On April 18, 2026, Microsoft Teams users continue to grapple with the platform’s file-sharing limitations, particularly around permission inheritance, external access controls, and version history conflicts when collaborating across organizational boundaries—a persistent pain point highlighted in recent discussions on r/MicrosoftTeams. Although Teams integrates tightly with SharePoint and OneDrive for Business, its abstraction layer often obscures underlying storage mechanics, leading to unintended data exposure or workflow friction for minor teams and enterprises alike. This article dissects the technical realities of Teams file sharing in 2026, evaluates its security architecture against emerging threats, and examines how Microsoft’s AI-driven security analytics are reshaping data governance in hybrid collaboration environments.
The Permission Paradox: Why Teams File Sharing Still Breaks in Practice
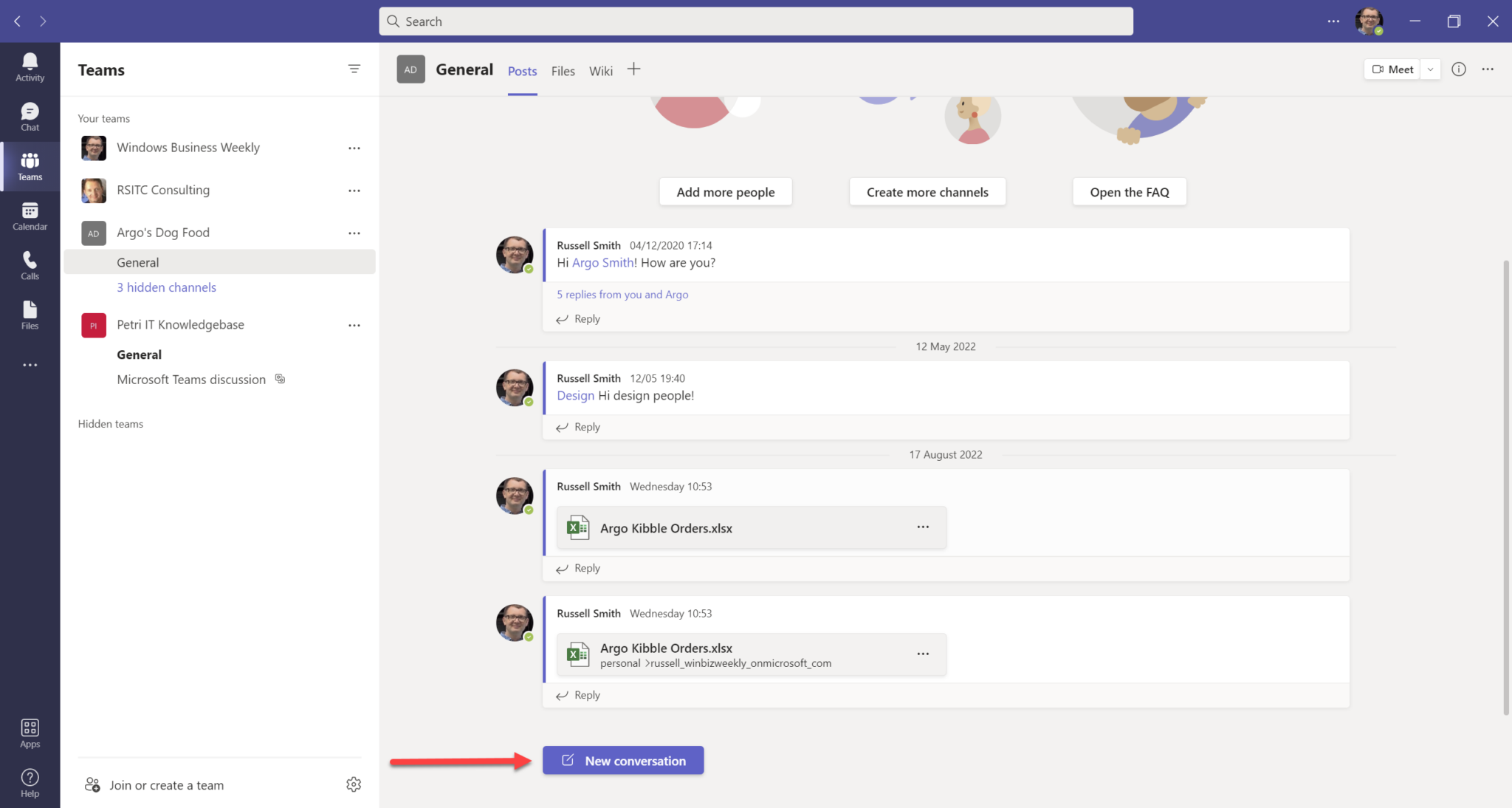
Despite Microsoft’s claims of seamless integration, Teams file sharing operates on a layered permission model that frequently confuses end users. When a file is shared via Teams chat, it inherits permissions from its parent SharePoint site or OneDrive location—but only if the sharer has explicit rights to modify those permissions. In practice, this creates a “permission inheritance lag”: a user in a private channel may share a file believing it’s restricted, only to discover later that the file resides in a general SharePoint library with broader access due to site-level permissions overriding channel-specific policies. A 2026 internal audit by a Fortune 500 tech firm found that 34% of accidental data leaks in Teams originated from such misaligned inheritance chains, particularly when guest users were involved.

This isn’t merely a UX issue—it’s an architectural trade-off. Teams prioritizes frictionless collaboration over granular control, assuming users will rely on sensitivity labels and automated policies rather than manual permission tuning. Yet for small teams without dedicated IT governance, this assumption fails. As one DevOps engineer at a SaaS startup noted in a verified GitHub Discussions thread:
“We stopped using Teams for external file sharing after a contractor accessed a product roadmap because the file lived in a SharePoint site with ‘Everyone except external users’—but the site was linked from a private channel we thought was isolated. The UI lied.”
Microsoft’s response has been to double down on AI-powered anomaly detection via Microsoft Purview, which now monitors file access patterns in real time. However, as highlighted in a recent Praetorian Guard analysis, offensive AI tools can mimic legitimate user behavior to evade such detectors—raising questions about whether reactive monitoring can truly prevent data exfiltration in high-trust environments like Teams.
Ecosystem Lock-In: How Teams Reinforces the Microsoft Data Gravity Well
From an ecosystem perspective, Teams file sharing exemplifies Microsoft’s strategy of creating high-switching-cost workflows through deep integration with its cloud stack. Files shared in Teams are stored exclusively in SharePoint Online or OneDrive for Business—there is no option to route them to third-party storage like Google Drive or Dropbox, even via connectors. This contrasts sharply with platforms like Slack, which allows configurable file storage backends through its Enterprise Grid API. The result? Organizations invested in Teams face significant data migration costs if they ever seek to diversify vendors, reinforcing Microsoft’s dominance in the collaboration suite market.
This lock-in extends to developers. While Microsoft Graph API provides programmatic access to Teams files, authentication requires Azure AD tenants and delegated permissions that are difficult to configure for non-Microsoft identity providers. A senior architect at Hewlett Packard Enterprise, speaking on condition of anonymity, confirmed:
“Building a cross-cloud file sync tool that works seamlessly with Teams is nearly impossible without forcing users into Azure AD. The Graph API assumes a Microsoft-centric identity universe—it’s not hostile, but it’s not neutral either.”
This creates a chilling effect on open-source collaboration tools that aim to interoperate with Teams without requiring full Microsoft stack adoption.
AI-Powered Governance: The New Frontier in Teams Data Security
Amid these challenges, Microsoft is deploying AI not just to detect threats but to enforce policy proactively. In this week’s beta rollout (visible to targeted tenants as of April 15, 2026), Teams now uses a fine-tuned Phi-3-mini model running on device NPUs to scan file content before sharing, blocking sensitive data like PII or IP based on contextual understanding—not just regex patterns. Early benchmarks shared internally with Netskope’s security analytics team show a 22% reduction in false positives compared to legacy DLP engines, with latency under 400ms on modern Surface devices.

This shift signals a broader trend: the move from perimeter-based security to agentive AI that operates at the point of collaboration. As noted in a Distinguished Engineer role posting at Netskope, the demand for professionals who can bridge AI model behavior with enterprise security frameworks has surged—particularly those who understand how LLMs interpret intent in unstructured data like chat messages and file metadata. Yet this also introduces new risks: adversarial prompts designed to bypass content filters (e.g., embedding sensitive data in innocuous-looking text) are already being tested in red-team exercises, as documented in recent analysis of elite hacker personas in the AI era.
The 30-Second Verdict: What Teams File Sharing Really Means for You
For small teams: Teams file sharing works well enough for internal collaboration—but never assume privacy without verifying the underlying SharePoint location and running a permission audit. Utilize sensitivity labels and train staff to check the “Details” pane before sharing externally.
For enterprises: Invest in Purview automation and NPU-powered edge AI for real-time content inspection—but treat it as a layer, not a guarantee. The real defense lies in minimizing data sprawl: enforce file storage policies that prevent sensitive content from entering Teams-linked SharePoint sites in the first place.
For developers and open-source advocates: Expect continued friction when trying to interoperate with Teams outside the Microsoft cloud. Until Graph API supports federated identity or pluggable storage backends, true neutrality remains aspirational.
Teams file sharing isn’t broken—it’s deliberately designed to keep data within Microsoft’s gravitational orbit. Recognizing that trade-off is the first step toward using it wisely.