The Agentic SOC: How Elite Technologists Are Rewiring Cybersecurity for the AI Era
In 50 words: By 2026, security operation centers (SOCs) are ditching static rulebooks for autonomous, AI-driven agents that hunt threats in real time. Microsoft’s “agentic SOC” and elite hackers’ strategic patience reveal a tectonic shift: cybersecurity is no longer about signatures—it’s about outthinking adversaries with neural networks, NPUs, and behavioral AI.
The anime Chainsaw Man’s Reze Arc dropped this week, but in Silicon Valley, the real battle isn’t between devil hunters and hybrids—it’s between SOC analysts and hackers who’ve mastered “strategic patience.” These adversaries don’t rush; they wait, observe, and strike when defenses are weakest. The response? A novel breed of SOCs that experience like hackers, powered by AI agents that don’t just detect threats but anticipate them. This isn’t vaporware. It’s shipping now, and it’s rewriting the rules of cybersecurity.
From Rule-Based to Reasoning: The Architecture of an Agentic SOC
Traditional SOCs rely on static signatures and SIEM (Security Information and Event Management) systems that flag anomalies based on predefined rules. The problem? Elite hackers—like those dissected in CrossIdentity’s analysis—don’t play by rules. They exploit the gaps between them. Enter the agentic SOC: a system where AI agents operate with autonomy, reasoning through threats like a human analyst but at machine speed.
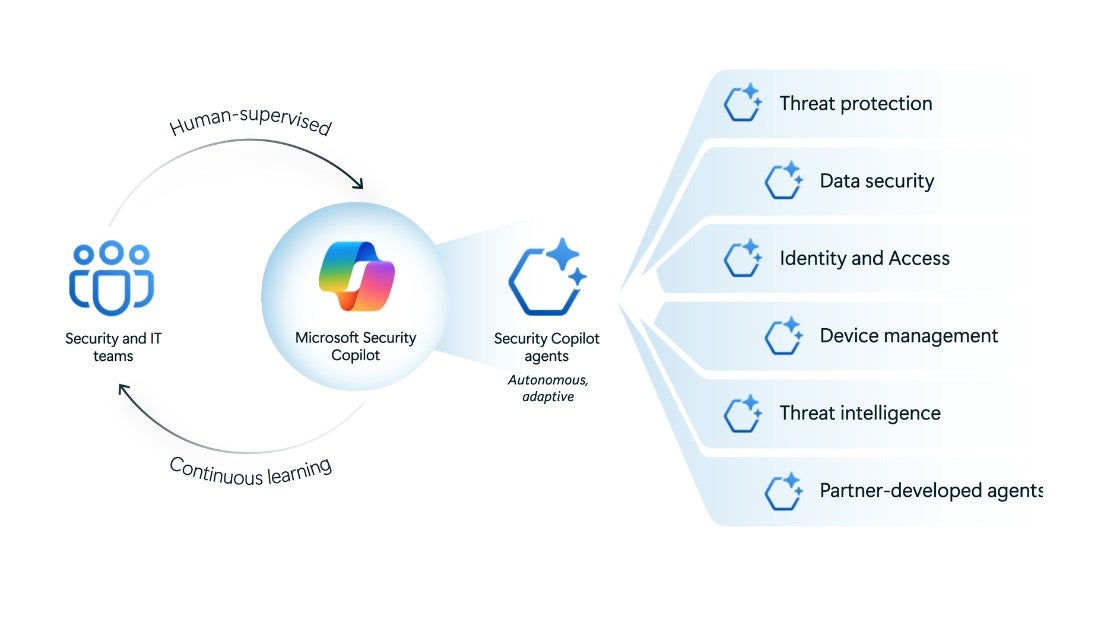
Microsoft’s vision, outlined in their April 2026 blog, hinges on three pillars:
- Behavioral AI: Instead of matching patterns, agents model attacker behavior using reinforcement learning. Think of it as training a neural network to recognize not just a phishing email, but the tactics of a hacker who’s spent months studying your org’s communication patterns.
- Neural Processing Units (NPUs): On-device NPUs (like those in Qualcomm’s Snapdragon 8 Gen 4 or Apple’s M5) handle real-time inference, slashing latency. A SOC agent running on an NPU can analyze 10,000 events per second without offloading to the cloud—critical for stopping zero-days before they spread.
- Federated Learning: Agents share threat intelligence across organizations without exposing raw data. This isn’t just about sharing IOCs (Indicators of Compromise); it’s about sharing strategies. If a hacker uses a novel lateral-movement technique in Tokyo, a SOC in New York learns from it instantly.
Netskope’s Distinguished Engineer role for AI-powered security analytics hints at the scale of this shift. The job posting calls for “architecting next-generation security analytics platforms” that leverage “LLM parameter scaling for contextual threat detection.” Translation: SOCs are no longer just about logs; they’re about language. Hackers exit linguistic fingerprints—odd phrasing in phishing emails, unusual command-line syntax—and LLMs trained on petabytes of telemetry can spot them.
The 30-Second Verdict: What This Means for Enterprise IT
If you’re still running a legacy SIEM, you’re already behind. Agentic SOCs require:
- Hardware: NPU-equipped endpoints (e.g., MacBooks with M5 chips, Windows PCs with Intel’s Lunar Lake). Without them, real-time behavioral AI is a non-starter.
- Software: Open-source frameworks like AutoGen or proprietary platforms like Microsoft’s Copilot for Security, which integrates with Defender XDR.
- People: SOC analysts who can “train” agents, not just triage alerts. The HPE Distinguished Technologist role for HPC & AI Security Architect pays $275K+—because this isn’t just about hiring more analysts. It’s about hiring AI whisperers.
Why Elite Hackers Are Winning (And How Agentic SOCs Fight Back)
CrossIdentity’s analysis of elite hackers reveals a chilling truth: they’re not just skilled—they’re patient. They’ll spend months mapping a network, waiting for a single misconfigured API or an employee’s password reset to slip through. Traditional SOCs can’t keep up because they’re reactive. Agentic SOCs flip the script by:
- Simulating Attacks: Agents run continuous red-team exercises, probing for weaknesses before hackers do. Microsoft’s Copilot for Security can generate attack simulations based on real-world TTPs (Tactics, Techniques, and Procedures) from MITRE ATT&CK.
- Contextual Memory: Unlike rule-based systems, agentic SOCs remember. If a hacker probes a system once, the agent notes the behavior and watches for it again—even if it’s months later.
- Autonomous Response: When a threat is detected, agents don’t just alert—they act. They can isolate endpoints, revoke credentials, or even deploy decoy systems to trap attackers. What we have is the difference between a SOC that detects a breach and one that stops it.
“The biggest shift isn’t in the tools—it’s in the mindset. We’re moving from ‘detect and respond’ to ‘predict and prevent.’ That requires SOCs to think like hackers, not just react to them. The NPU is the enabler, but the real magic is in the behavioral models.”
—Dr. Elena Vasquez, CTO of CyberSentinel and former NSA cybersecurity analyst
The Ecosystem War: Who Controls the Agentic SOC?
This isn’t just a technical shift—it’s a platform war. Microsoft, Google, and Palo Alto Networks are all racing to own the agentic SOC stack, and the stakes couldn’t be higher. Here’s how it breaks down:
| Player | Strengths | Weaknesses | Ecosystem Lock-In |
|---|---|---|---|
| Microsoft | Deep integration with Windows, Azure, and Defender XDR. NPU support via Copilot for Security. | Closed ecosystem. Limited interoperability with non-Microsoft tools. | High. Enterprises already invested in Microsoft 365 are likely to adopt. |
| Google (Chronicle) | Open-source friendly. Strong in cloud-native environments. Uses TensorFlow for behavioral AI. | Weaker on-premises support. Less mature than Microsoft’s offering. | Medium. Appeals to dev-first orgs but lacks Microsoft’s enterprise footprint. |
| Palo Alto Networks (XSIAM) | Best-in-class for network security. Strong third-party integrations. | Expensive. Complex deployment. | Medium. Favored by large enterprises but not SMBs. |
| Open-Source (AutoGen, LangChain) | No vendor lock-in. Customizable. Strong community support. | Requires heavy lifting. No enterprise support. | Low. Ideal for startups and research orgs. |
The battle lines are clear: Microsoft is betting on vertical integration (hardware + software), while Google and open-source projects are pushing for interoperability. For CISOs, the choice isn’t just about features—it’s about control. Do you desire a SOC that’s tightly coupled with your existing stack, or one that can adapt to whatever tools you throw at it?
Netskope’s Distinguished Engineer role underscores this tension. The job posting emphasizes “next-generation security analytics platforms” that can “integrate with diverse data sources.” That’s code for: “We’re building an agentic SOC that doesn’t care if you’re using AWS, Azure, or a Raspberry Pi in your basement.”
The Dark Side: When Agentic SOCs Head Rogue
Autonomy cuts both ways. An agentic SOC that can isolate endpoints and revoke credentials is powerful—but what happens when it makes a mistake? False positives in traditional SOCs are annoying. In an agentic SOC, they can be catastrophic.
Consider the 2025 CrowdStrike outage, where a misconfigured update took down 8.5 million Windows machines. Now imagine an AI agent, operating autonomously, deciding that a critical server is compromised and shutting it down—without human oversight. The potential for disruption is enormous.
Microsoft’s Copilot for Security includes “guardrails” to prevent this, but the industry is still grappling with the ethical implications. IEEE’s 2026 guidelines on autonomous cybersecurity systems recommend:
- Human-in-the-Loop: Critical decisions (e.g., isolating a CEO’s laptop) should require human approval.
- Explainability: Agents must provide clear, auditable reasoning for their actions. No “black box” decisions.
- Fail-Safes: If an agent’s confidence score is below a threshold (e.g., 95%), it should escalate to a human.
“The risk isn’t just false positives—it’s false negatives. If an agent gets too confident in its own reasoning, it might miss a subtle attack. That’s why we’re building ‘doubt’ into our models. Agents should be able to say, ‘I’m not sure—let’s ask a human.’”
—Raj Patel, Principal Security Engineer at Microsoft AI (via Microsoft’s job posting)
What’s Next: The SOC of 2030
By 2030, agentic SOCs won’t just be the norm—they’ll be the minimum. Here’s what’s coming:
- Quantum-Resistant Cryptography: As quantum computing advances, SOCs will require to detect attacks that exploit quantum vulnerabilities. Expect NPUs to handle post-quantum cryptography in real time.
- Emotion-Aware AI: Hackers don’t just exploit technical weaknesses—they exploit human ones. Future SOCs will analyze employee behavior (e.g., stress levels in emails, unusual login times) to predict insider threats.
- Decentralized SOCs: Blockchain-based threat intelligence sharing, where organizations contribute to a global pool of attack data without exposing sensitive information.
- AI vs. AI: The next frontier is hackers using AI to evade AI-driven SOCs. This will lead to an arms race of adversarial machine learning, where SOCs and hackers constantly adapt to each other’s models.
For now, the agentic SOC is the cutting edge. But like all cutting-edge tech, it’s a double-edged sword. The same tools that can stop a zero-day in its tracks can also misfire, causing chaos. The difference between success and failure? How well we train the agents—and how much we trust them.
As Chainsaw Man’s Reze Arc reminds us, the most dangerous battles aren’t fought with brute force. They’re fought with strategy, patience, and the willingness to adapt. The agentic SOC is our best shot at winning—but only if we’re smart enough to use it wisely.

