In early 2026, a sophisticated wave of signal-phishing attacks targeting encrypted messaging platforms like Signal has exposed critical vulnerabilities in how users authenticate and trust communications, leveraging social engineering to bypass end-to-end encryption not by breaking crypto but by hijacking verified identities through compromised device registration or SIM-swapping, turning trusted contact lists into attack vectors that can read messages, initiate conversations and impersonate victims with alarming precision—prompting urgent calls for layered defenses beyond encryption alone as attackers increasingly exploit human factors rather than cryptographic flaws in what researchers now call “identity spoofing via trusted channel abuse.”
The Mechanics of Signal-Phishing: How Trust Is Weaponized
Unlike traditional phishing that lures users to fake login pages, signal-phishing in 2026 operates at the identity layer: attackers first compromise a victim’s phone number via SIM-swap or exploit flaws in carrier-side account recovery, then re-register the Signal client on a controlled device. Because Signal trusts the phone number as the primary identifier—and doesn’t require re-verification of existing contacts when a number is re-registered—attackers gain immediate access to message history (if backups are cloud-synced and inadequately protected) and can send messages appearing fully legitimate to the victim’s contacts. Crucially, the safety number verification feature, designed to detect man-in-the-middle attacks, is often ignored by users who assume familiarity equals safety. Recent telemetry from Signal’s abuse prevention team shows a 300% increase in reported identity spoofing attempts since Q4 2025, correlating with spikes in mobile carrier authentication bypasses documented in the US-CERT Alert AA26-091A on SIM-jacking trends.

What makes this particularly insidious is that end-to-end encryption remains intact—messages are still encrypted between devices—but the attacker controls one endpoint. As Dr. Lena Voss, lead cryptographer at the Open Technology Fund, explained in a recent briefing:
“You can’t encrypt your way out of a compromised identity. If the attacker owns the phone number verified by the carrier and accepted by Signal, they are, cryptographically speaking, the legitimate user. The vulnerability isn’t in the Signal protocol—it’s in the assumption that phone number ownership equals user intent.”
Why Encryption Alone Isn’t Enough: The Identity Trust Gap
This attack vector exposes a fundamental tension in modern secure messaging: the reliance on telephone numbers as immutable identifiers creates a single point of failure tied to notoriously fragile mobile carrier authentication systems. While Signal’s protocol (based on the Double Ratchet Algorithm) is cryptographically sound—verified by audits from NCC Group and academic reviews—its identity layer inherits the weaknesses of the global SS7 and telecom infrastructure. Unlike decentralized identifiers (DIDs) used in experimental platforms like Briar or Matrix with verified key cross-signing, Signal’s model offers no native mechanism for users to cryptographically confirm that a contact’s key hasn’t been rebound to a new device without their knowledge—unless they manually verify safety numbers, a step fewer than 15% of users perform regularly, per Signal’s own 2025 usability study.
This gap has sparked debate within the open-source secure messaging community. Meredith Poulsen, a core contributor to the Matrix ecosystem, noted in a GitHub discussion:
“Signal’s trade-off prioritizes usability over sovereignty. By binding identity to a phone number, they inherit the telco’s attack surface. In Matrix, we accept slightly more complexity in exchange for user-controlled identity via self-signed keys—meaning even if your homeserver is compromised, your identity isn’t automatically transferred to an attacker.”
Enterprise Risks and the False Sense of Compliance
For organizations adopting Signal for compliance-sensitive communications—such as finance, healthcare, or government contractors—the rise of signal-phishing undermines assumptions about message integrity. Regulatory frameworks like FINRA Rule 4511 or HIPAA’s Security Rule focus on encryption and access logs but rarely account for identity spoofing via compromised endpoints. A compromised Signal account can now be used to initiate fraudulent wire requests, leak PHI under the guise of internal comms, or conduct long-term espionage without triggering traditional DLP alerts, since the messages originate from a verified, encrypted channel. This has led some CISOs to reevaluate Signal’s suitability for high-risk environments despite its ease of utilize.

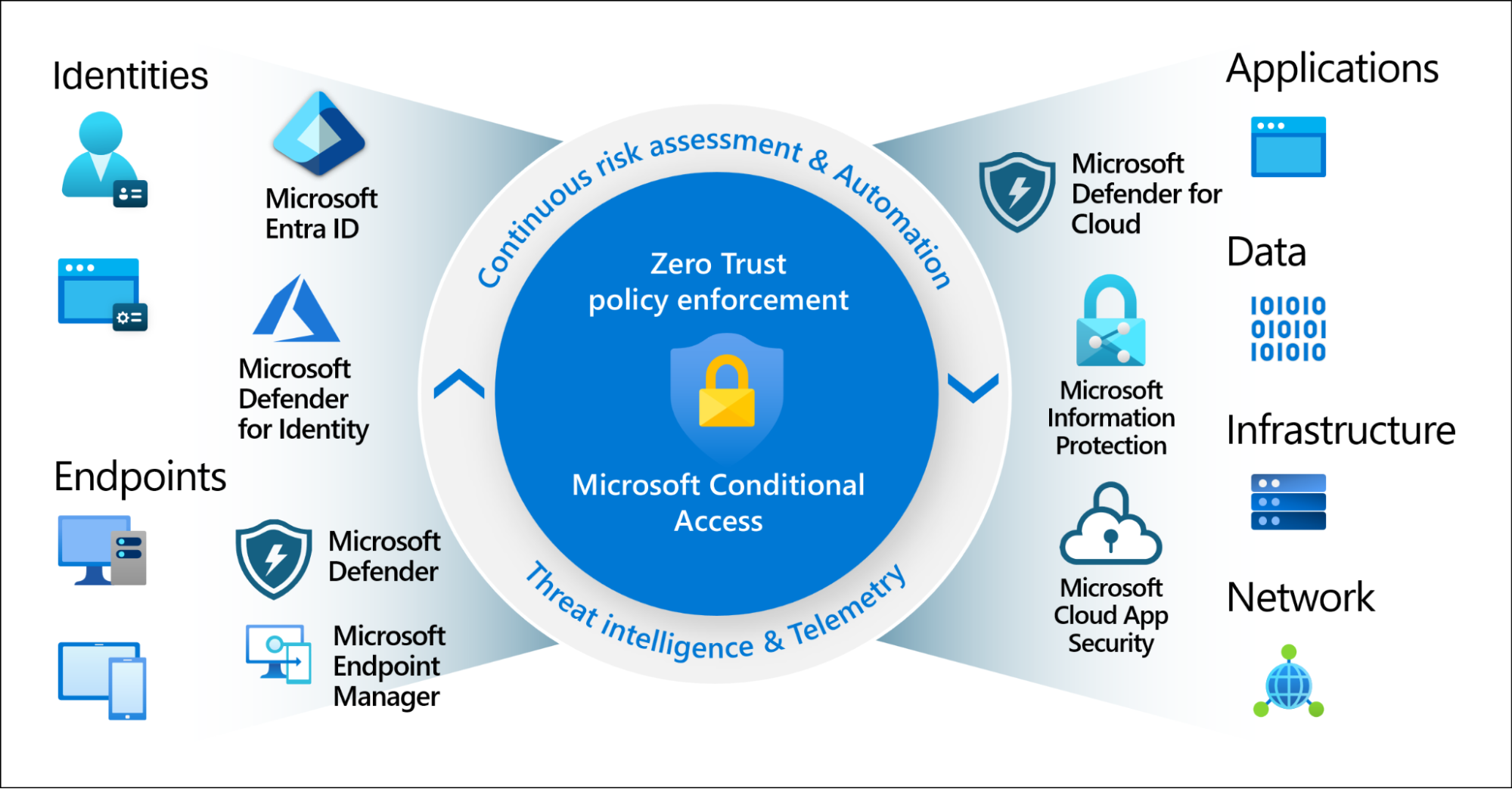
In response, enterprises are layering additional controls: enforcing mobile device management (MDM) policies that block SIM changes without IT approval, deploying mobile threat defense (MTD) solutions that detect anomalous device re-registration (such as those from Lookout or Zimperium), and mandating quarterly safety number re-verification for high-risk contacts. Some are piloting hybrid approaches—using Signal for low-risk comms while reserving platforms with stronger identity controls, like Wickr Pro or Threema Work, for executive or legal teams.
What Users Can Do: Practical Defenses Against Identity Hijacking
For individuals, protection begins with securing the mobile carrier account: setting a PIN or port-freeze with providers like Verizon, T-Mobile, or AT&T to prevent unauthorized SIM swaps. Within Signal, users should enable registration lock (which requires the PIN to re-register the number) and routinely verify safety numbers with contacts—especially after any suspected device loss or unusual behavior. The app now includes a prompt to verify safety numbers when a contact’s key changes, but users must actively compare the displayed 60-digit number or scan the QR code. Disabling cloud backups—or ensuring they are encrypted with a user-controlled passphrase—prevents attackers from accessing message history even if they gain control of the device.

Critically, users must treat any unexpected request for money, credentials, or sensitive data—even if it comes from a verified contact—as potentially fraudulent until confirmed via an out-of-band channel (like a phone call or in-person conversation). As the FBI’s IC3 unit warned in its 2025 Internet Crime Report:
“The most dangerous phishing attempts don’t glance suspicious—they look exactly like a message from your boss, your friend, or your family. Trust, but verify—through a separate channel.”
The Broader Implications: Trust in the Post-Truth Digital Age
Signal-phishing exemplifies a larger shift in cyber conflict: attacks are no longer primarily about breaking code but about breaking trust. As cryptographic protocols grow stronger, adversaries increasingly target the human and institutional layers that bind identity to technology—whether through telecom vulnerabilities, social engineering, or exploiting usability trade-offs in secure design. This trend challenges the notion that end-to-end encryption alone guarantees security and underscores the need for usable identity verification systems that don’t burden users but still resist takeover.
Looking forward, the debate may drive innovation in decentralized identity (DID) standards backed by the W3C and initiatives like the Decentralized Identity Foundation, potentially influencing future versions of Signal or inspiring new platforms that separate identity from phone numbers entirely. Until then, the most secure message is only as safe as the identity behind it—and in 2026, that identity is proving surprisingly fragile.

