The New York Times Mini Crossword for May 1, 2026, revealed answers centered around themes of digital communication and data – “EMAIL,” “CLOUD,” “BYTES,” “LINK,” and “SHARE.” While seemingly innocuous, these terms reflect the increasingly complex infrastructure underpinning modern life and more importantly, the escalating battle for control over that infrastructure. This isn’t just about word games; it’s a subtle indicator of how deeply ingrained these concepts are in our daily consciousness, and a reminder of the vulnerabilities inherent within them.
The Semantic Web’s Quiet Revolution: From Bytes to LLM Parameter Scaling
The answers themselves are foundational. “BYTES,” the fundamental unit of digital information, are the bedrock upon which everything else is built. But the scale has shifted dramatically. We’ve moved beyond simply storing bytes; we’re now grappling with petabytes and exabytes, fueling the exponential growth of Large Language Models (LLMs). The current state-of-the-art LLMs, like Google’s Gemini 1.5 Pro and Anthropic’s Claude 3 Opus, are pushing the boundaries of LLM parameter scaling – models now boast trillions of parameters, demanding unprecedented computational resources and sophisticated data management strategies. This isn’t just about bigger models; it’s about emergent capabilities. The ability to process and understand information at a human level, and even surpass it in certain domains, is directly tied to the sheer volume of data and the complexity of the underlying algorithms.
What This Means for Enterprise IT
For enterprises, this translates to a fundamental shift in how they approach data storage, processing, and security. Traditional relational databases are increasingly inadequate for handling the scale and complexity of modern data. The rise of NoSQL databases, like MongoDB and Cassandra, is a direct response to this challenge, offering greater scalability and flexibility. However, NoSQL databases also introduce new security concerns, as they often lack the robust ACID (Atomicity, Consistency, Isolation, Durability) properties of traditional databases. The move to the “CLOUD” – another answer from the crossword – is often presented as a solution, but it introduces a new layer of dependency and potential vulnerability.
The Cloud’s Paradox: Convenience vs. Control
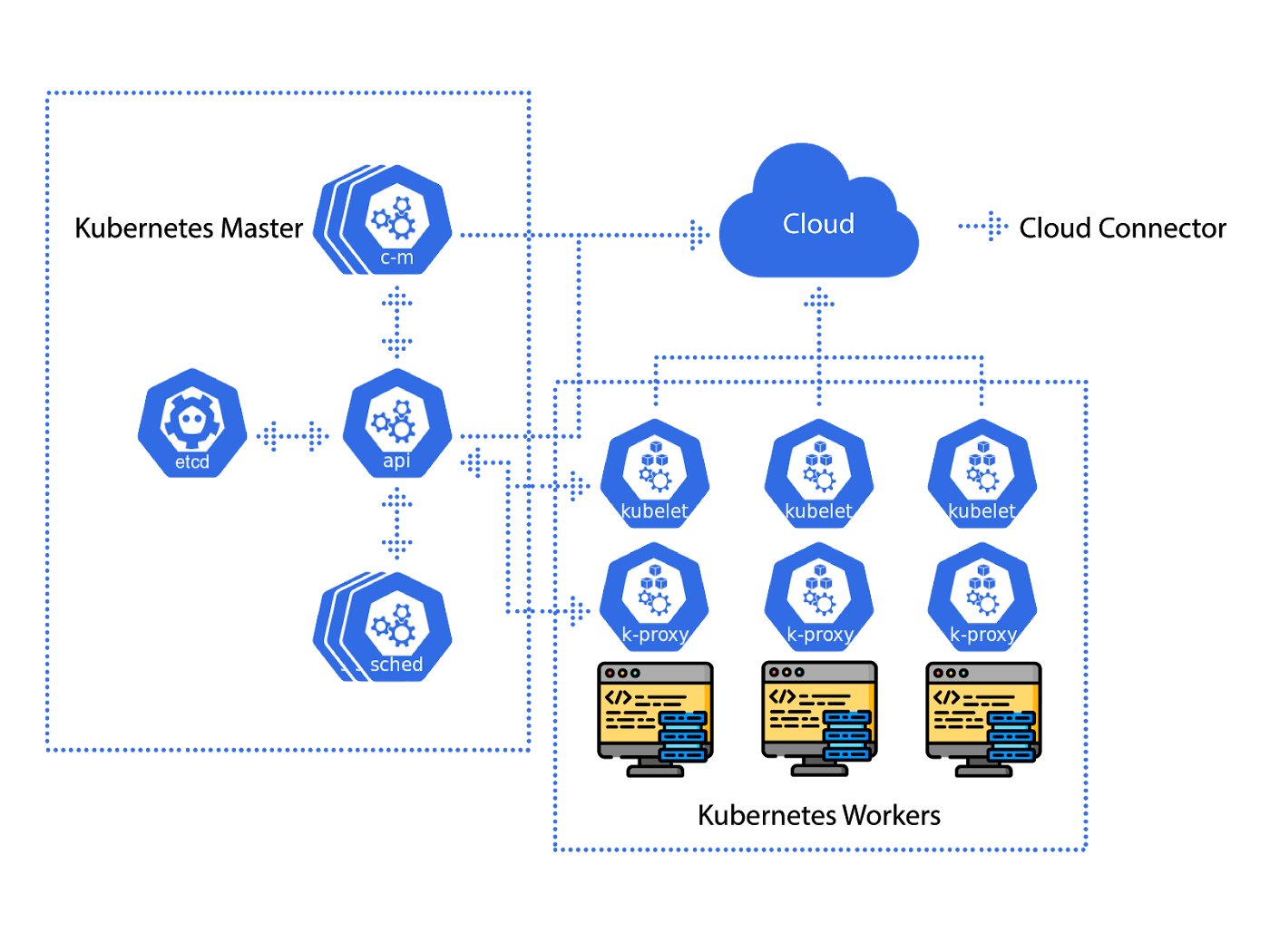
The allure of the cloud is undeniable: scalability, cost-effectiveness, and ease of management. But it also means relinquishing control over your data and infrastructure. The major cloud providers – Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP) – are essentially gatekeepers to the digital world. Their dominance raises concerns about vendor lock-in and the potential for censorship or data breaches. The recent surge in interest in federated cloud solutions, where organizations can distribute their data and applications across multiple cloud providers, is a direct response to these concerns. Projects like OpenStack and Kubernetes are gaining traction as organizations seek to regain control over their cloud infrastructure. Kubernetes, in particular, has become the de facto standard for container orchestration, enabling developers to deploy and manage applications across a variety of environments.
The concept of “LINK” – another crossword answer – highlights the interconnectedness of the modern web. But this interconnectedness also creates vulnerabilities. Supply chain attacks, where attackers compromise a third-party vendor to gain access to their customers, are becoming increasingly common. The SolarWinds hack in 2020 is a stark reminder of the devastating consequences of such attacks. Organizations need to adopt a zero-trust security model, where no user or device is trusted by default, and all access requests are verified.
The Rise of Post-Quantum Cryptography and End-to-End Encryption
The threat landscape is also evolving rapidly. The development of quantum computers poses a significant threat to current encryption algorithms. Shor’s algorithm, for example, can break RSA encryption, which is widely used to secure online transactions. The National Institute of Standards and Technology (NIST) is currently working to standardize post-quantum cryptography (PQC) algorithms that are resistant to attacks from both classical and quantum computers. NIST’s PQC Standardization Process is a critical step in preparing for the quantum era.
“EMAIL” and “SHARE,” the final answers, underscore the importance of secure communication. End-to-end encryption (E2EE) is essential for protecting the privacy of email and other communications. However, implementing E2EE is not without its challenges. It requires careful key management and can be difficult to integrate with existing systems. The Signal protocol, used by Signal, WhatsApp, and other messaging apps, is widely considered to be the gold standard for E2EE.
“The shift towards homomorphic encryption is a game-changer. It allows computation on encrypted data without decrypting it first, opening up possibilities for privacy-preserving machine learning and data analysis.” – Dr. Anya Sharma, CTO of CipherSafe Technologies.
The 30-Second Verdict
The NYT Mini Crossword isn’t just a pastime; it’s a cultural barometer. The answers on May 1, 2026, reflect a world grappling with the complexities of digital infrastructure, data security, and the evolving threat landscape. The key takeaway? Security is no longer an afterthought; it’s a fundamental requirement.
API Security and the Zero-Trust Imperative
The proliferation of APIs (Application Programming Interfaces) has further complicated the security landscape. APIs are the building blocks of modern applications, enabling different systems to communicate with each other. However, they also create new attack vectors. The OWASP API Security Top 10 lists the most critical API security risks, including broken authentication, excessive data exposure, and lack of resources and rate limiting. Implementing robust API security measures, such as authentication, authorization, and input validation, is essential for protecting sensitive data. The zero-trust model extends to APIs, requiring continuous verification of all API requests.

The increasing sophistication of cyberattacks demands a proactive approach to security. Organizations need to invest in threat intelligence, vulnerability management, and incident response capabilities. The leverage of AI and machine learning can help automate these processes and improve detection rates. However, AI-powered security tools are not a silver bullet. Attackers are also using AI to develop more sophisticated attacks. It’s an ongoing arms race.
The future of cybersecurity will be defined by the ability to adapt and innovate. The technologies and strategies that are effective today may not be effective tomorrow. Organizations need to embrace a culture of continuous learning and improvement. And they need to recognize that security is a shared responsibility.
| Encryption Standard | Security Level (as of 2026) | Quantum Resistance |
|---|---|---|
| AES-256 | High | No |
| RSA-4096 | Medium | No |
| Kyber-768 (PQC) | High | Yes |
| Dilithium-2 (PQC) | Medium | Yes |
The seemingly simple answers to a daily crossword puzzle offer a surprisingly insightful glimpse into the complex technological and security challenges of our time. Ignoring these signals is a risk we can no longer afford to take.

