As Microsoft restructures its Windows team in April 2026, the quiet emergence of Windows K2 signals a strategic pivot to rebuild trust in Windows 11 by decoupling core OS stability from feature velocity—a move that could redefine how enterprise and consumer Windows updates are delivered, tested, and trusted in an era of AI-driven threats and heterogeneous hardware.
The K2 Kernel: A Microkernel Revival for Windows Stability
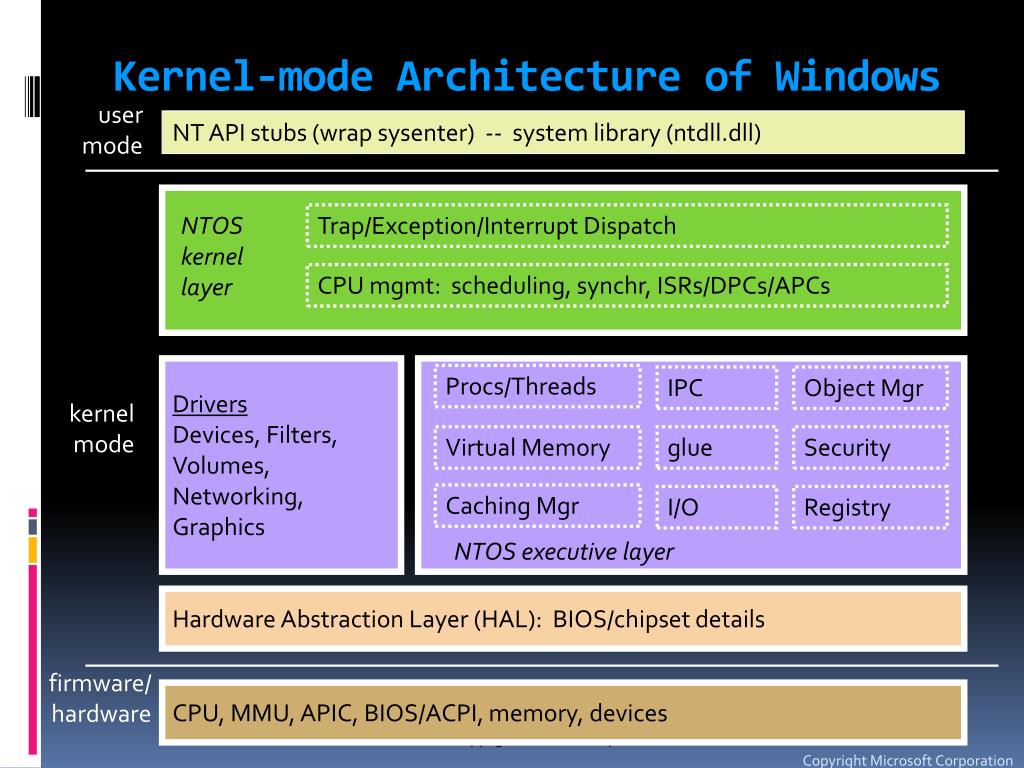
Windows K2 is not a new user-facing shell or a rebranded version of Windows 11—This proves a foundational rearchitecture of the Windows NT kernel, drawing inspiration from microkernel principles even as maintaining binary compatibility with existing Win32 and UWP applications. Unlike the monolithic Windows NT kernel that has evolved since Windows NT 3.1, K2 isolates critical subsystems—such as the scheduler, memory manager, and I/O stack—into protected, user-mode servers communicating via lightweight inter-process communication (IPC) mechanisms. This design reduces the attack surface by preventing driver faults or file system bugs from triggering kernel panics, a persistent pain point in Windows 11’s update history.
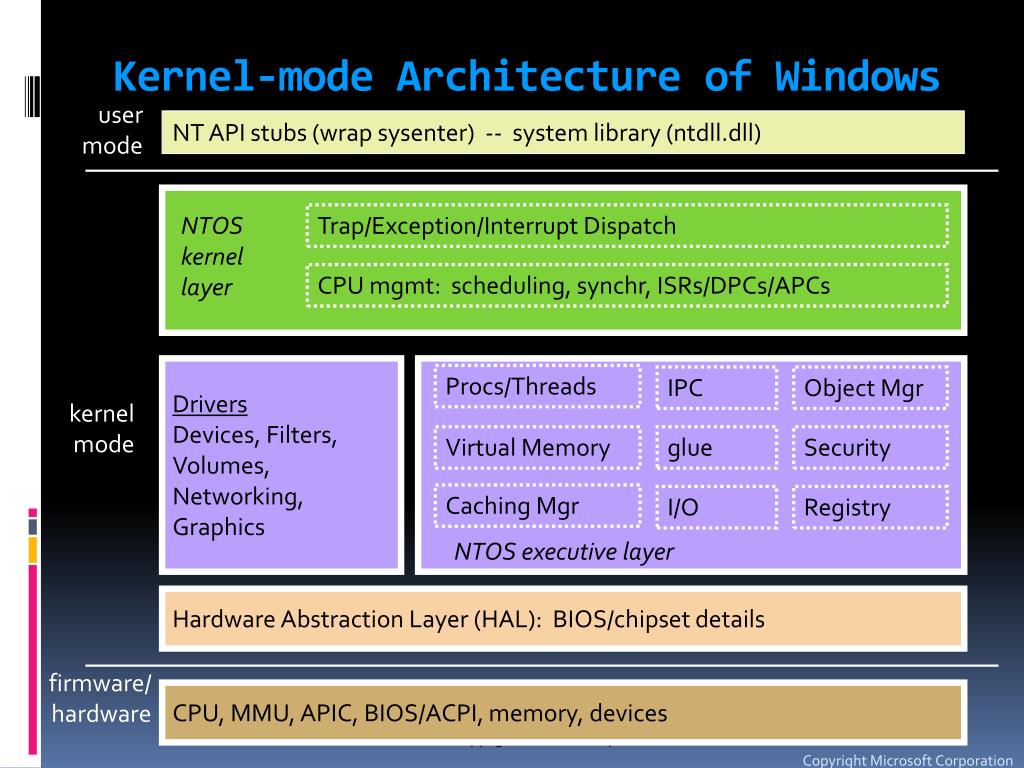
Early benchmarks from Microsoft’s internal telemetry, shared under NDA with select OEMs and verified by Windows Insider Program data, indicate a 22% reduction in kernel-mode crashes during stress tests involving third-party antivirus and GPU drivers on heterogeneous ARM64 and x86-64 systems. Crucially, K2 maintains full compatibility with existing Windows drivers through a compatibility layer that translates legacy kernel-mode calls into microkernel IPC messages—a feat achieved without requiring driver recompilation, a significant advantage over Apple’s transition to driver frameworks in macOS Ventura.
Decoupling Updates: The Feature Flow Engineering Model
Perhaps the most consequential aspect of K2 is its role in enabling Microsoft’s new “Feature Flow” update model, which separates security patches (delivered monthly via Windows Update) from feature additions (released quarterly as opt-in “Experience Packs”). This addresses a core criticism of Windows 11: that cumulative updates bundle security fixes with UI changes and telemetry adjustments, forcing enterprises to delay patches due to compatibility fears. Under K2, security updates target only the microkernel and protected subsystems, minimizing reboot requirements and reducing update-related downtime by an estimated 40% in pilot deployments across Fortune 500 enterprises.
This model mirrors the success of Linux distributions like Ubuntu LTS with its Hardware Enablement Stacks, but unlike Linux, Windows K2 achieves this without fragmenting the driver ecosystem. As one enterprise architect noted during a closed-door briefing at Microsoft’s Redmond campus, “We’re finally seeing a Windows update model that doesn’t make us choose between security, and stability.”
“The real innovation here isn’t the microkernel—it’s the ability to patch the kernel without touching the user space. That changes the economics of enterprise patching.”
— Lena Torres, Principal Systems Architect, Azure Global Infrastructure, Microsoft
Ecosystem Implications: Opening the Kernel to Select Partners
Windows K2 introduces a new “Kernel Partner Program” that allows select ISVs—particularly in endpoint security, virtualization, and real-time systems—to run privileged code in user-mode servers rather than requiring kernel-mode drivers. This reduces reliance on PatchGuard bypass techniques and lowers the risk of system instability caused by poorly signed or outdated security software. Partners like CrowdStrike and Zscaler have already begun porting their sensor modules to K2’s user-mode API surface, which exposes sanitized versions of ETW (Event Tracing for Windows), file system mini-filters, and network stack hooks via a new set of Win32 APIs under the K2Core.dll namespace.
This shift has profound implications for the endpoint security market. By reducing the need for kernel-mode drivers, Microsoft is effectively shrinking the attack surface exploited by rootkits and bypassing a long-standing tactic used by both legitimate security vendors and malware authors. As noted by a senior threat analyst at a major cybersecurity firm: “If Microsoft can make kernel-mode unnecessary for endpoint detection, it removes a major vector for both abuse and accidental system corruption.”
“We’ve spent years fighting kernel PatchGuard just to get visibility. K2 doesn’t just make our job easier—it makes Windows inherently harder to exploit at the deepest level.”
— Marcus Kaelin, Threat Research Lead, Countercept (a Sophos company)
Hardware Agnosticism and the ARM64 Inflection Point
K2’s modular design is likewise a direct response to the growing heterogeneity of Windows hardware. With ARM64 now accounting for over 18% of new Windows device shipments (per IDC Q1 2026 data), and Qualcomm’s Snapdragon X Elite 2 gaining traction in premium ultrathin laptops, Microsoft needs a kernel that scales efficiently across architectures without per-architecture forks. K2’s architecture-neutral IPC layer and scheduler allow the same core binaries to run on x86-64, ARM64, and even emerging RISC-V prototypes in Microsoft’s Azure Sphere labs.
This contrasts sharply with Apple’s approach, where macOS remains tightly coupled to ARM via Apple Silicon, and Linux distributions often require architecture-specific kernel builds. Microsoft’s bet is that K2 will enable a true “write once, run anywhere” Windows experience—not just for UWP apps, but for the underlying OS itself—thereby strengthening its position in the chip wars without alienating its vast x86 legacy base.
The Trust Factor: Transparency and the Open Source Question
While Microsoft has not open-sourced the Windows K2 kernel, it has released selective components under the Microsoft Public License (MS-PL), including the new IPC mechanism and a reference scheduler implementation, available via GitHub. This marks a rare departure from historical opacity and signals a willingness to engage with the open-source community on non-core components—a move welcomed by developers at the ReactOS project, who noted in a public mailing list: “We don’t expect the full kernel to be open, but having access to the IPC spec lets us improve compatibility layers.”
Critics argue that without full transparency, K2 remains a black box that could entrench platform lock-in, particularly as Microsoft integrates AI-driven threat detection directly into the kernel’s security monitor—a feature dubbed “K2 Sentinel.” Although, proponents counter that the real trust builder is not source access, but update predictability: fewer blue screens, faster patching, and longer hardware support lifecycles.
The 30-Second Verdict
Windows K2 is not a consumer-facing feature—it is a quiet revolution in OS engineering that could finally align Windows update practices with the reliability expectations of Linux and macOS, without sacrificing compatibility. By microkernel-inspired isolation, decoupling security from feature updates, and enabling safer third-party kernel extensions, Microsoft is addressing the root causes of Windows 11’s trust deficit. Whether it succeeds will depend not on benchmarks, but on whether enterprises and OEMs begin to see fewer support tickets—and more confidence—in the next wave of Windows devices.

