Iran Escalates Cyber Warfare: Targeting Tech Giants Signals a New Era of Corporate Conflict
The Islamic Revolutionary Guard Corps (IRGC) has declared regional offices of US tech companies – including Apple, Google, Microsoft and Meta – as “legitimate targets,” escalating tensions beyond traditional military and energy infrastructure. This move, announced this week and slated to take effect April 1st, represents a significant expansion of Iran’s conflict strategy, directly implicating the corporate sector and raising serious cybersecurity concerns for global technology operations in the Middle East.
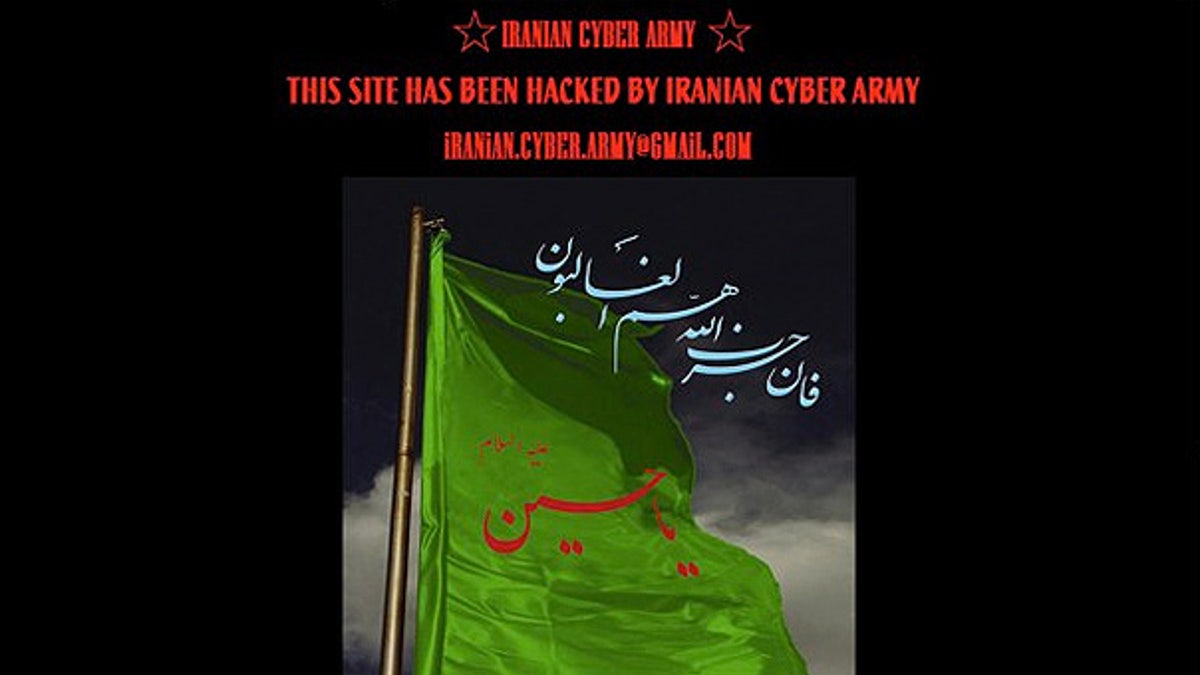
From Kinetic Strikes to Corporate Sabotage: A Paradigm Shift
This isn’t simply rhetoric. The IRGC’s previous actions, including reported attacks on Siemens, Telecom, and AT&T infrastructure in Israel, demonstrate a willingness to disrupt critical communication networks. These earlier attacks, while not directly targeting consumer-facing services, signaled a shift towards targeting the foundational layers supporting digital infrastructure. The current threat extends this to the companies *providing* those services, effectively turning tech headquarters into potential leverage points. The implication is clear: Iran views these companies as complicit in what it perceives as hostile actions against its interests. This represents a departure from previous strategies focused solely on state actors and military targets.
The timing is likewise crucial. With ongoing negotiations surrounding Iran’s nuclear program stalled and regional instability heightened, this escalation appears designed to increase pressure on the United States and its allies. It’s a calculated risk, designed to raise the stakes and force a reassessment of diplomatic strategies. The IRGC’s statement, disseminated through the semi-official Tasnim news agency, explicitly warned employees of these companies to evacuate their workplaces – a tactic designed to sow disruption, and fear.
The Technical Landscape: What’s at Risk?
The vulnerability isn’t simply physical security. These companies rely on complex, interconnected supply chains and cloud infrastructure. A successful attack could manifest in numerous ways, ranging from distributed denial-of-service (DDoS) attacks disrupting services to more sophisticated intrusions targeting sensitive data. Consider Google Cloud Platform (GCP) and Amazon Web Services (AWS), both heavily utilized in the region. A compromised server or network segment could have cascading effects, impacting not only the tech giants themselves but also the countless businesses and governments that rely on their services. The threat extends beyond data breaches; it encompasses the potential for manipulation of critical systems and the disruption of essential services.
Apple’s reliance on a tightly controlled ecosystem, while lauded for security, also presents a single point of failure. A successful breach targeting Apple’s regional infrastructure could compromise the data of millions of users. Microsoft, with its extensive enterprise footprint, faces a similar risk. The potential for supply chain attacks – targeting third-party vendors and software components – is particularly concerning. This is where the concept of software bill of materials (SBOM) becomes critical. The National Telecommunications and Information Administration (NTIA) has been pushing for wider adoption of SBOMs to improve software supply chain security, but implementation remains uneven.
Expert Insight: The Cybersecurity Implications
“This isn’t about stealing intellectual property; it’s about demonstrating capability and creating chaos. Iran has a sophisticated cyber warfare program, and they’re willing to employ it. The targeting of corporate entities is a clear escalation, and we should expect to see more of this type of activity.”
– Dr. Emily Harding, Senior Fellow, Center for Strategic and International Studies (CSIS)
The threat also highlights the increasing importance of zero-trust architecture. Traditional perimeter-based security models are insufficient in today’s threat landscape. Zero trust, which assumes that no user or device is inherently trustworthy, requires continuous verification and granular access control. This is particularly relevant for companies operating in high-risk regions like the Middle East. Robust incident response plans and regular security audits are essential to mitigate the risk of successful attacks.
The Open-Source Angle: A Potential Backdoor?
While the immediate threat focuses on proprietary systems, the widespread use of open-source software introduces another layer of complexity. Many of these tech giants rely heavily on open-source components, which are often subject to vulnerabilities. A compromised open-source library could provide a backdoor into critical systems. The recent Xz Utils vulnerability (CVE-2023-22515) serves as a stark reminder of the risks associated with relying on untrusted open-source code. This incident demonstrated how a malicious actor could compromise a widely used compression library, potentially impacting millions of systems. Companies must prioritize supply chain security and rigorously vet all open-source components.
The Chip Wars Connection: A Broader Geopolitical Context
This escalation isn’t happening in a vacuum. It’s inextricably linked to the broader geopolitical competition between the United States and China, often referred to as the “chip wars.” Iran’s reliance on Chinese technology, particularly in the telecommunications sector, adds another layer of complexity. While the US has imposed sanctions on Iran, China continues to maintain economic ties, providing access to critical technologies. This dynamic creates opportunities for Iran to circumvent sanctions and develop its cyber capabilities. The US government is actively working to restrict China’s access to advanced semiconductor technology, but these efforts are facing significant challenges.
The implications for the semiconductor industry are profound. Companies like TSMC, Intel, and Samsung are caught in the middle of this geopolitical struggle. They must navigate a complex web of regulations and sanctions while continuing to innovate and maintain their competitive edge. The recent CHIPS and Science Act, passed by the US Congress, aims to bolster domestic semiconductor manufacturing, but it will take years to fully realize its benefits.
What Which means for Enterprise IT
For organizations with operations in the Middle East, the immediate priority is to review and strengthen their cybersecurity posture. This includes:
- Implementing multi-factor authentication (MFA) for all critical systems.
- Conducting regular vulnerability assessments and penetration testing.
- Developing and testing incident response plans.
- Enhancing employee training on cybersecurity awareness.
- Monitoring threat intelligence feeds for emerging threats.
The 30-Second Verdict
Iran’s threat to US tech companies is a serious escalation of cyber warfare, signaling a new era of corporate conflict. The risk extends beyond data breaches to include disruption of critical services and potential manipulation of systems. Organizations operating in the Middle East must prioritize cybersecurity and prepare for a heightened threat environment.
“The IRGC is signaling that it views the private sector as a legitimate extension of US foreign policy. This is a dangerous precedent, and it will likely lead to more attacks on corporate targets in the future.”
– James Lewis, Senior Vice President, Center for Strategic and International Studies (CSIS)
The situation remains fluid and unpredictable. Continued monitoring of the geopolitical landscape and proactive cybersecurity measures are essential to mitigate the risks and protect critical infrastructure.

