iPhones produce black screenshots in apps like Netflix or Apple TV due to High-bandwidth Digital Content Protection (HDCP) and Digital Rights Management (DRM). These protocols prevent unauthorized recording by isolating protected video streams from the system’s screenshot capture API, ensuring content remains encrypted from the server to the display.
For the average user, this is a nuisance. For those of us who live in the kernel, it is a masterclass in hardware-software synergy. When you trigger that volume-up and side-button combo, you aren’t just taking a picture of your screen; you are requesting a dump of the current framebuffer. But in the case of premium streaming, the framebuffer is a lie.
This isn’t a “bug” or a glitch rolling out in this week’s beta. It is a foundational architectural decision designed to protect the intellectual property of studios that treat a single leaked 4K frame as a catastrophic security breach.
The Invisible Wall: How HDCP Hijacks Your Framebuffer
To understand why your screenshot is a void, we have to talk about the IEEE standards regarding digital content. The core mechanism at play is HDCP (High-bandwidth Digital Content Protection). In a traditional computing environment, the GPU renders a frame, stores it in a memory buffer, and the display controller reads that buffer to light up pixels on your OLED screen.
When a DRM-protected app like Netflix is active, the OS establishes a “Secure Video Path.” Instead of the decrypted video frames sitting in a general-purpose memory region accessible by the system’s screenshot utility, they are routed through a protected pipeline. The decryption happens within the SoC (System on a Chip), specifically leveraging the ARM-based architecture’s ability to isolate memory segments.
When the iOS screenshot API calls for a capture of the screen, it asks the system for the contents of the visible layers. However, the secure layer—the one containing the movie—is flagged as “protected.” The system simply ignores this layer or replaces it with a black placeholder before the final image is compressed into a JPEG or PNG. You are effectively taking a photo of the “wallpaper” behind the video, but since the video app is full-screen, the wallpaper is also hidden. Result: total darkness.
The 30-Second Verdict
- The Cause: HDCP and FairPlay DRM.
- The Mechanism: Secure Video Path isolation.
- The Result: Screenshot APIs are denied access to the protected memory buffer.
- The Bypass: Virtually impossible on non-jailbroken hardware due to SoC-level enforcement.
FairPlay vs. Widevine: The Architecture of Digital Lockdown
Apple uses its proprietary FairPlay Streaming (FPS) to handle this, even as Android devices typically rely on Google’s Widevine. While they achieve the same goal—preventing you from stealing a scene from Stranger Things—their implementation depths vary. Widevine, for instance, has different “Levels” (L1, L2, L3). L1 is the gold standard, requiring a Hardware-backed Trusted Execution Environment (TEE).
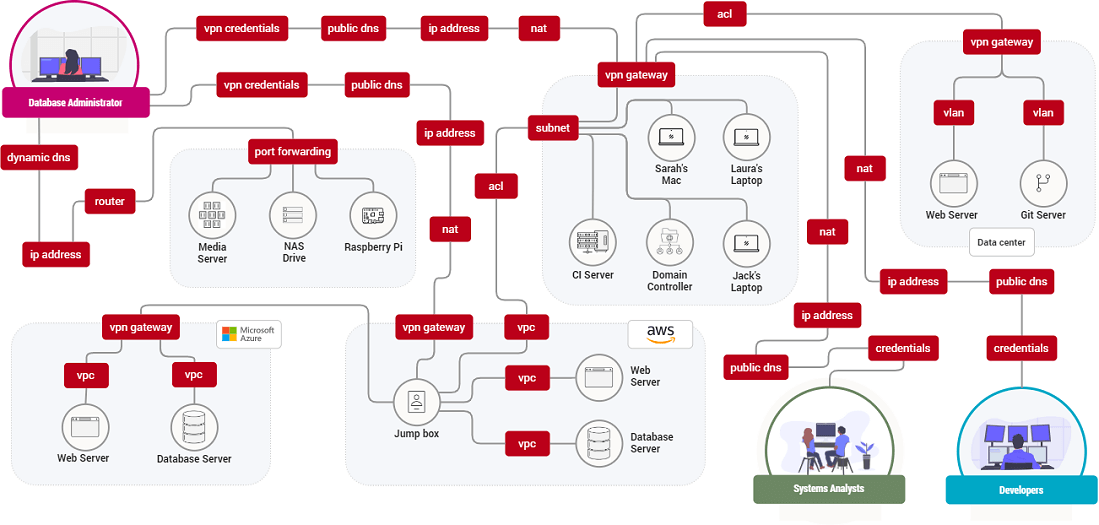
Apple’s approach is more vertically integrated. Because Apple designs the silicon (the A-series chips), the Secure Enclave and the GPU work in a tighter loop. The decryption keys never leave the hardware; they are processed in a way that the main CPU—and by extension, any app you might install—never actually “sees” the raw, decrypted bitstream.
| Feature | Apple FairPlay | Google Widevine (L1) | Open Source Alternatives |
|---|---|---|---|
| Hardware Root of Trust | Integrated (A-Series SoC) | TEE (TrustZone/Custom) | Software-based / Limited |
| Buffer Isolation | Kernel-level Secure Path | TEE-isolated Framebuffer | Application-level (Easily bypassed) |
| Enforcement | Strict OS-level API block | Hardware-dependent | Variable |
This creates a massive platform lock-in. Content providers trust Apple’s hardware more than they trust a fragmented ecosystem of Android OEMs, which is why certain 4K content is often restricted to specific “certified” devices.
“The transition from software-based DRM to hardware-backed secure paths represents a shift from ‘asking’ the OS to protect content to ‘forcing’ the silicon to hide it. At this level, the OS itself is often blind to the content it is displaying.” — Marcus Thorne, Senior Security Researcher at CyberSentinel.
Hardware-Level Isolation and the Secure Video Path
If you want to get truly granular, we need to look at the AVFoundation framework. When an app requests a stream, it doesn’t just download a file; it negotiates a handshake. The server sends an encrypted stream, and the device’s hardware decryption engine handles the heavy lifting.

The decoded frames are sent directly to the display controller. The “screenshot” function operates at a higher abstraction layer. It captures the composited image of the screen. By marking the video layer as isSecure, the compositor is told to omit that specific layer during any capture event. This is handled at the GPU driver level, making it invisible to the user and the app developer.
This is why you can sometimes take a screenshot of a “preview” image or a trailer, but not the actual feature film. The preview is a standard image file (no DRM), while the feature is a secure stream.
The Accessibility Paradox: When DRM Breaks the Web
While this is a win for copyright holders, it is a nightmare for accessibility. Screen readers and assistive technologies often rely on the ability to “see” or analyze what is on the screen to provide descriptions for visually impaired users. When a secure path is established, it can effectively blind these tools.
the “closed loop” nature of this technology fuels the ongoing tension between Apple and the open-source community. Efforts to create open-source media players that support high-res streaming are constantly thwarted by the requirement for proprietary hardware keys. You can write the most efficient playback code in the world, but if you don’t have the keys to the Secure Enclave, you’re stuck with 480p resolution.
We are seeing a slow shift toward more flexible standards, but as long as the “Chip Wars” continue and Apple maintains a vertical monopoly over its silicon, the black screen will remain the sentinel of the streaming era.
The Technical Takeaway
The black screen is not a failure of the iPhone; it is the system working exactly as intended. By moving the decryption and rendering into a hardware-isolated path, Apple removes the possibility of software-based interception. Until there is a fundamental shift in how the digital rights landscape is managed—perhaps through more transparent, blockchain-based licensing or EU-mandated interoperability—your screenshots of Netflix will remain a void of absolute black.

