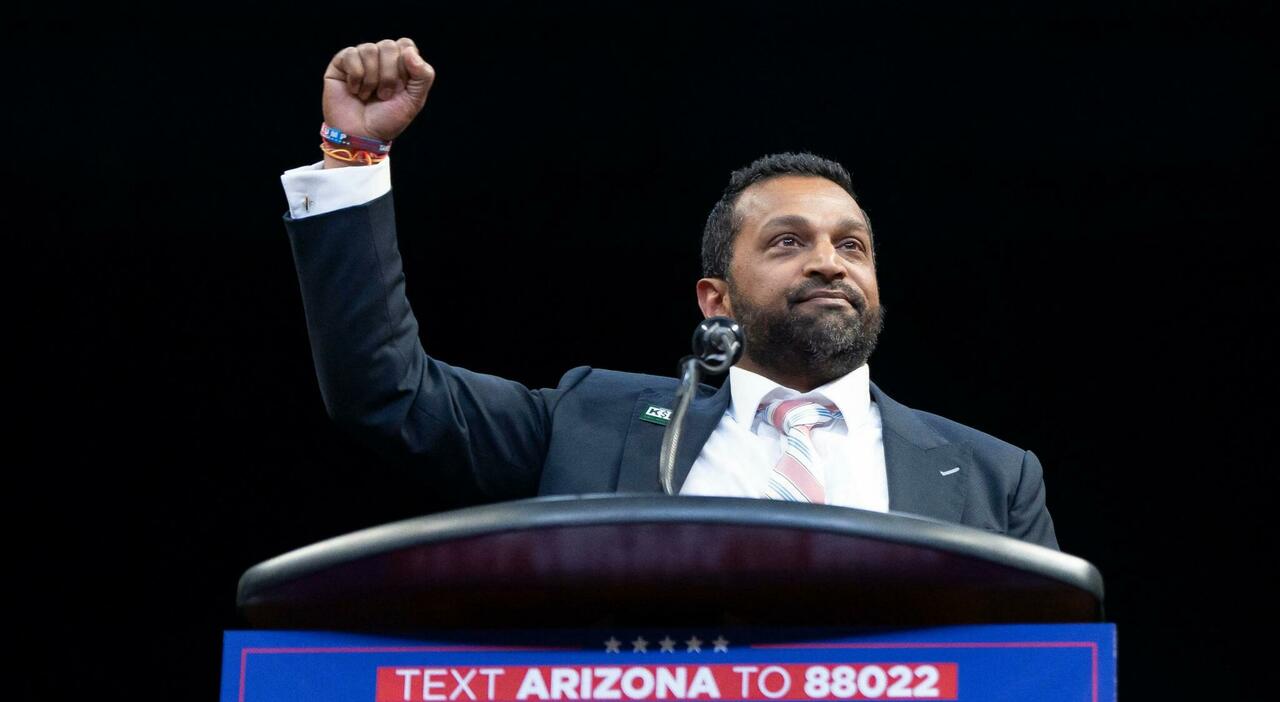
The digital world felt a familiar shudder this week as news broke of a sophisticated cyberattack targeting Kash Patel, the former Director of National Intelligence under President Trump and a current FBI official. The Handala Hack Team, widely suspected of ties to Iranian cyber-intelligence, didn’t just breach Patel’s personal email; they publicly displayed the spoils – intimate photos and a sampling of emails spanning over a decade. The question echoing across Washington and cybersecurity circles isn’t simply *how* this happened, but a far more unsettling one: is this a harbinger of a new, more aggressive phase in state-sponsored digital warfare?
Beyond Embarrassment: The Strategic Logic of “Naming and Shaming”
While the initial reaction focused on the potentially embarrassing nature of the leaked photos – cigars, a vintage convertible, and a selfie with rum – experts suggest the attack’s true intent is far more calculated. This isn’t about uncovering classified information, at least not directly. It’s about psychological warfare, a tactic known as “naming and shaming.” The Handala Hack Team, according to security analysts, aims to undermine confidence in U.S. Leadership by exposing vulnerabilities and creating a sense of unease.
“The goal here isn’t necessarily espionage, it’s degradation,” explains Gil Messing, Chief Staff of cybersecurity firm Check Point, in a statement to Archyde.com. “By targeting individuals personally, these actors attempt to erode trust in institutions and create a climate of fear and uncertainty. It’s a way of signaling capability and intent without necessarily triggering a large-scale kinetic response.”
This tactic aligns with a broader pattern of Iranian cyber activity. Recent targets have included Stryker, a major medical device manufacturer, and Lockheed Martin, with sensitive employee data being leaked in the Middle East. Security Affairs details the increasing frequency and sophistication of these attacks, noting a shift towards targeting critical infrastructure and key personnel.
A History of Digital Intrusions: Echoes of Past Breaches
The Patel hack isn’t an isolated incident. It evokes chilling parallels to previous breaches targeting high-ranking U.S. Officials. The 2016 hack of John Podesta, Hillary Clinton’s campaign chairman, and the 2015 breach of CIA Director John Brennan, both attributed to Russian intelligence, demonstrated the potential for politically damaging leaks. The Council on Foreign Relations provides a comprehensive overview of the escalating threat of cyber warfare and the challenges of attribution.
Whereas, the Iranian approach appears distinct. While Russian attacks often focused on influencing elections or stealing sensitive political information, Iran seems more focused on direct intimidation and the erosion of trust. This difference may stem from Iran’s asymmetric capabilities. Unable to directly challenge the U.S. Militarily, Tehran relies heavily on cyber warfare as a means of projecting power and achieving strategic objectives.
Escalation and Response: The Intelligence Community’s Assessment
U.S. Intelligence officials are taking the threat seriously. A recent assessment, circulated on March 2nd, suggests Iran is intensifying these “low-level” attacks in response to the U.S. Assassination of Qassem Soleimani, the former commander of the Islamic Revolutionary Guard Corps’ Quds Force. The assessment, reported by NBC News, warns that this could be just the “tip of the iceberg,” with other Iranian-linked hacking groups threatening to release vast amounts of data stolen from key figures in the Trump administration, including Susie Wiles, Trump’s former chief of staff.
The FBI confirmed the breach targeting Patel, stating that immediate mitigation measures were taken to neutralize any risks. Spokesperson Ben Williamson emphasized that the compromised data was “historical” and did not contain classified government information. However, this reassurance does little to quell concerns about the vulnerability of U.S. Officials to cyberattacks.
The Vulnerability of Personal Accounts and the Demand for Enhanced Security
The Patel incident highlights a critical vulnerability: the security of personal accounts used by government officials. Despite stringent security protocols for official communications, personal email and social media accounts often remain significantly less protected. This creates a potential backdoor for adversaries to gain access to sensitive information or, as in this case, to simply embarrass and intimidate.
“We’ve known for years that personal accounts are a weak link,” says Dr. Emily Harding, Senior Fellow at the Center for Strategic and International Studies (CSIS). “The challenge is balancing security with the need for officials to maintain a degree of personal privacy. It’s a difficult line to walk, but one we must address urgently.”
“The reality is that even the most sophisticated security measures can be circumvented. The human element is often the weakest link, and that’s where adversaries will focus their efforts.” – Dr. Emily Harding, CSIS.
The incident also raises questions about the effectiveness of current cybersecurity training and awareness programs for government personnel. Are officials adequately informed about the risks of phishing attacks, social engineering, and other common cyber threats? Are they encouraged to adopt strong password practices and enable multi-factor authentication on all their accounts?
Looking Ahead: A New Era of Digital Conflict?
The attack on Kash Patel is more than just a data breach; it’s a signal. It suggests that Iran is willing to employ increasingly aggressive tactics in the cyber domain, targeting individuals directly in an attempt to undermine U.S. Influence and sow discord. This is a worrying trend, and one that demands a comprehensive response.
That response must include not only enhanced cybersecurity measures for government officials but also a broader strategy for deterring Iranian cyber aggression. This could involve imposing sanctions on Iranian individuals and entities involved in cyberattacks, as well as working with international partners to develop norms of behavior in cyberspace. The U.S. State Department’s cybersecurity policy outlines the administration’s approach to addressing these challenges.
The digital battlefield is constantly evolving, and the stakes are higher than ever. The Patel hack serves as a stark reminder that cybersecurity is not just a technical issue; it’s a national security imperative. As we navigate this new era of digital conflict, we must be prepared to defend ourselves against a determined and resourceful adversary. What steps do *you* think are most critical to bolstering U.S. Cybersecurity defenses in the face of escalating threats from state-sponsored actors?