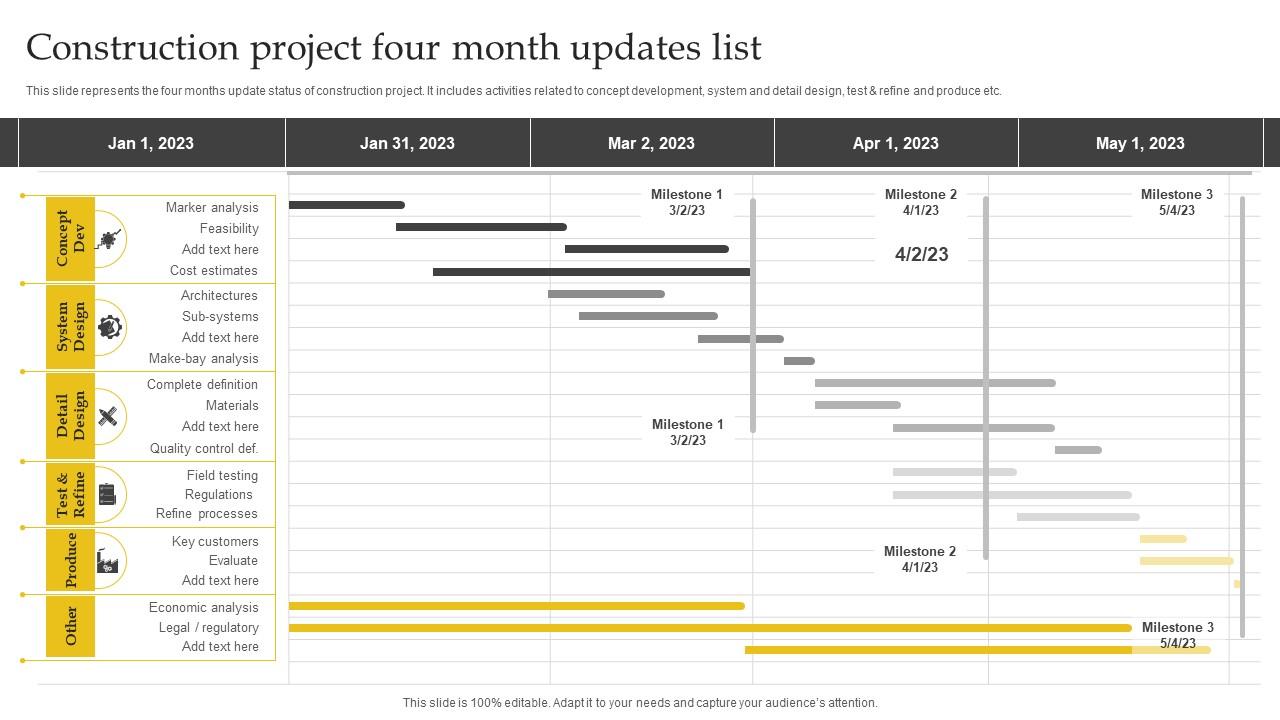
The Free Software Foundation (FSF) has concluded a four-month development sprint involving all four of its core teams to advance the open-source ecosystem. This coordinated push focuses on strengthening user autonomy and software freedom, countering the industry trend toward proprietary silos and restrictive licensing in the AI era.
Let’s be clear: in the current climate of “open-core” marketing and “open-weights” AI—which is often just proprietary software with a fancy coat of paint—the FSF is playing a different game. While the valley is obsessed with capturing the next billion users through walled gardens, the FSF is focused on the plumbing of digital sovereignty. Their recent activity isn’t about a single “product launch” because the FSF doesn’t sell products; they defend a philosophy. But that philosophy is currently facing an existential threat from the rapid integration of non-free binary blobs into the exceptionally heart of the Linux kernel and the rise of proprietary LLM-integrated operating systems.
The War Against the Binary Blob
A critical pillar of the FSF’s recent efforts involves the ongoing battle against proprietary firmware—the “binary blobs” that hide within the Linux kernel. For the uninitiated, these are opaque chunks of code that the community cannot audit, modify, or verify. When your hardware relies on a blob for WiFi or power management, you aren’t the owner of your machine; you are a tenant on the manufacturer’s land.
The FSF’s push toward “Libreboot” and “Coreboot” alternatives aims to replace these blobs with open-source equivalents. This is a high-stakes engineering challenge. We are talking about the lowest levels of the stack—the UEFI and BIOS—where a single misplaced bit can brick a motherboard. By prioritizing the removal of these blobs, the FSF is effectively trying to build a “Trusted Computing” model that actually trusts the user, not the vendor.
This isn’t just about purity; it’s about security. A binary blob is a perfect hiding spot for a backdoor. If the source code isn’t available for peer review, the only way to verify the blob’s behavior is through reverse engineering—a tedious process that is often a game of cat-and-mouse with obfuscated code.
LLMs and the Fresh Frontier of Software Freedom
The most pressing “information gap” in the current discourse is the intersection of Large Language Models (LLMs) and the GNU General Public License (GPL). As AI agents begin to write, commit, and merge code into open-source repositories, the definition of “author” is blurring. If an AI trained on GPL-licensed code generates a snippet for a proprietary project, is that a copyright violation?

The FSF is currently analyzing how to adapt the GNU GPL to address synthetic code generation. The risk is a massive “copyright laundering” operation where proprietary firms use AI to strip the license requirements from open-source logic, effectively stealing the labor of thousands of volunteer developers.
The 30-Second Verdict: Why This Matters for Devs
- Sovereignty: Reducing reliance on proprietary firmware prevents vendor lock-in at the hardware level.
- Legal Precedent: The FSF’s stance on AI-generated code will likely dictate future litigation regarding copyright and LLMs.
- Security: Auditable code is the only true defense against supply-chain attacks and state-sponsored backdoors.
Bridging the Ecosystem: ARM vs. X86 and the Open Hardware Push
The shift toward ARM-based architecture in the consumer space (led by Apple Silicon and Qualcomm’s Snapdragon X Elite) has complicated the FSF’s mission. ARM’s licensing model is notoriously closed. While x86 has its issues, the move toward highly integrated SoCs (System on a Chip) makes it harder to achieve a fully “free” system because the hardware itself is designed to resist third-party firmware.
To counter this, the FSF is championing RISC-V. Unlike ARM or x86, RISC-V is an open standard instruction set architecture (ISA). By decoupling the hardware specification from the company selling the chip, RISC-V allows for a truly open stack from the transistor to the text editor.
The technical friction here is immense. Writing a compiler (like GCC) for a new ISA requires grueling optimization to ensure that the high-level language translates efficiently to the machine code. The FSF’s work in this area ensures that “open hardware” isn’t just a buzzword, but a functional reality that can compete with the performance of proprietary chips.
The Strategic Outlook: Open Source vs. Open Freedom
We must distinguish between “Open Source” and “Free Software.” The former is often a business strategy—companies give away the software to sell the cloud services (the “SaaS-ification” of open source). The latter, championed by the FSF, is a human rights issue. The FSF’s four-month sprint is a reminder that the goal isn’t just “free as in beer” (zero cost), but “free as in speech” (liberty).
As we move deeper into 2026, the tension between the IEEE standards and proprietary extensions will only grow. The FSF is positioning itself as the last line of defense against a world where your computer is essentially a terminal for someone else’s cloud.
The result of this four-month push is not a shiny new app or a flashy API. It is the quiet, rigorous work of patching kernels, refining licenses, and auditing firmware. It is the unglamorous work that ensures that in ten years, we still have the right to know exactly what our machines are doing when we press the power button.