When German federal investigators raided a nondescript apartment in Cologne last autumn, they weren’t expecting to find the administrative backbone of a global terror network. Tucked inside a hollowed-out copy of Goethe’s Faust were spreadsheets—meticulously formatted in Excel—listing over 1,200 individuals who had pledged allegiance to the Islamic State, complete with aliases, nationalities, dates of birth, and in some cases, biometric data harvested from Syrian refugee camps. What began as a routine surveillance operation targeting suspected money laundering has unraveled into one of the most significant intelligence coups in Europe’s fight against jihadist terrorism since the fall of Mosul.
This isn’t just about names on a list. It’s about the chilling efficiency with which ISIS replicated state-like bureaucracy to manage its foreign fighter pipeline—and how fragments of that machinery now sit in German evidence rooms, offering an unprecedented window into the group’s internal mechanics. For analysts, the discovery confirms a long-suspected truth: beneath the propaganda videos and battlefield brutality lay a hyper-organized apparatus that handled payroll, logistics, and even human resources with the precision of a multinational corporation.
The Ledger of Loyalty: How ISIS Managed Its Global Ranks
The documents recovered by Germany’s Federal Criminal Police Office (BKA) reveal a system designed for scalability and control. Fighters were assigned numerical IDs upon joining, tracked through stages of training, deployment, and, in some cases, administrative reassignment. One spreadsheet, labeled “Foreign Brotherhood – Europe Division,” includes columns for “Current Status” (active, detained, killed, returned) and “Family Ties in Host Country,” suggesting the group monitored not just combatants but potential sleeper cells through familial anchors.

What’s particularly striking is the use of coded language to evade detection. Terms like “student exchange program” referred to jihadist training camps in Libya, while “wedding planning” denoted marriage arrangements between foreign fighters and local women—a tactic used to secure residency and legitimacy. These euphemisms mirror corporate jargon, revealing how ISIS adopted bureaucratic camouflage to blend into the noise of legitimate migration flows.
“This level of record-keeping isn’t accidental—it’s doctrinal,” says Dr. Nada Moumtaz, a terrorism researcher at the University of Oxford who has studied ISIS administrative structures.
“They didn’t just desire to fight; they wanted to govern. And governance requires data. These files show they were building a transnational bureaucracy long before they declared a caliphate.”
Her analysis, published in the Journal of Deradicalization last year, traces the evolution of ISIS record-keeping from looted Iraqi government forms to custom-built databases hosted on encrypted servers in Turkey.
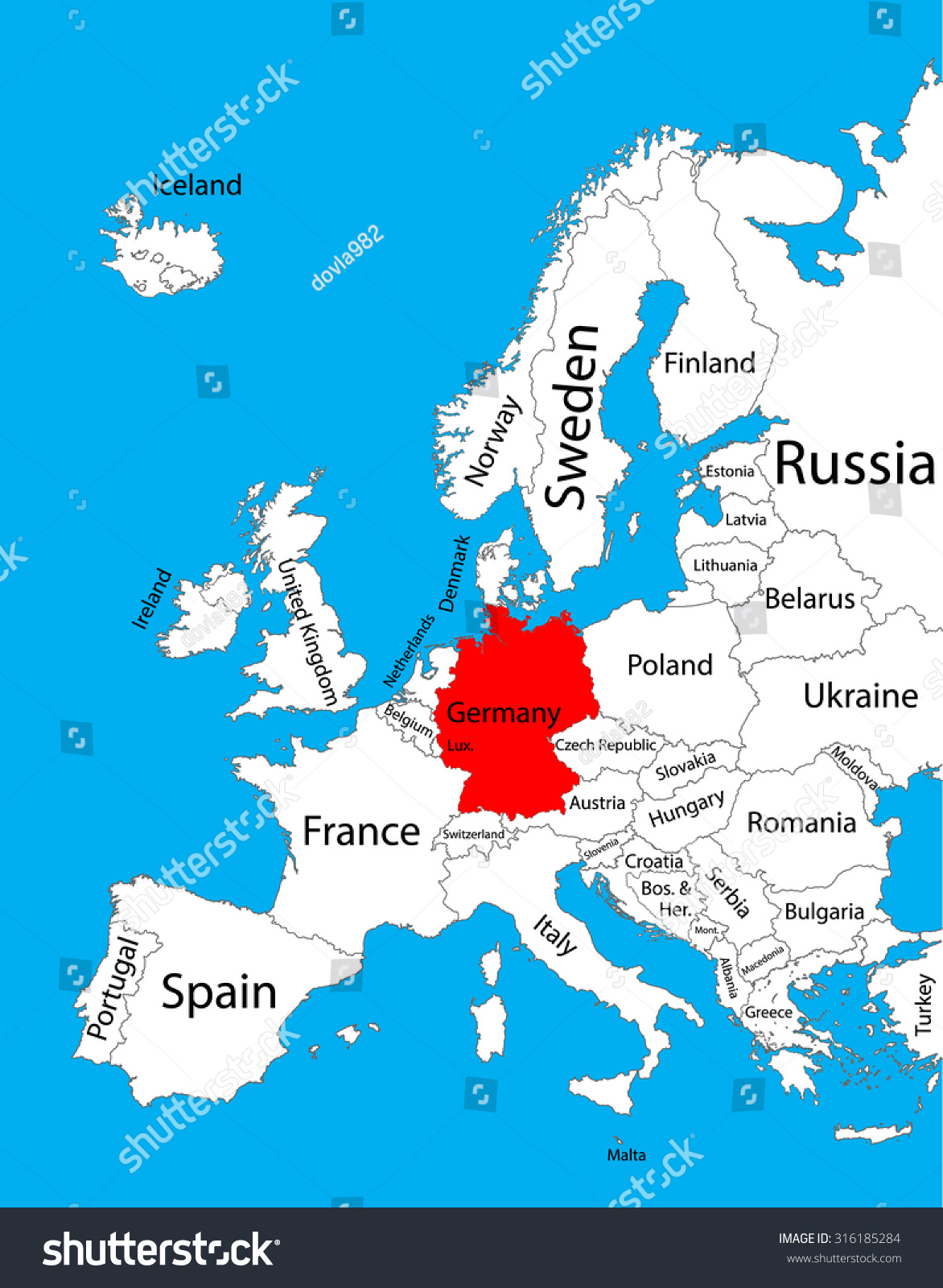
The discovery also raises urgent questions about blind spots in European counterterrorism. German authorities confirm that approximately 89 individuals listed in the recovered files have ties to Germany—either as former residents, nationals, or through familial connections. Of those, 32 are believed to still reside in the country under varying legal statuses, including asylum seekers, recognized refugees, and individuals with suspended deportation orders.
“Having a name on a list doesn’t equal imminent threat,” cautions Klaus-Peter Willsch, a member of the Bundestag’s Interior Committee.
“But it does mean we have a duty to verify, monitor, and where necessary, act. The real danger isn’t the list itself—it’s the assumption that we’ve already processed it.”
Willsch, who has advocated for tighter integration between immigration databases and security watchdogs, notes that Germany’s federal structure often hinders real-time data sharing between state police, the BKA, and federal migration offices.
From Caliphate to Cold Case: The Afterlife of Terror Data
The tactical value of these records extends beyond immediate security concerns. For historians and prosecutors, the documents offer irrefutable evidence of intent—a critical element in prosecuting terrorism-related charges under Germany’s Strafgesetzbuch (Section 89a), which criminalizes membership in a foreign terrorist organization. Unlike battlefield confiscations, these files were captured intact, preserving metadata that can trace communication patterns, financial flows, and even the chronological radicalization of individuals.

Prosecutors in Düsseldorf have already used fragments of the data to support indictments against three suspects accused of facilitating travel to Syria between 2014 and 2016. In one case, a spreadsheet entry showing a monthly stipend of €200 labeled “family support” was cross-referenced with bank transfers to a woman in Gaziantep, Turkey—later confirmed as the wife of a German-Tunisian fighter killed in Raqqa.
Yet the sheer volume of data presents a logistical challenge. The BKA estimates it will seize over 18 months to fully validate and cross-reference the recovered information with existing intelligence pools. Privacy advocates warn that rushing this process risks conflating suspicion with guilt. “We must avoid creating digital dossiers that stigmatize entire communities based on tenuous associations,” says Mireille Fanon-Mendès France, president of the Franz Fanon Foundation and advisor to the EU Fundamental Rights Agency.
“Counterterrorism cannot become a fishing expedition where bureaucratic inertia replaces judicial oversight.”
The Ghosts in the Machine: Why Some Names Remain Unacted Upon
One of the most troubling aspects of the discovery is the presence of individuals who appear to have disengaged from extremist activity years ago—yet remain listed as “active” in ISIS’s internal records. Experts suggest this may reflect outdated data, bureaucratic inertia within the terror group’s remnants, or deliberate disinformation designed to inflate perceived strength.
Dr. Hans-Jakob Schindler, senior director at the Counter Extremism Project, explains:
“Terrorist organizations, like any bureaucracy, suffer from legacy data. Just because someone’s name is in a spreadsheet doesn’t mean they’re still a threat—but it does mean we owe it to victims and survivors to check.”
His organization has urged European governments to establish independent review panels to assess such cases, balancing security needs with rehabilitation prospects.
Meanwhile, the discovery has reignited debate over Germany’s approach to returning foreign fighters and their families. While the country has repatriated dozens of orphaned children from Syrian detention camps since 2021, adult returnees face prosecution under strict anti-terrorism laws. Critics argue this binary approach fails to account for coercion, trauma, or varying levels of involvement—a nuance the ISIS records, paradoxically, may help clarify.
A Paper Trail to Accountability
What makes this seizure uniquely valuable is its dual nature: it is both an intelligence asset and a potential evidentiary goldmine. Unlike intercepted communications, which may be challenged on privacy grounds, these documents were seized during a lawful criminal investigation—meaning their admissibility in court is on firmer ground. Legal experts suggest they could serve as cornerstone evidence in future trials under Germany’s principle of universal jurisdiction, allowing prosecution of serious international crimes regardless of where they occurred.
Beyond the courtroom, the files may help families of victims seek closure. In Strasbourg, the European Court of Human Rights is currently weighing a case brought by Yazidi women who survived ISIS captivity; German prosecutors have signaled willingness to share relevant excerpts (after redaction) to support investigations into sexual slavery and genocide.
As Germany continues to sift through the digital ashes of ISIS’s administrative empire, one truth emerges with clarity: terrorism is not only fought in the dark alleys of the internet or the rubble of fallen cities—it is also defeated in the quiet, methodical work of turning terror’s own bureaucracy against it. The spreadsheets may be cold, but the implications are burning hot.
What do you think societies owe to those who once walked the path of extremism but now seek to return? And how do we balance the need for security with the imperative of mercy—without letting either become a excuse for inaction? The answers, like the data itself, are still being compiled.

