A Reddit user recently surfaced a client-side vulnerability in Blizzard’s Hearthstone, enabling the exposure of hidden card data during active matches. This exploit targets the game’s synchronization protocols, highlighting critical flaws in how the Unity-based engine handles state management between the server and the local client-side memory stack.
The discovery, which surfaced in the r/hearthstone community earlier this week, is more than just a “glitch”—it is a masterclass in why client-authoritative data models are a security nightmare. By inspecting the memory heap while the game state is being serialized, a user can effectively strip away the “fog of war” that keeps an opponent’s deck composition hidden until the moment of play.
The Anatomy of an Information Leak
At its core, Hearthstone relies on a complex Unity engine implementation that must balance low-latency responsiveness with server-side validation. However, the current architecture appears to be pushing too much metadata to the client’s RAM. When the game server sends a packet to update the match state, it often includes “future” or “hidden” object references that the client-side UI is instructed to ignore until specific triggers are met.
If you have access to a memory debugger or a packet sniffer, that “ignore” command is just a suggestion. The data is already sitting in your local memory space, waiting to be read. This represents a classic example of poor data sanitization at the architectural level. Blizzard isn’t just sending “your turn” data; they are sending the entire deck object, relying on the client software to hide it. In the world of cybersecurity, this is equivalent to sending an encrypted file along with the password in the same payload.
“The problem with modern game engines is the trade-off between performance and security. By serializing game objects to the client to save on round-trip latency, developers are creating a massive attack surface. If the client doesn’t need to know the identity of a card, it shouldn’t be in the client’s memory address space, period,” says Dr. Aris Thorne, a lead systems architect specializing in real-time distributed networks.
Why This Threatens the Competitive Ecosystem
This isn’t just about a few players getting an unfair advantage in a digital card game. It speaks to the broader fragility of “Games as a Service” (GaaS) models. When developers prioritize rapid feature deployment—like the recent, buggy expansion rollout—they often sacrifice the rigorous, deep-packet inspection required to prevent these types of memory-injection exploits.
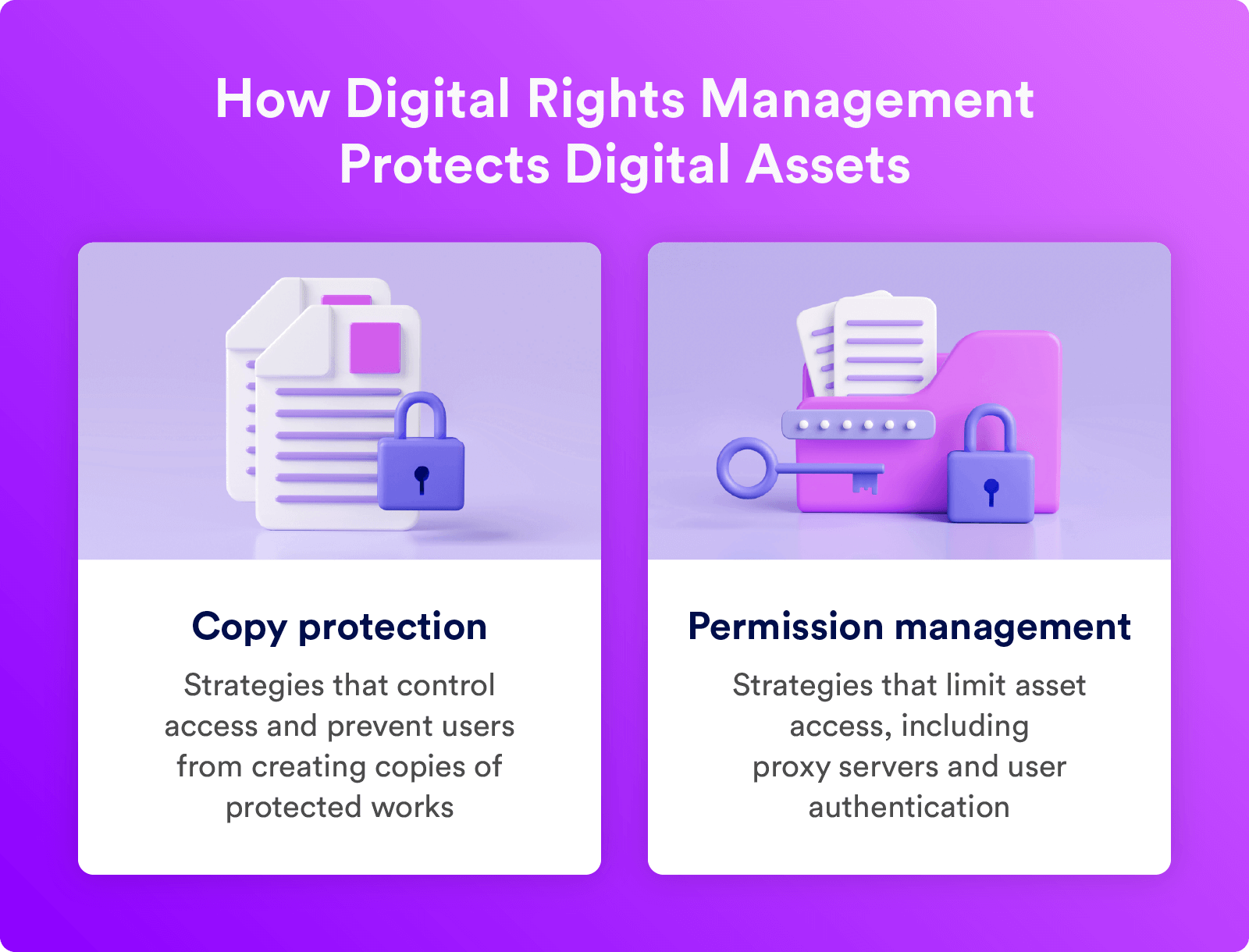
The broader tech war here is one of Digital Rights Management (DRM) and integrity. If the game engine cannot trust the client, it must move to a “thin client” model where the server renders the game state entirely. But that requires a massive investment in server-side compute, something Blizzard has been trying to offload to the end-user’s device for years to keep operating costs low.
The Technical Breakdown of the Exploit
- Injection Vector: Memory scraping of the Unity
MonoBehaviourinstances. - Protocol Vulnerability: Over-privileged data transmission in the game’s proprietary binary protocol.
- Detection Difficulty: Since the exploit is passive (reading memory rather than modifying it), standard anti-cheat heuristics—which look for behavioral anomalies like auto-clicking—often fail to flag it.
- Mitigation Path: Moving to a server-side “Need-to-Know” packet structure.
The Developer’s Dilemma: Latency vs. Security
Blizzard is currently caught in a classic “Tech Debt” trap. To fix this, they would need to refactor the way their backend handles object serialization. This isn’t a hotfix; it’s a fundamental change to how the game handles state synchronization. In a world where QUIC/HTTP3 is becoming the standard for low-latency communication, Blizzard’s reliance on legacy socket-based communication is showing its age.

If they move to a stricter server-side validation model, players might experience “input lag” or “jitter” as the client waits for the server to confirm every single card reveal. If they don’t, they risk the integrity of the competitive ladder, which is the entire value proposition of the platform. It is a zero-sum game for the developers.
The 30-Second Verdict
For the average user, Which means the competitive integrity of the game is currently compromised. If you are playing at a high rank, assume that your opponent might be using memory-resident tools to view your hand. This is not a “hack” in the sense of a remote breach; it is a fundamental flaw in the game’s data distribution strategy.
Until Blizzard patches the underlying API to prevent the client from receiving hidden card objects, the only real protection is the inherent difficulty of setting up these tools. However, as these methods become more streamlined and easier to deploy, the barrier to entry for cheaters will continue to drop. We are witnessing the inevitable collision between convenience-driven software architecture and the reality of modern CVE-level vulnerabilities.
Keep your software updated, avoid third-party “deck trackers” that haven’t been vetted by the community, and watch for official statements from Blizzard regarding a potential client-side patch. If they don’t move the state-management logic to the server, the game’s competitive credibility will continue to erode.
The tech is only as secure as its weakest link. In this case, the weakest link is the assumption that the user’s hardware can be trusted with secret data. It never should have been.
