Threema is decoupling digital identity from telephony by replacing phone-number-based registration with randomized IDs and integrating post-quantum cryptography (PQC). This architectural shift eliminates SIM-swapping vulnerabilities and protects current encrypted streams from “Store Now, Decrypt Later” quantum attacks, establishing a new benchmark for sovereign communication in 2026.
The industry has long treated the phone number as a convenient proxy for identity. In reality, it is a legacy artifact—a leaky, centralized identifier owned by a telecom provider, not the user. For the security-conscious, the phone number is not a key; it is a liability.
When a messenger relies on a phone number, it inherits the fragility of the SS7 protocol and the susceptibility of the human element at the telco storefront. SIM swapping isn’t a sophisticated hack; it is a social engineering exploit. By stripping the phone number from the onboarding process, Threema isn’t just adding a feature—it is removing a systemic attack vector.
The Mathematical Imperative: Defeating the Quantum Clock
While the removal of phone numbers solves the identity problem, the implementation of post-quantum cryptography (PQC) solves the persistence problem. Most current end-to-end encryption (E2EE) relies on Elliptic Curve Diffie-Hellman (ECDH) or RSA. These are computationally expensive for classical computers to break, but trivial for a sufficiently powerful quantum computer utilizing Shor’s algorithm.
We are currently living in the era of “Store Now, Decrypt Later” (SNDL). State actors are harvesting encrypted traffic today, betting on the fact that by the time a cryptographically relevant quantum computer (CRQC) exists, the data will still be valuable. If you are discussing corporate secrets or diplomatic cables today, a 2030 quantum breakthrough renders today’s encryption moot.
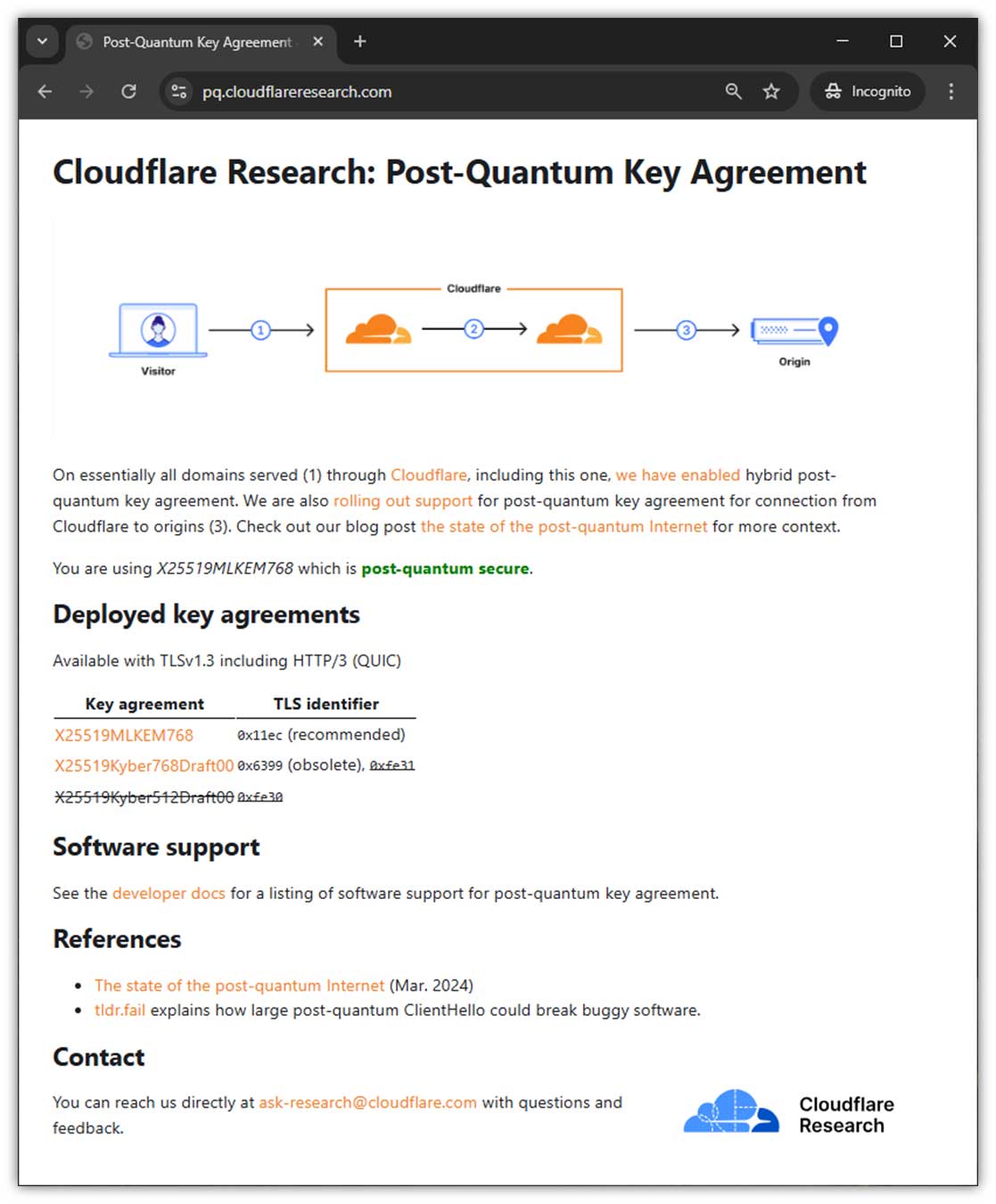
Threema’s pivot toward PQC involves integrating lattice-based cryptography, specifically moving toward standards like NIST’s ML-KEM (formerly Kyber). Unlike traditional prime factorization, lattice-based problems are believed to be resistant to both classical and quantum attacks. This isn’t just a software update; it’s a fundamental change in how the key exchange happens at the transport layer.
It is a race against the hardware.
The 30-Second Verdict: Identity vs. Privacy
- The Win: Complete decoupling of identity from SIM cards. No phone number = no SIM-swap risk.
- The Tech: Lattice-based PQC protects against future quantum decryption.
- The Trade-off: Increased friction in user discovery (you can’t just “sync contacts”).
- The Verdict: Essential for high-risk users; a slight hurdle for the casual consumer.
Comparing the Privacy Stack: Threema vs. The Giants
To understand why Threema’s approach is an outlier, we have to look at the competitive landscape. Signal, while the gold standard for protocol transparency, still clings to the phone number as a primary identifier, despite introducing usernames to mask them. WhatsApp, meanwhile, is a metadata goldmine for Meta, regardless of the encryption of the message content itself.
| Feature | Threema (2026) | Signal | |
|---|---|---|---|
| Identifier | Randomized Threema ID | Phone Number (Usernames as alias) | Phone Number |
| PQC Integration | Native Lattice-based | Experimental/PQXDH | None/Proprietary |
| Infrastructure | Swiss-based / Sovereign | Centralized / AWS-reliant | Meta Global Infrastructure |
| Metadata Footprint | Minimal/Zero-Knowledge | Low (Sealed Sender) | High (Social Graphing) |
The delta here is the “trust anchor.” Signal trusts the phone number to verify the user. Threema trusts a locally generated key pair. By shifting the trust anchor from a third-party telecom to the device’s own Trusted Execution Environment (TEE), the user regains ownership of their digital existence.
The Ecosystem Friction: Privacy as a Luxury Good
There is a reason why Meta and Signal haven’t fully abandoned the phone number: friction. The “magic” of modern messaging is the seamless onboarding. You download an app, it scans your address book, and boom—half your friends are already there. This is “growth hacking” at its most invasive.

Threema’s model rejects this. By requiring a manual exchange of IDs or QR codes, they are intentionally introducing friction. This creates a psychological and technical barrier that filters for users who actually value privacy over convenience. From a market dynamics perspective, this positions Threema not as a mass-market social tool, but as a specialized utility for the “security elite”—journalists, activists, and C-suite executives.
“The transition to post-quantum primitives is not optional; it is a survival requirement for any platform claiming to provide long-term confidentiality. The real challenge isn’t the math—it’s the implementation. If you botch the integration of ML-KEM into the existing handshake, you create new side-channel vulnerabilities.”
This sentiment is echoed across the Open Quantum Safe community, where the focus has shifted from theoretical proofs to the brutal reality of implementation. The risk is that in the rush to be “Quantum Ready,” developers might introduce bugs into the key encapsulation mechanism (KEM), leading to vulnerabilities that are easier to exploit than the quantum threats they are trying to prevent.
The Macro-Market Shift: Sovereign Infrastructure
Beyond the code, there is the geography. Threema’s reliance on Swiss infrastructure is a strategic hedge against the “Cloud Act” and other extraterritorial data grabs. When your data lives on a server in a jurisdiction that doesn’t recognize foreign subpoenas without strict local judicial review, the legal shield is as important as the cryptographic one.

This is the “Sovereign Stack” movement. We are seeing a trend where high-security entities are moving away from the “Massive Three” clouds (AWS, Azure, GCP) and toward localized, hardened infrastructure. It is a reversal of the 2010s centralization trend.
The integration of PQC and the removal of phone numbers are two sides of the same coin: the pursuit of asynchronicity. The goal is to make the communication channel independent of the state, the telecom, and the future of computing power.
The Path Forward for Enterprise IT
For CTOs and CISOs, the Threema model provides a blueprint for internal communications. Relying on corporate mobile plans for “secure” comms is a fallacy. To truly mitigate the risk of corporate espionage, organizations must move toward identity systems that are decoupled from the hardware provider. So implementing internal PKI (Public Key Infrastructure) and demanding PQC-readiness from every vendor in the stack.
The era of “convenient security” is over. The future is encrypted, anonymized, and mathematically resilient. If your identity is still tied to a 10-digit number issued by a carrier, you aren’t a user—you’re a target.

