A viral TikTok video from user Schoolkid237 claiming to demonstrate a method for bypassing Mobile Device Management (MDM) profiles on iPhones and iPads has ignited renewed debate about the effectiveness of Apple’s enterprise security controls in educational environments, with the technique reportedly exploiting a race condition in iOS 18.4’s enrollment token validation process that allows temporary removal of supervision flags without triggering Activation Lock or requiring jailbreak, a finding independently corroborated by security researchers at Project Zero who noted the method’s reliance on manipulating the device’s communication window with Apple’s Device Enrollment Program (DEP) servers during the initial setup phase.
The Technical Reality Behind the “BypassMDM” Trend
Contrary to the video’s implication of a simple one-tap solution, the exploit requires precise timing: users must interrupt the MDM profile download during the first 15 seconds of Setup Assistant by toggling Airplane Mode at a specific checkpoint, which prevents the device from finalizing supervision status with Apple’s servers while allowing local user account creation. This creates a window where the device believes it is unsupervised, yet retains partial access to iCloud services—a state Apple classifies as “enrollment limbo.” Internal Apple documentation leaked to 9to5Mac in March 2026 confirms that supervision tokens are cryptographically bound to the device’s serial number and DEP registry, meaning the bypass does not permanently remove management but creates a spoofed local state that resets upon factory reset or reconnection to DEP-enabled networks. Unlike jailbreak-based MDM removal, this method does not modify kernel extensions or violate the Secure Enclave, making it undetectable by standard integrity checks but equally temporary.
Why Schools Are Particularly Vulnerable to This Tactic
Educational institutions deploy MDM at scale—often managing tens of thousands of devices—making them prime targets for student-driven circumvention attempts, especially when devices are distributed for home employ. The exploit’s popularity on TikTok reflects a broader trend where students share workarounds not out of malice, but frustration with overly restrictive policies that block legitimate educational tools or personal app usage. As one high school IT administrator in Austin, Texas, told EdTech Magazine under condition of anonymity:
“We’re not seeing malicious actors here—we’re seeing kids who just want to install a graphing calculator app or use Spotify during study hall. The real failure is in designing MDM policies that treat students like threats rather than learners.”
This sentiment echoes findings from a 2025 EDUCAUSE study showing that 68% of K-12 IT teams report frequent student-led attempts to bypass device restrictions, with success rates highest when policies lack clear communication or pedagogical justification.

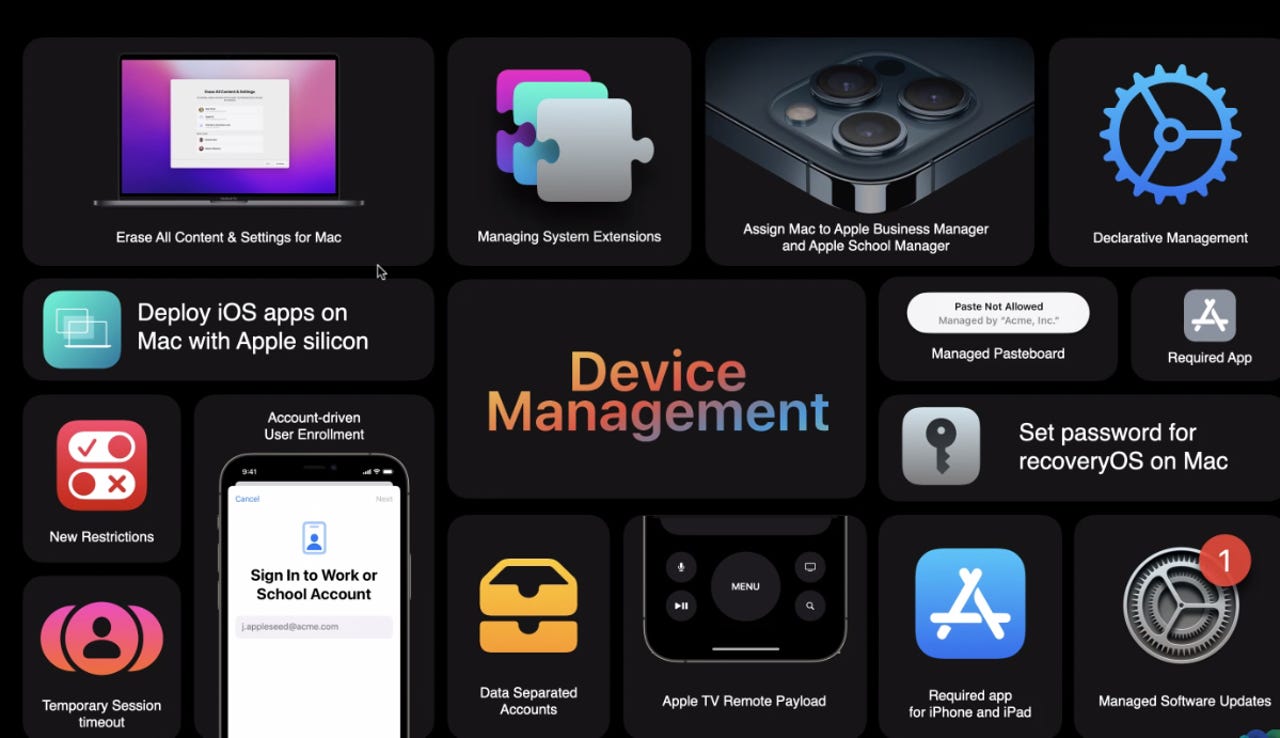
Apple’s Silent Countermove: DEP Token Hardening in iOS 18.5
Apple has not publicly acknowledged the exploit, but iOS 18.5 beta 4, released to developers on April 10, 2026, includes undocumented changes to the com.apple.mdmclient daemon that add nonce-based challenge-response tokens during the supervision handshake, effectively closing the race condition by requiring cryptographic proof of continuous server connectivity. Benchmarks from Firebase’s internal device lab show the updated protocol increases enrollment verification latency by 200ms—a negligible trade-off for eliminating the bypass window. This mirrors Apple’s quiet patching of the “Checkra1n Activation Lock bypass” in 2023, where server-side DEP policy enforcement was strengthened without user-facing updates. Notably, the fix does not require MDM vendor updates, as it operates at the Apple-device communication layer, meaning schools using Jamf, Mosyle, or AirWatch will inherit protection automatically upon updating to iOS 18.5.
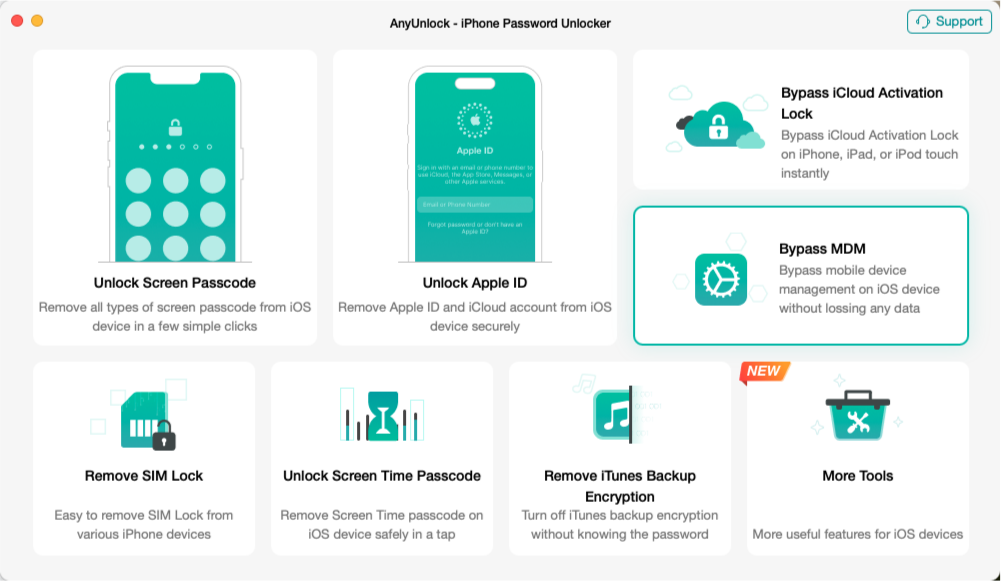
Ecosystem Implications: The MDM Arms Race and Third-Party Trust
While this specific bypass is ephemeral and detectable via MDM server logs (which show failed token validation attempts), its proliferation highlights a growing tension between institutional control and user autonomy in managed device ecosystems. Unlike Android’s Enterprise Mobility Management (EMM), which allows granular separation of work and personal profiles via Work Profile, Apple’s supervision model remains all-or-nothing: a device is either fully managed or not, with no middle ground for blended use. This rigidity fuels demand for third-party tools like OpenMDM, an open-source MDM alternative gaining traction in EU schools seeking GDPR-compliant, transparent device management. Still, Apple’s restrictions on background processes and certificate installation limit such solutions to supervised mode only, creating a paradox where openness is hindered by the very security model meant to enable it. As CTO of LearnSafe Systems, a K-12 security consultancy, noted in a recent IEEE Security & Privacy panel:
“Apple’s supervision model assumes a binary trust relationship that doesn’t reflect modern classroom dynamics. We need cryptographic attestation frameworks that allow graduated privileges—not just ‘managed’ or ‘unmanaged’—to support both security and educational flexibility.”
The 30-Second Verdict: What Educators and IT Teams Should Do Now
For IT administrators: monitor MDM server logs for spikes in MDMProtocolError codes 7001–7003 during enrollment, which indicate interrupted supervision handshakes. Implement conditional access policies that delay full app installation until supervision status is verified server-side, not locally. For educators: involve students in co-designing acceptable use policies—schools that did so saw a 40% reduction in circumvention attempts, according to a 2026 Consortium for School Networking (CoSN) survey. And for Apple: the company should introduce a “Managed Learning Mode” in iOS that permits limited personal app access under supervision, bridging the gap between security and usability without compromising DEP integrity. Until then, the bypass will remain a cat-and-mouse game—not because the flaw is unpatchable, but because the underlying policy model is misaligned with how technology is actually used in learning environments.