YouTube is currently plagued by sophisticated “Pig Butchering” scams where fraudsters harvest phone numbers from comment sections to impersonate investment experts. By leveraging social engineering and psychological manipulation, these attackers build false trust via small initial returns before executing large-scale financial thefts across global networks.
This isn’t a simple case of “internet strangers being dishonest.” It is a weaponized application of the attention economy. We are seeing a calculated pipeline that moves a target from a high-visibility, moderated environment (YouTube) to an encrypted, unmonitored dark channel (Telegram or WhatsApp), effectively stripping away every safety guardrail Google has spent a decade building.
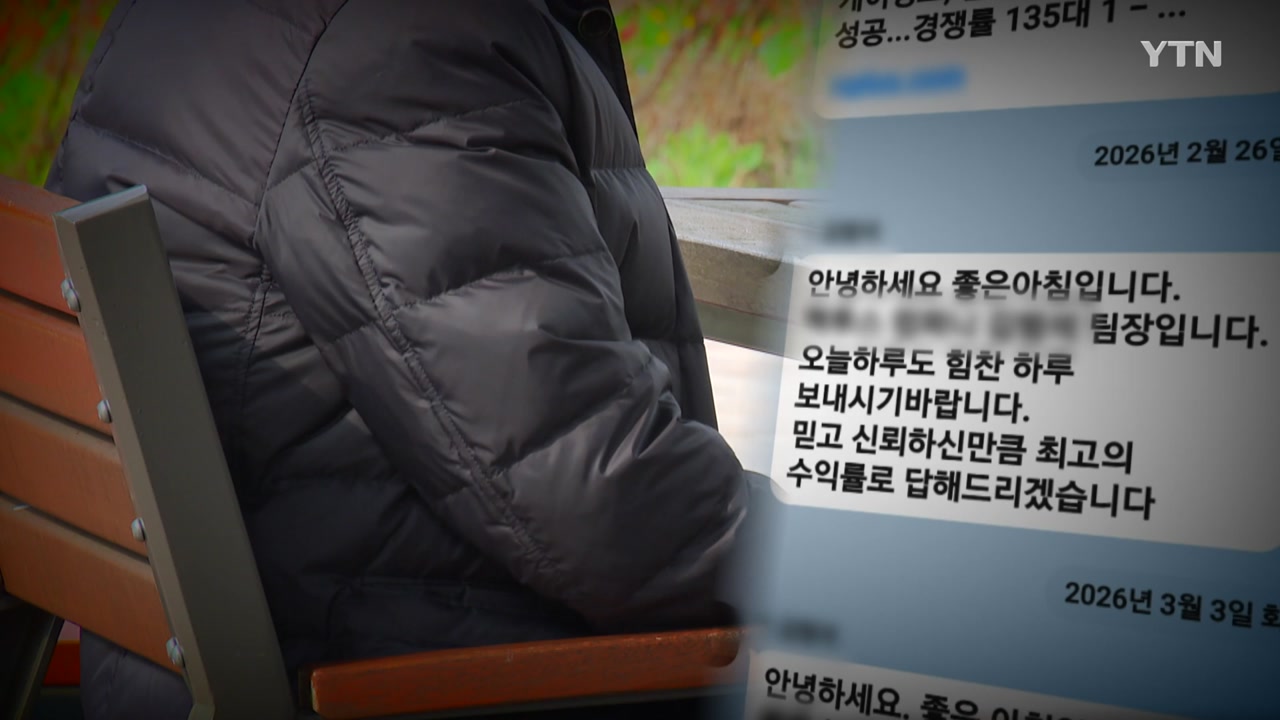
The “Team Leader Kim” persona is a classic social engineering trope, but the backend infrastructure supporting it has evolved. In the 2026 landscape, these aren’t just individuals with smartphones; they are organized syndicates utilizing automated scraping clusters and simulated trading environments to manufacture a reality that looks, feels and smells like legitimate wealth creation.
The Anatomy of the Harvest: From Comment Section to Wallet
The attack vector begins with a simple data harvest. Scammers deploy bots—likely written in Python using frameworks like Scrapy or Selenium—to monitor high-traffic finance and stock-tip videos. These bots don’t just seem for keywords; they specifically target “lead magnets,” such as comments where users leave their phone numbers in hopes of receiving “exclusive” tips.
This is Open Source Intelligence (OSINT) in its most predatory form. Once a number is captured, it is fed into a CRM (Customer Relationship Management) system that tracks the target’s perceived value based on their interaction history. The “Team Leader” doesn’t reach out immediately. They wait. They build a profile.
Then comes the pivot.
The scammer initiates contact, often via a VoIP service that masks their true location, and immediately insists on moving the conversation to an encrypted platform. This is the critical failure point in the user’s security chain. By moving to Telegram or WhatsApp, the attacker leverages End-to-End Encryption (E2EE). Whereas E2EE is a triumph for privacy, in the hands of a fraudster, it is a cloak of invisibility that prevents platform moderators and law enforcement from intercepting the crime in real-time.
The “Pig Butchering” Architecture: Simulating Profit via Shadow APIs
The most insidious part of this operation is the “fattening” phase—hence the term “Pig Butchering.” The victim is directed to a trading platform. To the untrained eye, it looks like a professional Bloomberg terminal or a high-end crypto exchange. In reality, it is a “shadow API” environment.
These platforms are essentially glorified CRUD (Create, Read, Update, Delete) applications. There is no actual trading happening on the backend. No orders are being sent to the NYSE or a crypto liquidity pool. Instead, the “Team Leader” simply manually updates a database entry to show the victim’s balance increasing. The “profits” the user sees are just numbers in a SQL table, manipulated by the admin to trigger a dopamine response.
“The brilliance of the modern investment scam is that it doesn’t start with a request for money; it starts with a demonstration of success. By allowing a victim to withdraw a small ‘profit’ early on, the attacker bypasses the brain’s critical thinking filters and installs a deep, misplaced trust.” — Marcus Thorne, Lead Cybersecurity Analyst at SentinelNode
Once the victim is convinced the system works, the “whale” phase begins. The attacker encourages a massive deposit—often the victim’s entire life savings—under the guise of a “once-in-a-lifetime” market event. The moment the large sum is transferred, the account is frozen, and “Team Leader Kim” vanishes into the ether.
The 30-Second Technical Verdict
- Vector: OSINT scraping of public YouTube comments.
- Pivot: Migration from moderated platforms to E2EE channels (Telegram/WhatsApp).
- Payload: Simulated trading dashboards (Fake Front-ends) with no real-world asset backing.
- Goal: High-value capital extraction via psychological anchoring.
The Encryption Pivot: Why the Move to Telegram is a Red Flag
From a network security perspective, the insistence on moving to a third-party app is the equivalent of a “Zero-Day” warning for your finances. When a professional advisor asks you to leave a secure, verified corporate channel for a personal chat app, they are intentionally breaking the chain of custody for the conversation.
This move serves two purposes for the attacker. First, it avoids the automated spam and fraud detection algorithms of YouTube. Second, it allows them to use “disappearing messages” to erase the evidence of their promises and instructions. This makes forensic recovery nearly impossible once the scam is realized. If you cannot audit the communication, you cannot prove the fraud.
We are seeing a dangerous intersection here between the democratization of privacy tools and the professionalization of cybercrime. The very tools designed to protect dissidents from authoritarian regimes are now being used to shield financial predators from the law.
Hardening the Human Firewall: Enterprise-Grade Defense for the Individual
We cannot wait for Google or Meta to solve this. The “human layer” is the most vulnerable part of the stack, and it requires a patch. To defend against these high-fidelity social engineering attacks, users must adopt a mindset similar to NIST’s Zero Trust Architecture: Never trust, always verify.
If an investment opportunity requires you to provide a phone number in a public forum, it is a scam. If the “expert” refuses to communicate through official, verifiable corporate channels, it is a scam. If the returns are consistent regardless of market volatility, it is a simulation.
| Red Flag Indicator | Technical Reality | Safe Alternative |
|---|---|---|
| Public Phone Harvesting | Bot-driven OSINT scraping | Official contact forms/Email |
| Urgency to move to Telegram | Evading platform moderation/E2EE cloak | Verified corporate portals |
| Guaranteed high returns | Hard-coded database manipulation | Regulated brokerage accounts |
| “Small win” early withdrawals | Psychological anchoring (The “Bait”) | Due diligence via SEC/FCA registries |
The battle against “Team Leader Kim” isn’t won with better firewalls; it’s won with better skepticism. In an era of deepfakes and shadow APIs, the only reliable security protocol is a refusal to engage with any financial entity that operates in the shadows of an encrypted chat app.