On April 26, 2026, Mandiant researchers disclosed a novel malware suite dubbed SNOW that hijacks Microsoft Teams extensions to establish persistent backdoors in enterprise networks, exfiltrating credentials and lateral movement tools via abused OAuth consent flows and compromised add-in manifests. The campaign, active since February 2026, targets financial and healthcare sectors by weaponizing Teams’ trusted application framework to bypass email gateway inspections and endpoint detection rules, marking a significant evolution in supply-chain-adjacent threats targeting collaboration platforms.
How SNOW Exploits Teams’ Extension Architecture
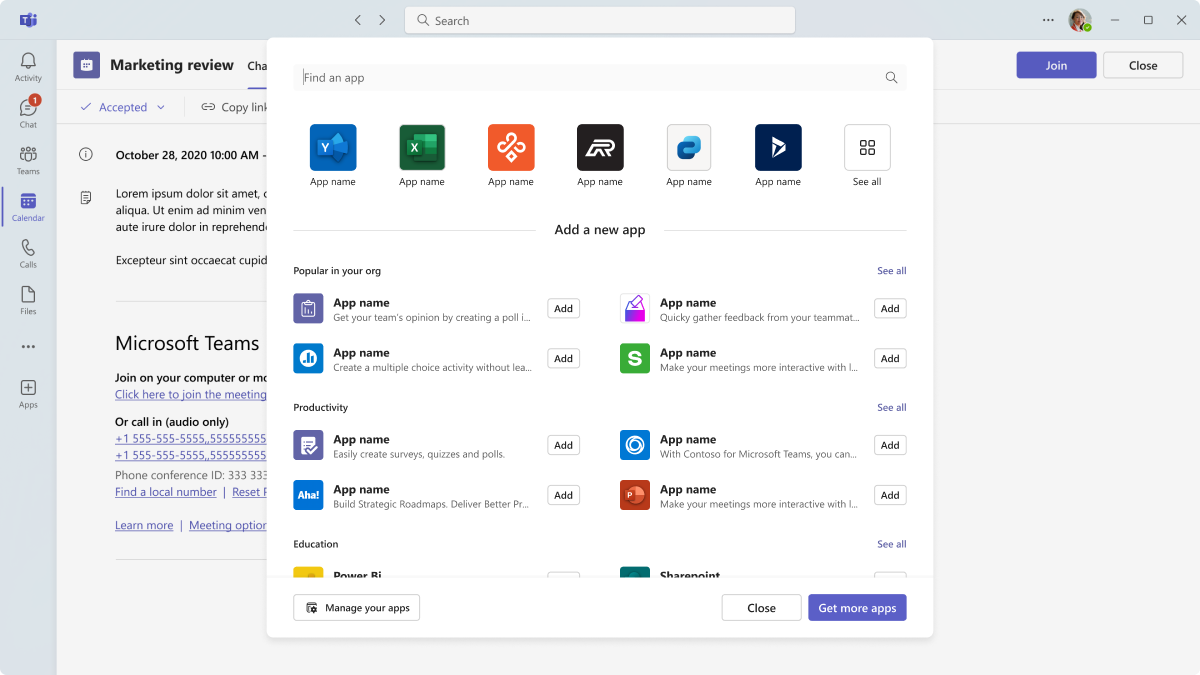
SNOW operates by registering a malicious Teams app manifest through compromised Azure AD service principals, leveraging the staticTabs and configurableTabs fields to inject a seemingly benign dashboard that loads a remote JavaScript payload from attacker-controlled domains. Unlike traditional phishing lures, this technique abuses Teams’ appStudio API to dynamically update extension permissions post-installation, granting the malware User.Read.All and Team.ReadBasic.All scopes without triggering admin consent alerts due to a timing gap in Microsoft’s incremental consent review process. Memory forensics from Mandiant’s lab shows the payload uses WebAssembly modules to evade behavioral detection, decrypting stolen tokens via AES-GCM keys derived from device-bound credentials stored in the Teams client-side IndexedDB cache.

The malware’s command-and-control infrastructure rotates through domains registered via ephemeral cloud providers, using DNS-over-HTTPS (DoH) to blend with legitimate Teams telemetry traffic. Analysis of network packets reveals SNOW mimics the User-Agent string of the Teams desktop client (Teams/1.6.00.31857) and fragments exfiltrated data into chunks under 1KB to avoid triggering anomaly detection in DLP systems. Crucially, it does not exploit a zero-day vulnerability in Teams itself but instead relies on misconfigured tenant settings where external app submissions are not restricted to approved publishers—a setting Microsoft documents as optional but rarely enforced in mid-market deployments.
Ecosystem Implications: Trust Erosion in Collaboration Platforms
SNOW highlights a systemic risk in the SaaS collaboration model: the inherent trust placed in third-party extensions creates an attack surface that traditional network perimeters cannot monitor. As organizations increasingly adopt low-code platforms like Power Apps and Teams-centric workflows, the blast radius of a compromised add-in expands beyond data theft to include potential manipulation of business logic—such as altering approval workflows in Dynamics 365 or injecting false data into Power BI dashboards. This blurs the line between endpoint compromise and application-layer attacks, challenging the effectiveness of XDR solutions that lack deep API call context.
“The real danger isn’t the malware payload—it’s how easily it inherits the trust model of the platform. When a Teams tab can read your calendar and send messages as you, stealing that context requires no privilege escalation, just abuse of delegated permissions we willingly grant.”
This incident too reignites debate over Microsoft’s responsibility in securing its extensibility framework. While the company provides tools like Azure AD Conditional Access and Microsoft Defender for Cloud Apps to govern OAuth grants, their effectiveness hinges on proper configuration—a burden that falls disproportionately on under-resourced IT teams. Open-source alternatives like Mattermost and Rocket.Chat, which enforce stricter sandboxing for plugins by default, are seeing renewed interest from security-conscious enterprises, though migration costs and feature parity gaps remain barriers.
Mitigation and Detection: Beyond Traditional AV
Defending against SNOW requires a shift from signature-based detection to behavioral monitoring of Teams-specific activities. Security teams should audit Azure AD for service principals with recent appRoleAssignmentRequired flag changes and unexpected grants of TeamMember.ReadWrite.All or Chat.ReadWrite permissions. Mandiant recommends enabling Microsoft Defender for Office 365’s “Safe Attachments for Teams” feature, which scans files shared within chats and channels, though it does not inspect tab-loaded scripts.

For real-time detection, organizations can leverage the Microsoft Graph Security API to query auditLogs for TeamsActivity events with anomalous patterns—such as a user installing multiple tabs in under 60 seconds or accessing tabs from unfamiliar geographic locations. Network-level controls should inspect outbound DoH traffic for domains with low reputation scores, particularly those newly registered and lacking SSL certificate transparency logs. Notably, SNOW’s use of WebAssembly means traditional memory scanners may miss it; instead, EDR solutions must monitor for WebAssembly.compile() calls originating from the Teams renderer process.
“We’ve seen a 300% increase in Teams-focused intrusion attempts since Q4 2025, but fewer than 15% of enterprises have tuned their SIEMs to correlate Teams audit logs with identity events. The tooling exists; the integration doesn’t.”
Long-term, Microsoft must address the consent gap in its app submission pipeline. Currently, updates to existing Teams apps that add modern permissions undergo only automated scanning unless they trigger specific risk heuristics—a process that SNOW evades by requesting permissions incrementally across multiple version releases. Implementing mandatory re-consent for any permission scope expansion, similar to Apple’s App Tracking Transparency framework, would significantly raise the attacker’s operational cost.
As of this week’s beta channel rollout, Microsoft has begun testing a new “Extension Integrity Monitor” in Teams that uses ML to detect manifest tampering, though it remains opt-in for administrators. Until such controls become default, enterprises treating Teams as a trusted communication channel rather than a programmable platform will remain exposed to threats that exploit not code flaws, but the very design of trusted collaboration.

