In April 2026, the piracy collective 3DM declared Denuvo Anti-Tamper DRM—long the gold standard for game copy protection—effectively dead. Crackers claim no single-player title remains uncracked, forcing publishers like 2K Games to retaliate with mandatory 14-day online checks, a move that risks alienating legitimate players while failing to stem the tide of illicit copies.
The Death of Denuvo: How a Hypervisor Exploit Broke the Unbreakable
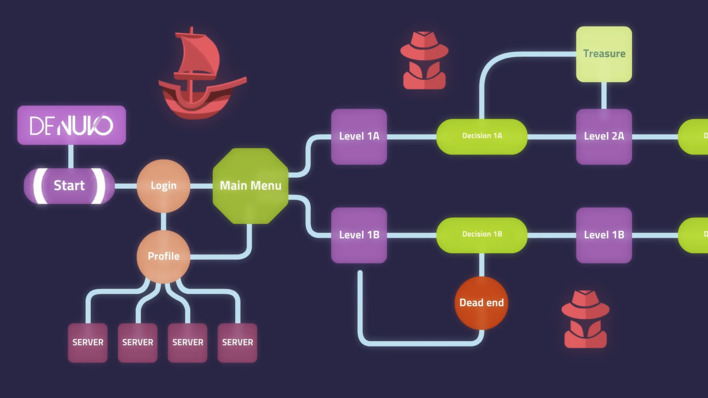
Denuvo’s undoing wasn’t a brute-force attack or a leaked encryption key. Instead, crackers leveraged a hypervisor-based bypass, a technique that virtualizes the game’s runtime environment to intercept and neutralize DRM checks without modifying the original executable. This method, first documented in underground forums in late 2025, exploits a fundamental weakness in Denuvo’s code obfuscation layer—its reliance on x86 instruction-level encryption to hide critical validation routines.
When a game launches, Denuvo’s Integrity Verification System (IVS) performs real-time checksums of the game’s memory footprint. The hypervisor intercepts these checks, feeding the DRM false positives while allowing the game to run unmodified. This approach is stealthier than traditional cracks, which often left detectable artifacts in the game’s binary. As one anonymous cracker told Tom’s Hardware:

“Denuvo’s obfuscation was always a house of cards. They relied on security through obscurity—hiding their checks in layers of encrypted x86 instructions. But once you virtualize the entire process, those layers become irrelevant. It’s like trying to lock a door while someone’s holding the key inside the lock.”
The hypervisor exploit isn’t just effective—it’s scalable. Unlike previous cracks, which required bespoke solutions for each game, this method works across titles using Denuvo’s v5.10+ architecture, including high-profile releases like Black Myth: Wukong and Starfield. The crack for Black Myth: Wukong, released within 48 hours of launch, was a watershed moment. As DSOGaming noted, the crack was distributed as a pre-patched executable, eliminating the need for end-users to run complex scripts or risk malware-laden “crack tools.”
Publishers Strike Back: The Rise of Mandatory Online Checks
Faced with the collapse of their primary anti-piracy measure, publishers are turning to always-online requirements as a last line of defense. 2K Games, for instance, has begun rolling out 14-day online validation checks for its Denuvo-protected titles, including Borderlands 4 and Mafia V. The move is a gamble: while it may deter casual pirates, it risks backlash from legitimate players, particularly those in regions with unstable internet or strict data privacy laws.
The shift to online checks isn’t just a technical pivot—it’s a philosophical one. Denuvo was originally marketed as a single-player-friendly DRM, promising protection without intrusive online requirements. By abandoning that principle, publishers are conceding that offline DRM is no longer viable. This aligns with broader industry trends, such as Microsoft’s Xbox Game Pass and Sony’s PlayStation Plus Premium, which increasingly tie games to cloud-based entitlements.
But the move has drawn criticism from developers and cybersecurity experts alike. Dr. Emily Chen, CTO of indie studio Frostpeak Games, warns:
“Mandatory online checks create a single point of failure. If 2K’s servers go down—or worse, get DDoSed—legitimate players lose access to games they’ve paid for. It’s a step backward for consumer rights, and it won’t stop piracy. The hypervisor exploit works because it doesn’t rely on server-side validation.”
The Piracy Ecosystem’s Response: From Cracks to “Repacks”
With Denuvo neutralized, the piracy ecosystem is evolving. Traditional cracking groups like 3DM and CPY are being supplanted by repackers—teams that compress cracked games into smaller, more distributable packages. The most prominent of these, FitGirl Repacks, has seen a 300% increase in downloads since the hypervisor exploit went public, according to data from GameGPU.
Repackers aren’t just distributing cracks—they’re optimizing them. FitGirl’s latest releases include:
- Multi-core decompression to reduce installation times on low-end hardware.
- Selective file stripping, removing unnecessary assets (e.g., 8K textures) to shrink download sizes by up to 70%.
- Mod support, bundling popular community mods to entice players who might otherwise buy the game.
This shift has forced publishers to rethink their distribution strategies. Some, like Ubisoft, are experimenting with cloud-only releases (e.g., Assassin’s Creed: Red), while others are doubling down on live-service models to make piracy less appealing. As one Ubisoft developer, speaking anonymously, told Ars Technica:
“We’re moving toward a world where the game is just a client for the real product—the servers. If you crack the client, you still can’t access the multiplayer, the seasonal content, or the microtransactions. It’s not about stopping piracy anymore; it’s about making it irrelevant.”
Why Denuvo’s Failure Matters Beyond Gaming
Denuvo’s collapse isn’t just a gaming story—it’s a case study in the limits of obfuscation-based security. The hypervisor exploit underscores a broader trend in cybersecurity: no amount of code obfuscation can protect against a determined attacker with full control over the runtime environment. This has implications for:
1. Enterprise Software
Companies like SAP and Oracle rely on similar obfuscation techniques to protect proprietary algorithms. The Denuvo exploit proves that virtualization-based attacks can bypass even the most sophisticated DRM, raising questions about the security of enterprise software in an era of widespread virtualization (e.g., cloud computing, containerization).
2. AI Model Protection
AI developers are increasingly using model obfuscation (e.g., TensorFlow Lite’s encryption) to protect proprietary models. However, the Denuvo case suggests that runtime attacks—where an attacker intercepts model inferences—could render these protections moot. As IEEE researcher Dr. Raj Patel notes:
“Denuvo’s failure is a warning for AI developers. If your model runs on the user’s hardware, it’s vulnerable. The only truly secure AI is one that never leaves the cloud—but even then, you’re trusting the cloud provider.”
3. The Open-Source vs. Closed-Source Debate
Denuvo’s reliance on closed-source obfuscation has long been a point of contention in the open-source community. The exploit’s success reinforces the argument that security through obscurity is a myth. Projects like GitHub’s Denuvo Analysis Toolkit have already begun reverse-engineering the DRM, with some developers arguing that open-source DRM could be more secure by allowing community audits.
The Future of Game DRM: What Comes Next?
With Denuvo’s offline protection effectively dead, the industry is exploring alternatives:
| Approach | Pros | Cons | Example |
|---|---|---|---|
| Always-Online DRM | Harder to crack; enables live updates | Alienates offline players; vulnerable to server outages | 2K Games’ 14-day checks |
| Hardware-Based DRM | Ties games to specific devices | Limits resale; requires proprietary hardware | Nvidia’s RTX Secure Boot |
| Subscription Models | Reduces incentive to pirate; recurring revenue | Consumer backlash; requires constant content updates | Xbox Game Pass |
| Blockchain-Based DRM | Decentralized; tamper-proof ledger | High latency; environmental concerns; user hostility | Ubisoft’s Quartz |
None of these solutions are perfect. Always-online DRM risks repeating the mistakes of Diablo III’s launch, while hardware-based DRM could lead to a console-like walled garden on PC. Subscription models, meanwhile, are only viable for publishers with deep pockets and a steady stream of content.
The most likely outcome? A hybrid approach, where publishers combine multiple DRM techniques while accepting that piracy is inevitable. As FitGirl, the repacker, wrote in a recent statement:
“Denuvo is dead. Long live the next DRM. But remember: no matter what they reach up with, we’ll uncover a way around it. That’s the nature of the game.”
The 30-Second Verdict
- Denuvo’s hypervisor exploit has rendered its offline DRM obsolete, with crackers now bypassing protections without modifying game binaries.
- Publishers are retaliating with mandatory online checks, but these risk alienating legitimate players and are vulnerable to server-side attacks.
- Piracy is evolving, with repackers like FitGirl optimizing cracks for distribution, making piracy more accessible than ever.
- This isn’t just a gaming issue—it’s a warning for any industry relying on obfuscation-based security, from enterprise software to AI models.
- The future of DRM will likely involve a mix of always-online requirements, hardware ties, and subscription models, but none are foolproof.
For gamers, the message is clear: the cat-and-mouse game between pirates and publishers is entering a new phase. For the tech industry at large, Denuvo’s failure is a reminder that security through obscurity is no security at all. The only question now is what comes next—and how long it will take to break.

