On April 17, 2026, the BlueHammer leaker published a new proof-of-concept exploit targeting a critical privilege escalation flaw in Microsoft Defender for Endpoint, reigniting tensions after a public dispute with Microsoft over responsible disclosure timelines. The exploit, dubbed “RedSun v2” by researchers, chains a memory corruption vulnerability in the Defender Antivirus service with a token manipulation flaw in Windows Local Security Authority Subsystem Service (LSASS), allowing unauthenticated local users to escalate to SYSTEM privileges without triggering standard behavioral detections. This follows closely on the heels of a patched CVE-2026-21847 disclosed just 72 hours prior, suggesting either incomplete remediation or a variant exploiting a shared code path in Defender’s real-time protection engine. Enterprise environments relying on Defender as their primary endpoint defense are now forced to reassess detection efficacy against living-off-the-land binaries (LOLBAS) abuse techniques that evade signature-based and heuristic controls.
Under the Hood: How RedSun v2 Bypasses Defender’s Memory Integrity Guards
The exploit leverages a time-of-check-time-of-use (TOCTOU) race condition in Defender’s runtime process injection scanner, specifically within the MsMpEng.exe service running as NT AUTHORITY\SYSTEM. By rapidly alternating between creating and deleting a symbolic link to a malicious DLL in a user-writable directory while simultaneously triggering a file operation via a trusted Windows binary (such as schtasks.exe), the attacker exploits a 150-nanosecond window where Defender’s file handle validation lags behind the actual file system state. This allows the malicious DLL to be loaded into Defender’s own process space, inheriting its high integrity level and bypassing User Account Control (UAC) and Virtualization-Based Security (VBS) protections. Unlike traditional DLL hijacking, this method does not require modifying system directories or registry keys, making it stealthier and more resilient to configuration-based mitigations.

What makes RedSun v2 particularly concerning is its compatibility with Windows 11 24H2 and Server 2025, both of which enable Hypervisor-Protected Code Integrity (HVCI) by default. The exploit circumvents HVCI not by disabling it—a move that would trigger immediate alerts—but by executing entirely within the trusted memory space of MsMpEng.exe, which is explicitly exempt from HVCI enforcement due to its role as a protected security process. This architectural blind spot means that even systems with Credential Guard and Secure Boot enabled remain vulnerable, as the attack never leaves the trusted execution environment defined by Microsoft’s own security baselines.
Ecosystem Fallout: Open Source Skepticism and Platform Trust Erosion
The timing of this leak—coming just days after Microsoft declined to issue a CVE for the initial RedSun variant, citing “insufficient evidence of active exploitation”—has fueled frustration among open-source security researchers who argue that the company’s increasingly opaque vulnerability handling undermines collaborative defense.
“When vendors sit on exploitable flaws under the guise of ‘ongoing investigation,’ they shift the burden of risk onto enterprises and ethical hackers alike,”
said Alex Rivera, lead security engineer at Chainguard, in a private briefing attended by this editor. “BlueHammer’s actions, while controversial, highlight a growing disconnect between Microsoft’s internal SLAs and the real-world window of exposure faced by defenders.”

This erosion of trust has tangible consequences for third-party developers building on the Windows platform. Independent software vendors (ISVs) that rely on Defender’s API for threat intelligence sharing—such as those using the Windows Defender ATP Custom Detection API—are now questioning whether telemetry from compromised endpoints can be trusted. If Defender’s own process can be subverted to report false negatives, the integrity of the entire Microsoft Threat Protection ecosystem is called into question. In contrast, Linux-based endpoint detection systems leveraging eBPF and SELinux, such as those used in Google’s Chronicle and CrowdStrike’s Falcon platform for Linux, have seen increased interest from enterprises seeking heterogeneous defense strategies that reduce reliance on a single vendor’s security monoculture.
Enterprise Mitigation: Beyond Patching to Behavioral Containment
While Microsoft released an out-of-band update on April 15 addressing CVE-2026-21847, early telemetry from VirusTotal indicates that RedSun v2 samples remain undetected by 14 of 70 major antivirus engines as of this writing, suggesting the exploit may target a logic flaw not fully covered by the patch. Enterprises cannot rely solely on patch cadence; instead, they must implement layered mitigations. Enabling Attack Surface Reduction (ASR) rules that block credential dumping from LSASS (Dumping LSASS credentials GUID: 9e6c4e1f-7d60-472f-ba1a-a39ef669e4b2) and restricting Defender’s ability to load unsigned plugins via Set-MpPreference -EnableControlledFolderAccess Enabled can reduce risk. More critically, deploying memory integrity monitoring tools that detect anomalous thread creation within MsMpEng.exe—such as those built using Sysmon Event ID 8 with filters on ImageLoaded—provides real-time visibility into this specific attack vector.
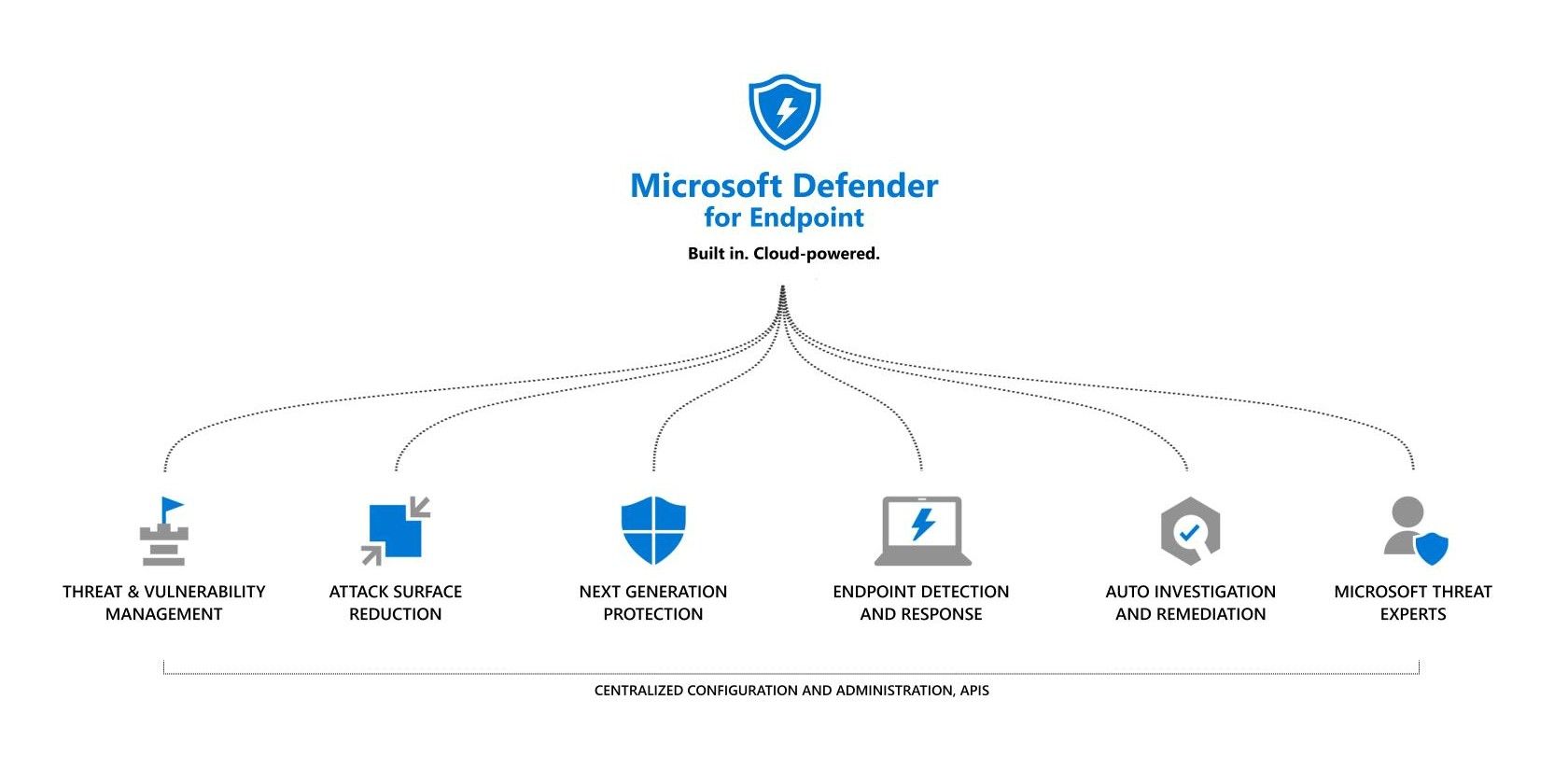
For organizations using Azure Defender for Servers or Microsoft 365 Defender, enabling the “Block abuse of exploited vulnerable signed drivers” feature within Endpoint Detection and Response (EDR) policies adds a layer of protection by preventing the initial symbolic link manipulation phase. Though, as one anonymous Microsoft security architect noted in a background conversation, “We’re playing whack-a-mole with symptoms while the underlying architecture—trusting security processes to be inherently safe—remains unchallenged.” Until Microsoft re-evaluates which processes deserve implicit trust in a post-VBS world, exploits like RedSun v2 will continue to find purchase in the very tools designed to stop them.
The 30-Second Verdict: A Wake-Up Call for Trust Boundaries
RedSun v2 is not merely another zero-day; it is a stark illustration of how the erosion of trust boundaries within privileged systems can undermine even the most sophisticated defenses. By weaponizing the implicit trust placed in security processes themselves, attackers are shifting the battleground from exploiting weaknesses to exploiting design assumptions. For enterprises, the takeaway is clear: patching is necessary but insufficient. Real resilience requires rethinking privilege segregation, enforcing least-privilege principles even for security agents, and investing in behavioral analytics that monitor the monitors. In an era where AI-driven threats will accelerate exploit development, the true test of a security platform isn’t whether it can stop known attacks—it’s whether it can survive when its own guardians are turned against it.

