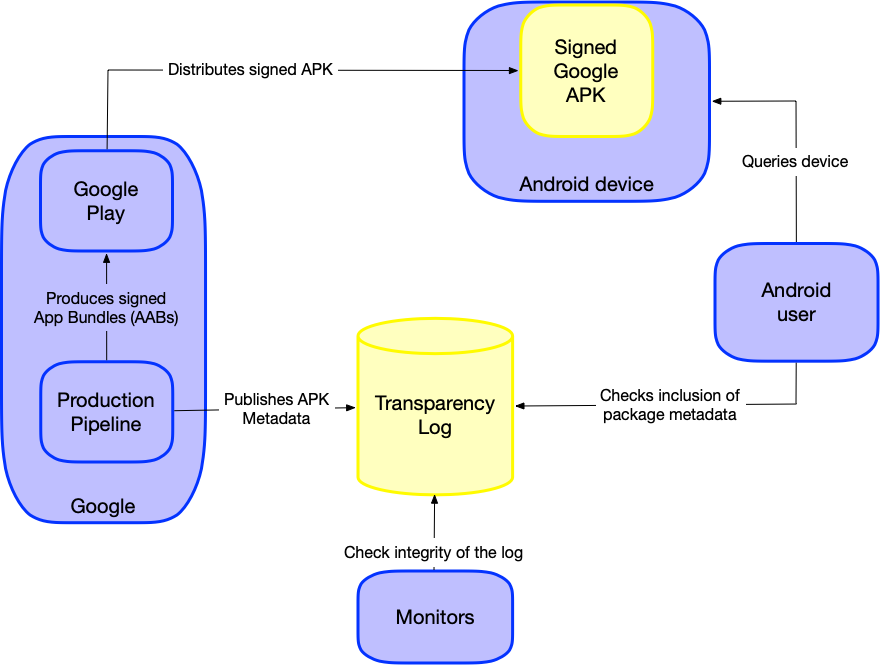
Google is expanding Android Binary Transparency to mitigate supply chain attacks by implementing a public, verifiable log of app binaries. This prevents attackers from distributing targeted, malicious versions of legitimate apps to specific users, ensuring the code running on a device matches the version officially published by the developer.
For years, the industry has relied on digital signatures to prove provenance. If an APK is signed by a trusted developer, the OS trusts it. But signatures only prove who signed the code, not what was signed. This creates a dangerous blind spot: the “targeted update” attack. In this scenario, a compromised build server or a malicious actor with access to signing keys can serve a backdoored binary to a high-value target—say, a diplomat or a journalist—while serving the pristine, legitimate binary to the rest of the world. Because the malicious binary is still signed by the correct key, standard security checks pass silently.
It is a ghost in the machine.
By rolling out the expanded Binary Transparency (BT) framework in this week’s beta, Google is essentially moving from a system of “trust the key” to “trust the log.” This is a paradigm shift toward a public ledger for software, mirroring the success of Certificate Transparency (CT) in the TLS/SSL world. When a binary is published, its cryptographic hash is recorded in an append-only, verifiable log. The device then checks this log before installation. If the binary on the device isn’t in the public log, it’s a rogue agent.
The Cryptographic Engine: Merkle Trees and Verifiable Logs
Under the hood, Android Binary Transparency relies on Merkle trees—a data structure that allows for efficient and secure verification of large sets of data. Instead of the device downloading a massive list of every app hash ever created, it uses “consistency proofs” and “inclusion proofs.” The client can verify that a specific binary hash exists within the global log without needing to process the entire ledger, keeping latency low and battery drain negligible.
This mechanism effectively kills the “split-view” attack. An attacker can no longer reveal different versions of the same app to different people without the discrepancy becoming mathematically evident to any auditor monitoring the log. To pull off a targeted attack now, the adversary would have to publish the malicious hash to the public log, effectively screaming their presence to every security researcher on the planet.
The technical brilliance here isn’t in the encryption—it’s in the visibility.
The 30-Second Verdict: Security vs. Friction
- The Win: Eliminates targeted binary substitution and mitigates the impact of compromised signing keys.
- The Cost: Slight increase in initial installation latency due to log verification.
- The Bottom Line: A mandatory evolution for any OS attempting to secure a fragmented global supply chain.
The OEM Dilemma and the Fragmentation Tax
While this is a win for the AOSP (Android Open Source Project) core, the implementation gets messy when you enter the world of Original Equipment Manufacturers (OEMs). Companies like Samsung, Xiaomi, and Oppo often wrap Google’s binaries in their own proprietary skins and optimization layers. This introduces “binary drift.”
If an OEM modifies a system binary for a specific region or hardware configuration, that binary must also be logged. If Google mandates a centralized log, OEMs lose a degree of autonomy. If they maintain their own logs, the verification process becomes fragmented, and the “transparency” is diluted. We are seeing a tension between the desire for a unified security standard and the reality of Android’s open-source architecture.
This isn’t just a technical hurdle; it’s a geopolitical one. In regions where governments demand “localized” versions of apps for surveillance purposes, Binary Transparency acts as a whistleblower. It makes state-sponsored tampering visible to the global community.
“The shift toward binary transparency is the only logical response to the professionalization of supply chain attacks. We’ve moved past the era of simple malware; we are now fighting adversaries who can compromise the build pipeline itself. Visibility is the only scalable defense.”
Bridging the Gap: Android vs. The Walled Garden
Critics often point to Apple’s closed ecosystem as the gold standard for security. Apple controls the hardware, the OS, and the App Store. They don’t need a public transparency log because they are the sole source of truth. However, that “truth” is opaque. You trust Apple because they say you should.
Google is attempting something far more ambitious: creating a “trustless” system. By using public logs, Android is arguing that you shouldn’t have to trust Google or the developer—you should trust the math. This is a strategic move to lure enterprise clients who are wary of “black box” security models. By aligning with NIST’s Software Supply Chain security frameworks, Google is positioning Android as the more transparent, and therefore more auditable, platform for government and high-security corporate employ.
To understand the delta between traditional signing and Binary Transparency, consider this comparison:
| Feature | Standard APK Signing | Binary Transparency (BT) |
|---|---|---|
| Verification Basis | Private Key Possession | Public Ledger Inclusion |
| Targeted Attack Defense | Ineffective (if key is stolen) | Highly Effective |
| Visibility | Private/Opaque | Publicly Auditable |
| Trust Model | Trust the Certificate Authority | Trust the Cryptographic Proof |
The Macro-Market Impact: The End of the “Shadow Update”
The expansion of BT signals the end of the “shadow update” era. For developers, this means a higher standard of build hygiene. You can no longer push a hotfix to a handful of beta testers via a side-channel without leaving a permanent cryptographic footprint. This forces a discipline in CI/CD pipelines that the mobile industry has historically lacked.

From a cybersecurity perspective, this is a direct counter to the tactics used in advanced persistent threats (APTs). When an adversary compromises a vendor’s build system, their goal is to remain invisible. Binary Transparency turns the lights on. It transforms the act of delivering a malicious update from a stealth operation into a public announcement.
We are seeing a convergence of software delivery and blockchain-adjacent logic—not for the sake of currency, but for the sake of immutable truth.
As this rolls out across the ecosystem, the real test will be adoption. If Google makes BT mandatory for all Play Store apps, they effectively secure the majority of the world’s mobile endpoints. If it remains an optional “opt-in” for developers, it becomes a luxury security feature rather than a systemic shield. Given the current climate of zero-day volatility and the rise of sophisticated supply chain compromises reported by outlets like Ars Technica, optionality is a risk Google can no longer afford.
The code is the law, but the log is the judge.