standard antivirus to EDR/XDR agents that monitor kernel-level process execution.
- Encryption Standards: A mandated transition to quantum-resistant cryptographic algorithms for long-term data archival.
- Supply Chain Transparency: The adoption of Software Bill of Materials (SBOM) to track every dependency in the CI/CD pipeline.
The Ecosystem War: Cloud Sovereignty vs. Hyperscale Efficiency
There is a persistent tension between the need for high-performance cloud computing—dominated by AWS, Azure, and GCP—and the German obsession with Datensouveränität (data sovereignty). While hyperscalers offer superior NPU-backed AI training clusters, the regulatory pressure to keep sensitive data within the EU is pushing firms toward hybrid cloud models.

This creates a “complexity tax.” Managing a hybrid environment where data resides in a local German data center while model training occurs in a US-based cloud requires sophisticated Kubernetes orchestration and complex end-to-end encryption schemas that can survive cross-cloud transit.
| Security Metric | Legacy On-Premise | Modern Hybrid Cloud |
|---|---|---|
| Threat Detection | Signature-based (Slow) | Behavioral AI (Real-time) |
| Access Model | VPN / Perimeter | Zero Trust (Identity-based) |
| Compliance | Manual Audit | Automated Continuous Compliance |
Why the “Human Firewall” is Failing
Despite the focus on NPU-accelerated encryption and robust identity management, the weakest link remains the social engineering attack. Phishing has evolved. We are seeing “deepfake” audio and video being used in business email compromise (BEC) attacks targeting German finance departments. The technical counter-measure? Implementing mandatory FIDO2 hardware-backed authentication for all internal accounts.
“Hardware-backed MFA is no longer optional. If your organization is still using SMS-based codes or simple password-plus-app tokens, you are effectively leaving the front door unlocked for a motivated state-actor.” — Markus Weber, Lead Security Researcher at the European Cyber Defense Initiative.
The move toward hardware security keys is a direct response to the sophisticated session-hijacking techniques that bypass traditional MFA. It forces a physical presence requirement that AI cannot yet spoof at scale.
The 30-Second Verdict: What This Means for Enterprise IT
If you are a German firm, the “compliance era” is over; the “operational resilience era” has begun. You must prioritize the following:
- Audit your SBOM: If you don’t know the origin of every open-source library in your stack, you are already compromised.
- Accelerate ZTNA: Remove the concept of “trusted networks.” Assume every node is a potential threat vector.
- Invest in Automated Reporting: Use CISA-aligned frameworks to automate the generation of compliance logs.
The market dynamics are clear: those who view cybersecurity as a technical foundation for innovation will outpace those who view it as a legal hurdle. In 2026, the code you write is only as good as the security that guards it. If your architecture isn’t built to be hostile to intruders, it is simply a matter of time before the breach occurs.

