“`html
KrebsOnSecurity Targeted by Near-Record DDoS Attack: Aisuru Botnet Suspected
Table of Contents
- 1. KrebsOnSecurity Targeted by Near-Record DDoS Attack: Aisuru Botnet Suspected
- 2. The Scale of the Attack
- 3. Aisuru’s Fingerprints
- 4. The Aisuru Botnet: How It Works
- 5. “Forky” and DDoS-for-Hire Services
- 6. Unmasking Forky
- 7. Considering the Mirai botnet attack on KrebsOnSecurity,what are some of the key vulnerabilities in IoT devices that make them susceptible to DDoS attacks?
- 8. KrebsOnSecurity Hit with Record DDoS Attack: A Deep Dive into Internet Security Challenges
- 9. The Scale and Scope of the Attack
- 10. Attack Characteristics and Key Metrics
- 11. The Mirai Botnet: Weapon of Choice
- 12. How Mirai Worked
- 13. Impact and Consequences of the Attack
- 14. DDoS Mitigation Strategies and Lessons Learned
- 15. DDoS Mitigation Techniques
- 16. Benefits of Proactive DDoS Protection
- 17. The Ever-Evolving Threat Landscape: Future Predictions
- 18. Real-World Exmaple: DDoS’s Long-Term Impact
- 19. Practical Tips for Website Owners
A Massive Distributed Denial-Of-Service (DDoS) attack recently hammered KrebsOnSecurity, reaching a staggering 6.3 terabits per second (Tbps). this near-record assault appears to be a trial run, showcasing the capabilities of a new, formidable internet of Things (IoT) botnet known as Aisuru. The brief but intense attack highlights the growing threat posed by these digital siege machines.
The Scale of the Attack
The 6.3 Tbps attack dwarfed the 2016 Mirai botnet attack, exceeding it by tenfold. Back then, Akamai, providing pro-bono DDoS protection, had to request KrebsOnSecurity to leave their service due to the disruption caused to paying customers.
Currently, Google’s Project Shield, a free DDoS defense service for news, human rights, and election-related websites, protects KrebsOnSecurity. Google Security Engineer Damian Menscher noted that the May 12 attack was the largest Google had ever handled, second only to a similar attack mitigated by Cloudflare earlier this year.
Aisuru’s Fingerprints
Comparing data with Cloudflare, Menscher identified the Aisuru botnet as the culprit behind both attacks. Aisuru, a digital siege machine that emerged less than a year ago, unleashed approximately 585 million data packets per second, targeting random ports with large UDP data packets.
“For most companies, this size of attack woudl kill them,” Menscher stated, emphasizing the potential to overwhelm network infrastructure.
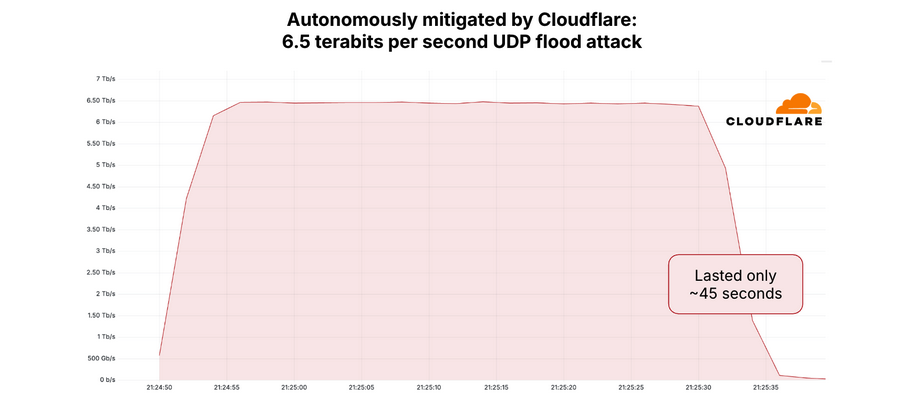
A graph depicting the 6.5 Tbps attack mitigated by Cloudflare in April 2025. Image: Cloudflare.
The Aisuru Botnet: How It Works
The aisuru botnet consists of compromised IoT devices globally, including routers and digital video recorders. These devices are hijacked through default passwords or software vulnerabilities. QiAnXin XLab researchers first identified Aisuru in August 2024, during an attack on a large gaming platform.
After a period of silence,Aisuru resurfaced in November with increased firepower and software exploits. A January 2025 report from XLab revealed that Aisuru (also known as “Airashi”) incorporated a previously unknown zero-day vulnerability in Cambium Networks cnPilot routers.
“Forky” and DDoS-for-Hire Services
The individuals behind the Aisuru botnet have been advertising access to their DDoS capabilities in public Telegram channels, closely monitored by security firms. In August 2024, subscriptions ranged from $150 per day to $600 per week, offering attacks of up to two terabits per second.
A notice posted on Telegram by the Aisuru botnet owners in August 2024 stated, “You may not attack any measurement walls, healthcare facilities, schools, or government sites.” Interested parties were directed to contact the Telegram handle “@yfork,” previously known as “Forky,” who has been active in DDoS-focused telegram channels since 2021.
The FBI has previously seized Forky’s DDoS-for-hire domains. In 2022, stresses[.]best was seized as part of an international law enforcement effort.
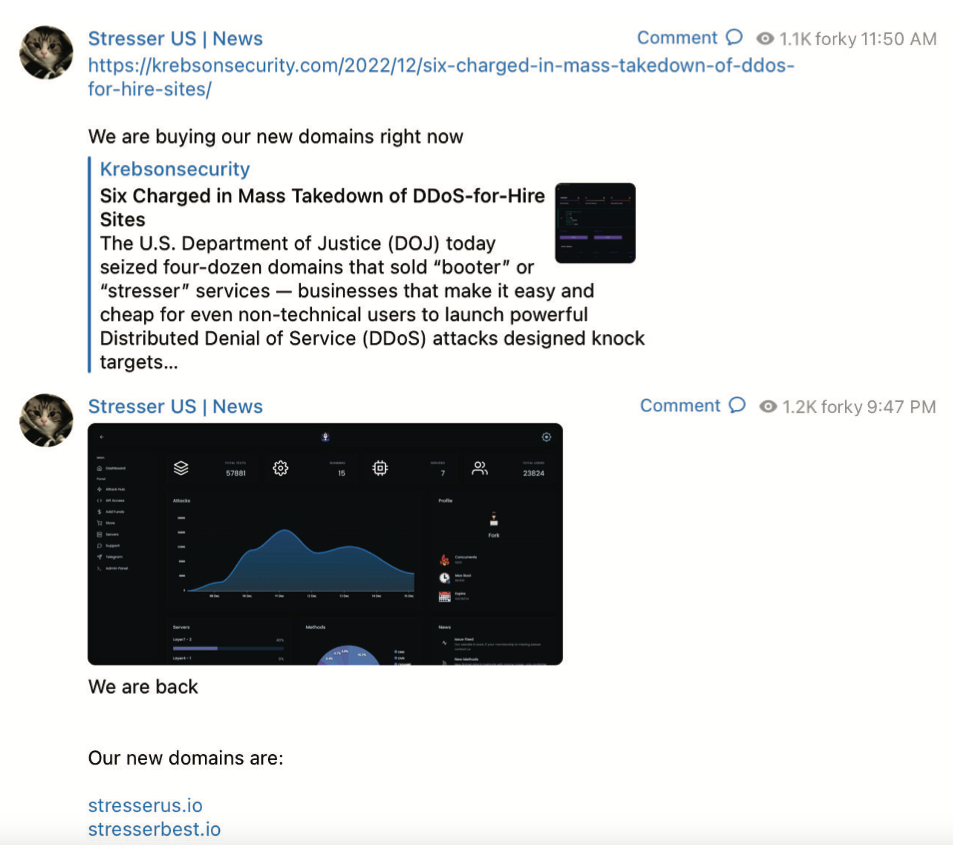
A screenshot from the FBI’s seizure warrant for Forky’s DDoS-for-hire domains shows Forky announcing the resurrection of their service at new domains.
Following the seizure announcement, Forky posted a link to a news story about the operation, adding, “We are buying our new domains right now.” Approximately ten hours later, Forky instructed customers to use their old passwords on the new website.
Unmasking Forky
Intelligence firms Unit 221B and Flashpoint have indexed Forky’s posts to public Telegram channels, revealing a 21-year-old individual claiming to reside in Brazil.
Since late 2022, Forky has frequently promoted Botshield[.]io, a DDoS mitigation company and ISP. Botshield LTD,a business entity registered in the United Kingdom,lists a 21-year-old woman from Sao Paulo,Brazil,as the director.
Considering the Mirai botnet attack on KrebsOnSecurity,what are some of the key vulnerabilities in IoT devices that make them susceptible to DDoS attacks?
KrebsOnSecurity Hit with Record DDoS Attack: A Deep Dive into Internet Security Challenges
The Scale and Scope of the Attack
Brian Krebs,the renowned cybersecurity investigative journalist behind KrebsOnSecurity, experienced a devastating Distributed Denial of Service (DDoS) attack in 2016. This attack, unprecedented at the time, brought the KrebsOnSecurity website offline and highlighted the evolving threat landscape facing online publications and businesses globally. The attackers leveraged a massive botnet called Mirai,composed of compromised Internet of Things (IoT) devices,to generate a flood of malicious traffic aimed at overwhelming the website’s servers. This event serves as a crucial case study in understanding modern DDoS threats and the strategies for website protection.
Attack Characteristics and Key Metrics
The DDoS attack on krebsonsecurity was notable for its sheer volume. It involved traffic exceeding 620 Gigabits per second (Gbps) at its peak. This tremendous bandwidth capacity meant the attackers could quickly exhaust the website’s resources, flooding the servers and preventing legitimate users from accessing the site. Analysis of the attack data reveals critical facts, including:
- Attack Type: primarily comprised of UDP flood attacks.
- Attack Duration: Extended over several days, indicating persistence and dedication from the attackers.
- Attacker’s Motivation: Primarily motivated by targeting Brian Krebs’s investigations, revealing an attack tailored to silence an investigative journalist.
The unprecedented attack demonstrated the vulnerability of even well-defended websites against coordinated assault using botnets. Understanding the attack’s profile is fundamental to formulating effective defense strategies.
The Mirai Botnet: Weapon of Choice
The attack’s success hinged on the Mirai botnet. Mirai exploited vulnerabilities within IoT devices like routers, cameras, and digital video recorders. Thes typically lacked robust security defenses, and default credentials were reused. Once compromised, these devices silently joined the botnet, becoming weapons for attackers, forming a “zombie army.” This makes Mirai a crucial point in the history of DDoS attacks.
How Mirai Worked
The Mirai botnet infected IoT devices by scanning the internet for devices with default usernames and passwords. Once identified, the malware woudl attempt to remotely take control, making them “bots.” These bots were then harnessed to launch DDoS attacks. Key aspects of Mirai’s operation include:
- Exploitation of Weak Defaults: Mirai preyed on weak default credentials such as “admin” and associated standard passwords,typical of many widely-available IoT devices.
- Large-Scale Compromise: Mirai could quickly create a large botnet of compromised devices to amplify the effect of DDoS attacks.
- Difficult Mitigation: The sheer number and distributed nature of the infected devices made it challenging to shut down the botnet’s operations quickly.
Impact and Consequences of the Attack
The attack on KrebsOnSecurity crippled the website and highlighted serious implications for free speech and online security. Besides bringing down the site, the attack’s consequences had far-reaching effects:
- Damage to Reputation: The inability to access the KrebsOnSecurity site, famous for breaking news on cybercrime, impacted its reputation and ability to deliver timely insights.
- Loss of Business: Organizations reliant on internet connectivity experienced significant financial losses, impacting revenue generation and public relations.
- Raising public consciousness: Alerting individuals to the risks of IoT vulnerabilities. This further fueled public advocacy.
The incident compelled a global assessment of website security and internet infrastructure, making the online surroundings more resilient to cyber attacks.
DDoS Mitigation Strategies and Lessons Learned
The attack on KrebsOnSecurity propelled crucial advancements in DDoS mitigation. Addressing the DDoS threat requires a multi-layered approach:
DDoS Mitigation Techniques
Mitigation strategies commonly include:
- Traffic Scrubbing: Specialized services which are essential for cleaning malicious traffic before it reaches a website’s primary infrastructure. This is conducted through dedicated DDoS mitigation providers like Cloudflare or Akamai.
- Rate Limiting: Limiting the amount of traffic that a single IP address can send over a given period to minimize the effects of attacks that rely on sustained traffic.
- Content Delivery Networks (CDNs): CDNs distribute content across multiple servers worldwide, which increases availability and also helps with DDoS mitigation by distributing traffic across geographically diverse locations.
- Web Application Firewalls (WAFs): WAFs proactively check HTTP traffic for malicious patterns that can then filter out malicious requests based on various rules.
these tactics work to keep the website online or render it as accessible as possible and are used in most modern ddos mitigation strategies. As such, it’s crucial for website administrators and organizations to continuously evaluate their defenses and incorporate the most recent security practices to be effectively shielded against emerging threats. The experience of KrebsOnSecurity is a crucial case study.
Benefits of Proactive DDoS Protection
- Improved Website Availability: Ensures that the website remains accessible to legit users, even during a DDoS attack.
- Enhanced user Experience: Guards page loading speeds and keeps it consistent, no matter the attack attempts.
- Improved Business Continuity: Helps the business to avoid extended downtimes, especially those that depend on web traffic such as e-commerce.
- Stronger Reputation: Showing proactive steps toward protecting your website gives visitors confidence and trust.
The Ever-Evolving Threat Landscape: Future Predictions
The attack on KrebsOnSecurity foreshadowed escalating cyber threats. DDoS attacks are continuously evolving, with attackers constantly refining their techniques. The sophistication and scale of future DDoS attacks are expected to rise. Predictions indicate:
- IoT Vulnerabilities: Because of continued security holes, attackers will continue exploiting IoT devices.
- Rise in Attacks: The number of DDoS attacks will still continue to go up,especially as botnets come more accessible.
- Elegant Attacks: More complex attack vectors are expected, combining application-layer and volumetric attacks.
Investing in robust and scalable security infrastructure and staying updated on the latest security practices and tactics will be vital for any business or institution going forward.
Real-World Exmaple: DDoS’s Long-Term Impact
The aftermath of the KrebsOnSecurity attack, included a lasting imprint on the security mindset of internet users and security professionals. This case led to increased adoption of DDoS mitigation solutions and fostered further research into mitigating strategies. Here are some observed changes:
- Increased Investment in DDoS Prevention: Post-attack there was a sharp expansion of spending on DDoS protection measures by businesses and individuals wishing to secure their online resources. DDoS mitigation providers gained in importance, increasing the adoption of cutting-edge technology.
- The Growth of Security Awareness: The incident increased public understanding of the scope and potential of cyberattacks, leading to a heightened consciousness of security risks and greater prioritization of cybersecurity practices.
- Changes in Internet Policy: The case influenced the progress of legislation and policies directed at improving the security of IoT devices and internet infrastructure, promoting a safer internet.
Practical Tips for Website Owners
Protecting a website from DDoS attacks requires a robust strategy. Here are actionable steps:
- Choose a Reputable CDN: Employing a Content Delivery Network (CDN) is critical to distributing your website’s data across regions, minimizing latency, and protecting you from attack.
- Implement a Web Application Firewall (WAF): Implement a Web Application Firewall to filter threats by inspecting HTTP/HTTPS traffic for malicious patterns.
- Monitor Traffic Constantly: Regular monitoring, using tools, can help recognize anomalies, providing early warnings of impending attacks.
- Regularly Review and Update Security: Update your website’s software and security measures regularly. This helps prevent attacks such as the one suffered by krebsonsecurity.
By implementing these strategies, businesses can improve resilience against DDoS attacks and maintain a strong online presence.
