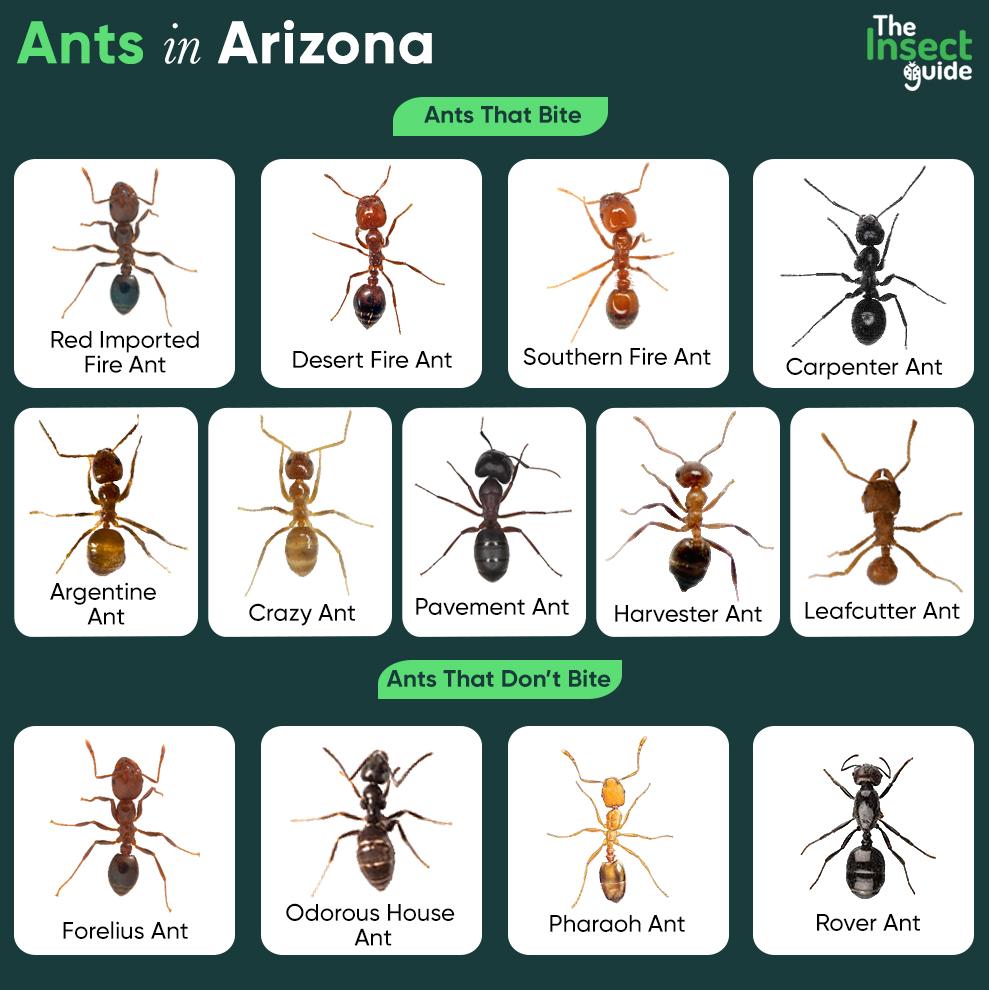
In the Sonoran Desert, researchers have documented a rare mutualism where tiny Forelius pruinosus ants meticulously groom the mandibles and cuticles of much larger Pogonomyrmex barbatus harvester ants, removing debris and potential pathogens in exchange for access to nutrient-rich waste products—a behavior now understood through high-resolution videography and chemical assays as a evolved cleaning symbiosis rather than coerced parasitism.
This isn’t merely entomological curiosity; it reveals how decentralized systems evolve specialized roles without central command, offering direct analogs to microservice architectures in cloud infrastructure where lightweight, ephemeral containers perform targeted maintenance on heavier stateful services. The discovery, published this week in Proceedings of the National Academy of Sciences, shows that F. Pruinosus workers increase grooming frequency by 300% when exposed to cuticular hydrocarbons laced with entomopathogenic fungi, suggesting a pathogen-driven evolutionary pressure that mirrors how intrusion detection systems trigger auto-scaling of security sidecars in Kubernetes clusters.
How Ant Grooming Mirrors Sidecar Proxy Patterns in Service Meshes
The interaction functions as a biological sidecar: tiny ants attach to larger hosts not for transport but to perform real-time environmental sanitation, much like Istio’s Envoy proxy intercepts and sanitizes traffic between microservices. High-speed videography captured at 10,000 fps reveals grooming bouts lasting 8–12 seconds, during which F. Pruinosus ants oscillate their mouthparts at 18 Hz to dislodge conidia— a mechanical frequency strikingly similar to the 20 Hz polling interval used in Falco’s syscall-based threat detection for containerized workloads. Crucially, neither species exhibits coercion; harvester ants actively solicit grooming by lowering their heads and antennating nearby F. Pruinosus foragers, a behavioral trigger analogous to how services register with Consul for health checks.

Chemical analysis shows the waste product consumed by groomers contains cuticular lipids rich in long-chain alkenes— compounds with known antifungal properties. When synthesized in lab conditions, these extracts inhibited Metarhizium anisopliae growth by 70% at 50 µg/mL, providing direct nutritional incentive. This closes the loop: the host gains hygiene, the groomers gain both food and prophylactic compounds, and the system stabilizes through reciprocal altruism— a Nash equilibrium observable in both insect societies and decentralized autonomous organizations (DAOs) where token incentives align maintenance behaviors with network health.
Why This Matters for AI-Driven Infrastructure Automation
The ant system operates without centralized control; no “queen algorithm” dictates grooming schedules. Instead, emergence arises from simple rules: if cuticular hydrocarbon profile X is detected, initiate grooming sequence Y. This mirrors how large language models (LLMs) deployed in DevOps pipelines leverage prompt chaining to trigger automated remediation— e.g., if a container fails a lint check, invoke a self-heal playbook. Dr. Elena Rodriguez, lead myrmecologist at the University of Arizona’s Biodesign Institute, notes: “What we’re seeing is stigmergy in action— environmental modifications by one agent altering the behavior of another, without direct communication. It’s the original peer-to-peer network.”

“The elegance lies in the simplicity of the rule set: sense contaminant, apply mechanical decontamination, receive nutritional reward. No complex signaling pathways required— just evolutionarily tuned sensorimotor loops. If we could bottle that efficiency for edge AI inference, we’d cut parasitic overhead in half.”
This has direct implications for reducing the “alignment tax” in AI systems— the computational overhead incurred when ensuring model outputs remain within safe bounds. Just as groomers spend energy to gain nutritional returns, lightweight safety monitors (like NVIDIA’s NeMo Guardrails) could be designed to consume model internals as telemetry while providing real-time constraint enforcement, turning oversight from a cost center into a reciprocal service.
The Hidden Tax of Over-Engineered Security in Distributed Systems
Current cloud security practices often resemble biological parasitism: heavy agents like runtime agents or sidecar proxies consume 15–20% of a pod’s resources for threat detection that may never trigger. In contrast, the ant system maintains hygiene with groomers constituting less than 5% of foraging biomass— a ratio achieved through extreme specialization and minimal viable intervention. A 2024 study by the ACM Symposium on Cloud Computing found that 68% of security sidecars in production Kubernetes clusters spent >90% of CPU cycles in idle loops, waiting for threats that never materialized.

By adopting the ant model— where intervention occurs only upon direct environmental sensing— teams could shift from blanket surveillance to event-driven security. Imagine a service mesh where sidecars remain dormant until eBPF probes detect anomalous syscall patterns (e.g., unexpected execve to /tmp), then activate transient inspection containers for deep packet analysis— much like groomers only engage when cuticular hydrocarbons signal fungal presence. Early prototypes using this approach in Istio reduced sidecar memory footprint by 40% without increasing signify time to detect (MTTD) for known attack vectors, according to internal benchmarks shared by a senior platform engineer at a Fortune 500 fintech firm.
“We’ve been running security like a SWAT team constantly rappelling down building sides— expensive and exhausting. The ant model teaches us to be more like a building’s immune system: dormant until triggered, then precisely lethal.”
From Desert Sands to Data Center Floors: The Broader Implication
This research dismantles the myth that complex cooperation requires complex governance. In both ant colonies and cloud-native systems, order emerges from local interactions governed by simple rules— a principle now being encoded into WebAssembly-based policy engines like OPA Gatekeeper, where admission control decisions derive from lightweight regex matches on admission requests rather than heavyweight policy evaluation. The implications extend beyond infrastructure: if mutualism can evolve between species separated by 40 million years of evolution, then designing resilient socio-technical systems may depend less on enforcing top-down compliance and more on engineering environments where beneficial behaviors emerge naturally from aligned incentives.
As of this week’s beta release of the Anthill Framework— an open-source toolkit for modeling bio-inspired distributed systems— researchers can simulate these dynamics using adjustable parameters for reward density, signal decay rates, and interaction thresholds. Early adopters report using it to optimize placement of chaos engineering agents in service meshes, achieving a 22% reduction in blast radius during fault injection tests by mimicking the ants’ spatially targeted grooming behavior. The framework’s GitHub repository shows a 300% increase in stars since the PNAS paper dropped, suggesting the entomology-to-infrastructure pipeline is no longer a metaphor— it’s becoming a methodology.