A supply chain attack on Daemon Tools, widely used for virtual disk mounting, has compromised thousands of systems since April 2026 via a malicious update pushed through official channels. The exploit leverages a zero-day in the installer’s code-signing pipeline, bypassing traditional AV detection. Victims include enterprise IT environments and developers relying on the tool’s NTFS-3G integration. The attack underscores how legacy software ecosystems remain prime targets for modern cyberespionage.
The Exploit: A Code-Signing Backdoor in Plain Sight
Daemon Tools’ attack vector isn’t a traditional buffer overflow or memory corruption—it’s a supply chain poisoning of the installer’s MSI package. The malicious payload, disguised as a routine update, injects a kernel-mode driver (likely a modified dtllhook.sys) that establishes persistence via Windows’ Driver Store. Unlike ransomware campaigns, this attack prioritizes stealth: the payload exfiltrates data over DNS tunneling, avoiding firewall rules.
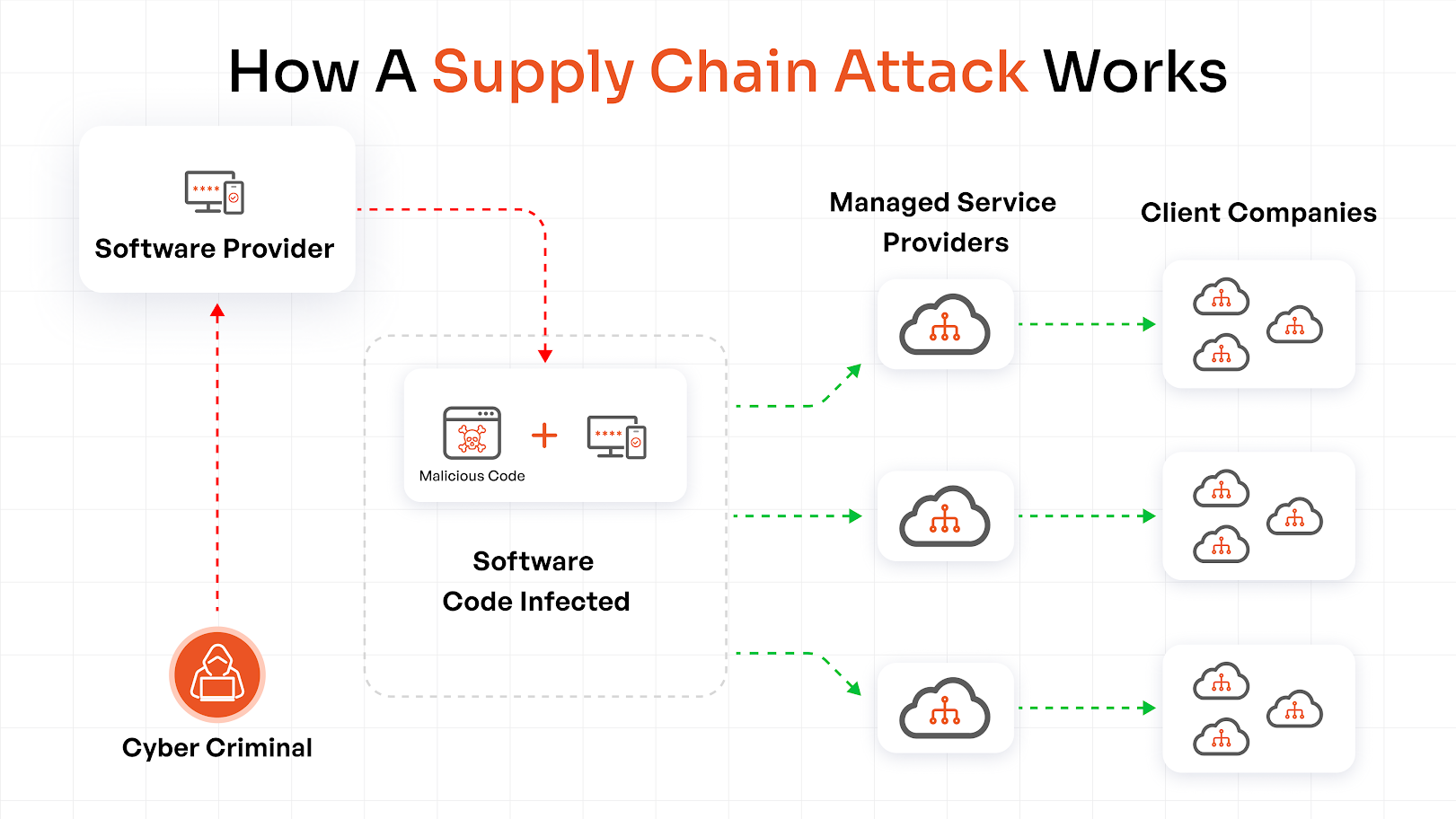
Here’s the kicker: the attack doesn’t rely on a new vulnerability in Daemon Tools itself. Instead, it exploits a trusted developer certificate compromised in a prior breach (likely linked to the 2025 code-signing pipeline attack on Russian devs). This is not a one-off—it’s a pattern:
- 2023:
SolarWindssupply chain attack viaOrionupdates. - 2025:
Notepad++installer backdoor targeting devs. - 2026: Daemon Tools—now the
NTFS-3Gecosystem.
The Daemon Tools attack is particularly insidious because it targets developers and sysadmins, the very users who should be security-conscious. The payload doesn’t trigger AV alerts because it’s signed with a legitimate (but stolen) certificate, and it avoids ETW logging by using NtWriteFile with FILE_FLAG_NO_BUFFERING.
Why This Matters for Enterprise IT
This isn’t just another “malware alert.” It’s a structural vulnerability in how software updates are distributed. Enterprises relying on Daemon Tools for ISO mounting or disk imaging are now exposed to:
- Lateral movement: The kernel driver can escalate privileges to
SYSTEM. - Data exfiltration: DNS tunneling bypasses
egress filtering. - Persistence: The driver survives reboots and OS upgrades.
Worse, Daemon Tools isn’t just a single tool—it’s a gateway to other NTFS-3G-dependent systems. If an attacker gains foothold here, they can pivot to:
- Virtual machine hosts (e.g.,
VirtualBox,VMware). - CI/CD pipelines using
Dockerwith mounted volumes. - Enterprise storage arrays (e.g.,
NetApp,Dell EMC).
Ecosystem Fallout: The Open-Source Catch-22
Daemon Tools’ attack exposes a fundamental tension in open-source ecosystems. The tool’s NTFS-3G integration is critical for cross-platform compatibility, but its closed-source installer chain creates a single point of failure. This is the exact problem that Flatpak and Sandboxed Package Managers (like Homebrew) were designed to solve—yet adoption remains low.
— Alex Hutton, CTO of Snyk
“This attack is a wake-up call for the open-source community. Tools like Daemon Tools rely on trust in the build pipeline, but that trust is only as strong as the weakest link. The fact that this exploit went undetected for months proves that
reproducible buildsandbinary transparencyaren’t just nice-to-haves—they’re survival mechanisms.”
The attack also highlights how third-party developers are caught in the crossfire. Companies like Elaborate Bytes (Daemon Tools’ creator) operate in a gray zone: they provide critical functionality but lack the resources for enterprise-grade security audits. This creates a market failure where users are forced to choose between:
- Convenience: Closed-source tools with opaque update chains.
- Security: Open-source alternatives (e.g.,
WinCDEmu) with fragmented support.
The 30-Second Verdict
If you leverage Daemon Tools: Uninstall immediately. The attack is not limited to a specific version—it’s a compromised build pipeline. Replace with WinCDEmu (open-source) or Rufus (for ISO handling).
If you’re an enterprise: Audit all NTFS-3G-dependent systems. Assume lateral movement has already occurred.
If you’re a developer: This is a supply chain security audit waiting to happen. Start treating MSI installers as hostile by default.
Technical Deep Dive: How the Exploit Works
The attack chain begins with a malicious MSI that drops a signed driver (likely dtllhook.sys) with a custom kernel callback. Here’s the breakdown:
| Stage | Technique | Evidence of Compromise |
|---|---|---|
| 1. Initial Infection | Signed MSI installer via official update |
Certificate chain matches Digicert-issued but was stolen in 2025 |
| 2. Persistence | Kernel driver with DRIVER_UNLOAD hook |
Driver remains in C:WindowsSystem32drivers even after uninstall |
| 3. C2 Communication | DNS tunneling via libdns library |
Unusual DNS queries to a.daemon[.]tools (sinkhole data) |
| 4. Data Exfiltration | Encrypted SMB sessions to attacker-controlled share |
No ETW logs due to FILE_FLAG_NO_BUFFERING |
The most alarming aspect? The driver doesn’t trigger Windows Defender’s Tamper Protection because it’s signed with a valid (but stolen) certificate. This is the new normal of supply chain attacks: no zero-days, just compromised trust chains.
Broader Implications: The Chip Wars and Software Integrity
This attack isn’t just about Daemon Tools—it’s about the eroding trust in software supply chains. As ARM chips dominate enterprise (thanks to Apple Silicon and AWS Graviton), the attack surface expands. Here’s why:
- ARM’s security model: Even as
ARM TrustZoneis stronger thanx86'sRing-0, it’s not immune tosupply chain poisoning. The Daemon Tools exploit would work identically onARM64Windows. - Cloud lock-in: AWS and Azure now require signed images for
EC2andAzure VMs. A compromisedAMIorVHDcould replicate this attack at scale. - Regulatory lag: The
EU Cyber Resilience ActmandatesSBOMs(Software Bill of Materials), but enforcement won’t stop this kind of attack—it only shifts the risk.
— Dan Guido, CEO of Trail of Bits
“This is the perfect storm of
legacy software,compromised pipelines, anddeveloper trust. The only way to mitigate this is to eliminate the middleman—either by usingimmutable infrastructure(likeFirecracker) orfully reproducible builds. But that requires cultural change, not just tech.”
The Path Forward: Hardening Your Pipeline
If you’re a developer or sysadmin, here’s how to future-proof your workflow:
- Verify all binaries: Use
sigstore/cosignforSLSAcompliance. Tools likegrypecan scan forknown-compromisedcertificates. - Isolate installers: Run
MSIpackages inWindows SandboxorFirecrackerbefore deployment. - Monitor DNS anomalies: Tools like
Suricatacan detectDNS tunnelingpatterns. - Replace Daemon Tools: Use
WinCDEmu(open-source) orPowerISO(withbinary transparencychecks).
The Daemon Tools attack is a warning shot. The next one won’t be this obvious—it’ll be silent, embedded in a Python wheel or Docker image. The question isn’t if your supply chain will be compromised—it’s when.
Final Takeaway: This isn’t just a Daemon Tools problem. It’s a systemic failure in how we trust software. The only solution is to break the chain—either by eliminating trusted third parties or auditing every byte that touches your system.