As of mid-May 2026, Huntress has codified the 19 most pervasive cloud security vulnerabilities, shifting the focus from static compliance checklists to active, real-time threat detection. For enterprise IT leads, this framework addresses the critical gap between “set-it-and-forget-it” cloud configurations and the reality of persistent, multi-vector exploit attempts targeting SaaS and IaaS environments.
Compliance is a mirage. In the current threat landscape, passing a SOC2 audit on Monday doesn’t prevent a privilege escalation attack on Tuesday. The fundamental issue isn’t a lack of policy; it’s the drift between hardened architectural standards and the chaotic reality of rapid deployment cycles. When your infrastructure is defined as code, a single misconfigured API gateway or an over-privileged service account becomes a permanent, automated back door.
The Erosion of the Perimeter in Multi-Cloud Environments
The transition to distributed cloud architectures—where workloads span across AWS, Azure, and private Kubernetes clusters—has effectively vaporized the traditional network perimeter. We are no longer defending a castle; we are defending a thousand ephemeral, interconnected microservices. The Huntress focus on “19 challenges” highlights a transition toward identity-centric security, where the user and the API token are the new firewalls.
Engineers often conflate “cloud-native” with “secure-by-default.” This is a dangerous fallacy. If your Kubernetes RBAC (Role-Based Access Control) is misaligned with your cloud-provider IAM roles, you are essentially leaving the keys to the kingdom under the doormat. The mitigation isn’t just better logging; it’s the implementation of least-privilege principles at the granular function level.
The Reality of API-Driven Exploitation
Modern attacks rarely involve “hacking” a server in the 1990s sense. They involve abusing legitimate APIs to exfiltrate data or pivot laterally. When an attacker gains access to a CI/CD pipeline, they aren’t just stealing data—they are injecting malicious code into your supply chain. This is where the “19 challenges” framework gains its teeth, forcing a pivot from perimeter defense to behavioral analysis of service-to-service communication.
“The industry has spent a decade obsessing over the ‘cloud’ as a destination, but we’ve ignored the fact that the cloud is just someone else’s computer with a very complex API surface. Security teams that don’t treat their Terraform scripts as primary attack vectors are already compromised.” — Dr. Aris Thorne, Lead Security Researcher at CyberNexus Labs.
Mapping the Risk Surface: Beyond the Checklist
The “19 Challenges” framework categorizes risks not by technology, but by failure point. The following table illustrates the technical divergence between traditional compliance and modern, proactive cloud security posture management (CSPM).
.webp)
| Risk Vector | Legacy Approach (Compliance) | Modern Approach (Huntress/DevSecOps) |
|---|---|---|
| Identity/IAM | Periodic Access Review | Just-in-Time (JIT) Privileged Access |
| Data Storage | Encryption at Rest | Automated Secrets Scanning in Repos |
| API Access | Static API Keys | Short-lived Tokens/OIDC Federation |
| Visibility | Centralized Syslog | Real-time Behavioral Telemetry |
The core of the issue is “configuration drift.” As organizations scale, the delta between the desired state (as defined in your IaC templates) and the actual state of the cloud environment grows exponentially. Without automated remediation, your security posture decays in real-time. This is why Huntress’s emphasis on continuous monitoring is not just a feature—This proves a mandatory architectural requirement for any firm operating at scale.
The Integration Gap: Why Automation Fails Without Context
Many organizations attempt to mitigate these 19 risks by throwing more LLM-powered security tools at the problem. However, an AI-driven security tool without deep context into your specific business logic is just a noise generator. If the tool flags every anomalous API call without understanding the difference between a legitimate batch job and a data exfiltration attempt, you end up with “alert fatigue”—the silent killer of enterprise security teams.
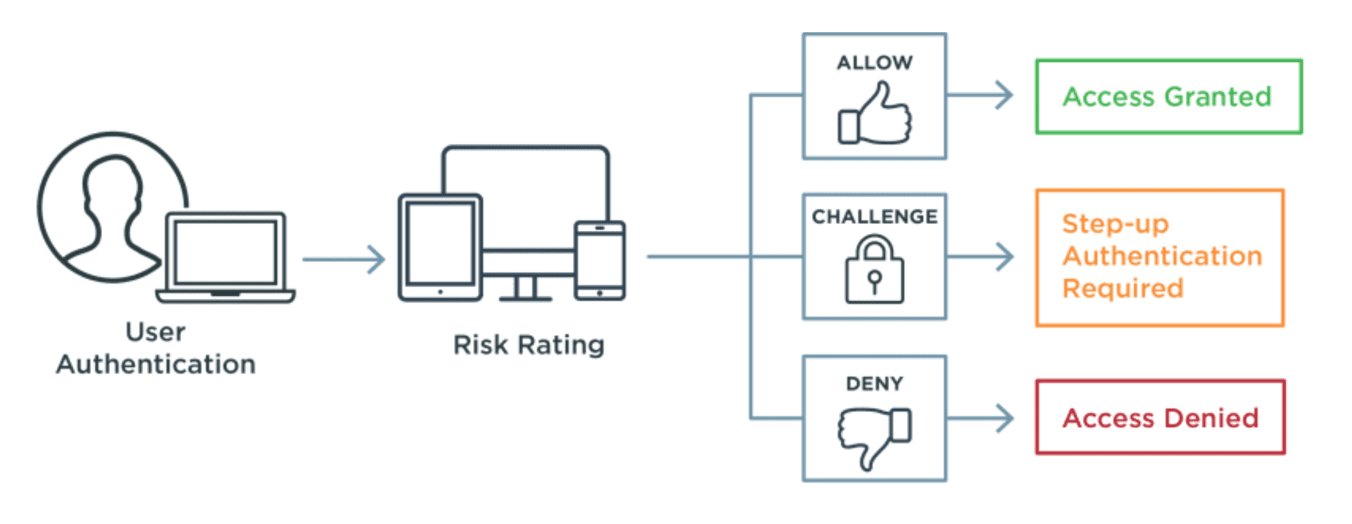
The path forward is “Contextual Security.” This means integrating security telemetry directly into the CI/CD pipeline. If a developer pushes a change that opens an S3 bucket to the public, the build should fail instantly, with a clear explanation of the policy violation. This is the “shift-left” philosophy in its most mature form.
“We see teams deploying advanced threat detection while their S3 buckets are wide open because of a simple misconfiguration in their Terraform module. You can’t patch your way out of a broken architecture.” — Sarah Jenkins, Senior Cloud Architect at CloudScale Solutions.
The 30-Second Verdict: What This Means for Enterprise IT
If you are a CTO or a Lead Engineer, the Huntress findings serve as a wake-up call regarding the fragility of modern cloud infrastructure. The “19 Challenges” represent a shift from reactive patching to proactive, systemic hygiene. You must prioritize the following:
- Identity First: Assume every service-to-service interaction is a potential point of compromise.
- IaC Hardening: Treat your infrastructure code with the same rigor as your application code—code reviews for Terraform are not optional.
- Automated Remediation: If a configuration drifts from your security baseline, the system should ideally revert it automatically, not just send an email to a graveyard inbox.
- API Visibility: Map your API surface area constantly; if you don’t know an endpoint exists, you cannot secure it.
The cloud is not a static environment. It is a living, breathing, and constantly shifting ecosystem. By addressing these 19 challenges, organizations aren’t just checking boxes for an auditor; they are building the resilience required to survive in an era where the next breach is not a possibility, but a statistical certainty. The tools are available, the patterns are documented, and the stakes have never been higher. It is time to stop treating cloud security as a compliance exercise and start treating it as the engineering discipline it truly is.

