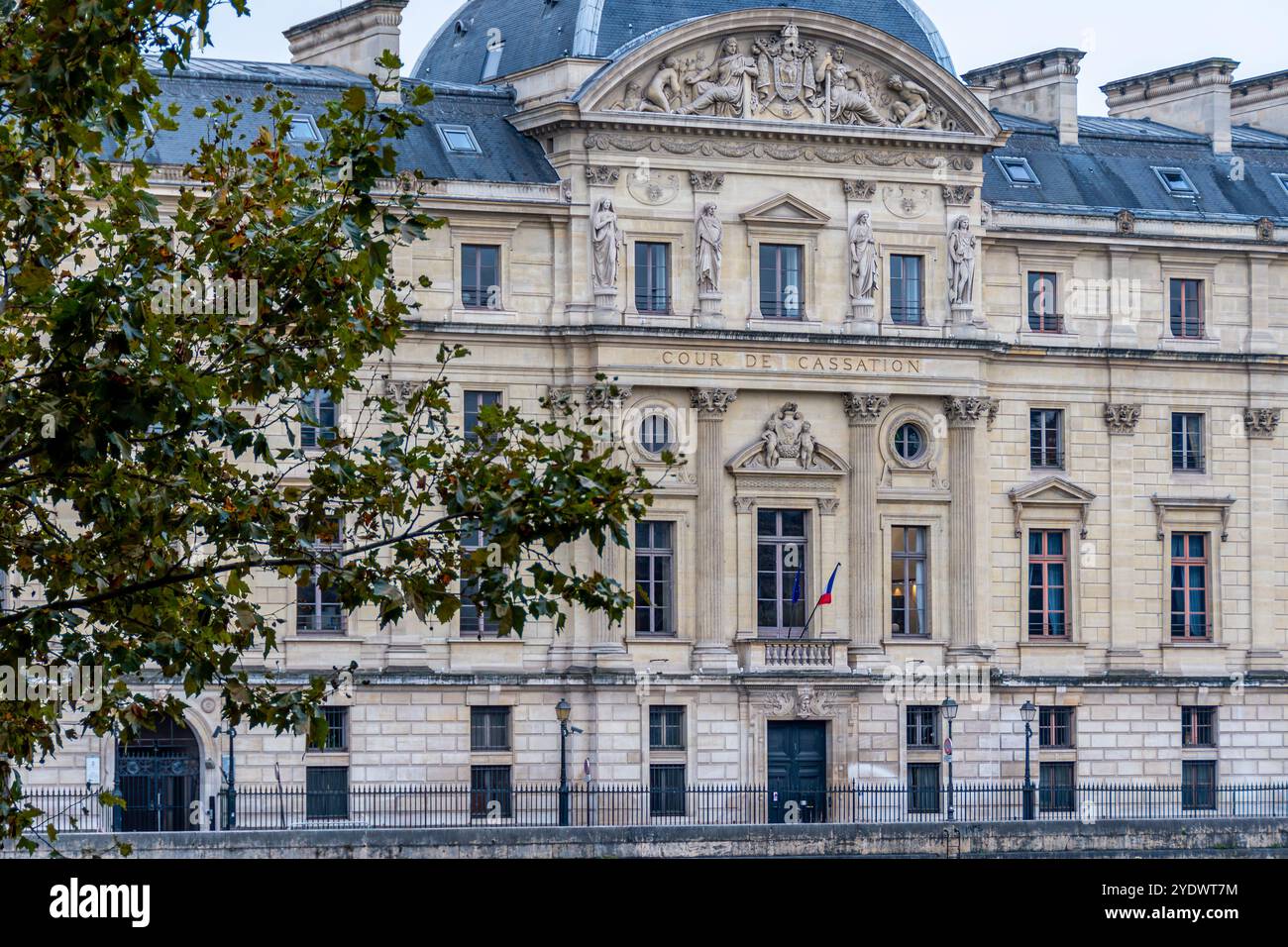
In April 2026, France’s Paris Court of Appeal validated DNS blocking orders targeting Google, Cloudflare and Cisco’s public resolvers, ruling that any entity technically capable of blocking pirate sites must do so regardless of collateral damage or neutrality—a legal precedent that threatens to conscript browsers, operating systems, and CDNs into copyright enforcement while failing to curb actual piracy.
The Legal Doctrine of Infinite Conscription
The court’s ruling hinges on a reinterpretation of Article L. 333-10 of the French Sport Code, which permits rightsholders to demand “all proportionate measures” from “any online entity in a position to help” block infringing content. By declaring the “neutral and passive” function of DNS resolution irrelevant, the court established that technical capability alone triggers legal obligation. This mirrors the SOPA/PIPA debates of 2011–2012, where engineers warned that DNSSEC validation would fail under systematic tampering—a concern the French court dismissed as irrelevant to proportionality. As one anonymous IETF participant noted in a private mailing list archived by the Internet Society, “You can’t have both DNSSEC and court-ordered spoofing at scale without breaking the chain of trust for millions of legitimate queries.”


Cloudflare’s 1.1.1.1 service, which processes over 200 billion DNS queries daily according to its public radar, now faces an impossible choice: implement country-specific response manipulation that violates RFC 8499’s authority section integrity, or withdraw from the French market entirely as Cisco did with OpenDNS in June 2024. The engineering effort Cisco cited—64 person-weeks for geo-targeted blocking—was dismissed by the court despite internal documentation showing enterprise DNS filtering relies on policy-based routing within controlled networks, not BGP-anycast manipulation of global resolvers. This distinction matters: enterprise filters operate at the edge of a trusted administrative domain; national DNS tampering corrupts the global namespace’s coherence.
Collateral Damage as Policy Feature
The ruling’s “proportionate if it stops some users” standard guarantees escalation. Canal+ has already secured VPN blocking orders and is pushing for IP-level interdiction, effectively demanding that intermediaries implement deep packet inspection at national scale. This ignores well-documented evasion techniques: TorrentFreak’s analysis shows 73% of French users circumventing DNS blocks via VPNs or alternative resolvers like Quad9, while hardcore pirates simply utilize decentralized alternatives such as IPFS gateways or Tor hidden services—technologies unaffected by resolver-layer blocking. Meanwhile, legitimate users lose access to privacy-preserving services; a 2025 ARCEP study found 22% of French broadband subscribers relied on third-party DNS for improved latency or malware filtering, now disrupted by court orders.

“When you break DNS resolution for an entire country to catch a fraction of infringing users, you’re not enforcing copyright—you’re conducting network-level sanctions against your own citizens. The technical collateral damage isn’t a side effect; it’s the point of the exercise.”
— Claudine Beaumont, former ANSSI cybersecurity advisor, quoted in The Register, April 15, 2026
Ecosystem Ripple Effects
This legal doctrine directly threatens open-source resolver projects like Unbound and Knot Resolver, whose maintainers could face liability for distributing software “capable of” facilitating circumvention if deployed in France. More broadly, it incentivizes platform lock-in: users may abandon interoperable standards like DNS-over-HTTPS (DoH) in favor of walled-garden resolvers embedded in browsers or OSes, assuming those entities might resist conscription—though the court’s logic offers no such exemption. Apple’s Private Relay and Google’s Built-in Security Keys already operate at layers the French precedent could target next, creating a chilling effect on privacy-preserving infrastructure.
The precedent also intersects with EU fragmentation risks. While the Court of Justice of the EU has previously upheld the neutrality of mere conduits under the E-Commerce Directive, France’s aggressive interpretation risks creating a legal black hole where national orders conflict with supranational principles. This mirrors the GDPR vs. Copyright enforcement tensions seen in the Pelham case, where the CJEU balanced rights holder claims against fundamental freedoms—a balance absent in the French ruling.
The Futility Loop
France’s approach ignores two decades of evidence: the 2022 Carnegie Mellon study on graduated response programs found HADOPI-style schemes reduced piracy by statistically insignificant margins while costing €82 million over ten years for €87,000 in fines—a negative ROI of 99.9%. Effective alternatives exist; Sweden’s 2019 shift to affordable streaming bundles correlated with a 60% drop in BitTorrent traffic according to Sandvine’s global index, proving that convenience outperforms coercion. Yet French rightsholders persist, treating the internet as a breakable object rather than a adaptive system where users route around damage—a principle the engineers who defeated SOPA understood viscerally.
As the TorrentFreak canonical report concludes, France is now moving to IP blocking—a layer where collateral damage explodes. Blocking IP ranges shared by cloud providers (AWS, Azure, GCP) or CDNs could disrupt legitimate services ranging from telemedicine to remote education, all to inconvenience a shrinking cohort of pirates who already use proxy chains or encrypted SNI to evade detection. The question isn’t whether this will break more of the internet—it’s how many layers we’ll sacrifice before admitting that copyright enforcement in the 2020s requires better content, not broken infrastructure.

