In a quiet but significant shift this week, Microsoft has quietly enabled users to pause Windows updates indefinitely—a move that redefines the power dynamic between operating systems and their users, particularly in environments where system stability trumps automatic patching. This change, rolling out in the Windows 11 22H2 and 23H2 cumulative updates, allows administrators and power users to suspend feature and quality updates through Group Policy or the Windows Update settings interface without time limits, effectively granting permanent control over when—or if—a device receives Microsoft’s latest code. While framed as a user-experience improvement, the decision carries deep implications for enterprise IT, cybersecurity hygiene, and the ongoing tension between vendor control and user autonomy in closed ecosystems.
The Mechanics Behind the Pause: How Windows Update Orchestration Actually Works
Under the hood, Windows Update relies on the Unified Update Platform (UUP), a telemetry-driven backend that coordinates feature updates via UUP delivery and quality patches through the Component Based Servicing (CBS) stack. Prior to this change, the PauseUpdatesExpiry registry key enforced a maximum 35-day pause, after which updates would resume regardless of user preference—a hard limit designed to prevent systems from falling dangerously behind on security patches. The new policy removes this expiry, allowing the PauseUpdatesExpiry value to be set to 0 or left unset indefinitely, effectively disabling the timer. This is not a registry hack but a supported configuration via Set-WUServiceManager in PowerShell or through Mobile Device Management (MDM) tools like Intune, using the Update/AllowAutoUpdate CSP. For enterprise environments, this means Group Policy Object (GPO) settings under Computer Configuration → Administrative Templates → Windows Components → Windows Update → Manage updates offered from Windows Update can now enforce a permanent pause without triggering compliance flags in systems like SCCM or Windows Update for Business.
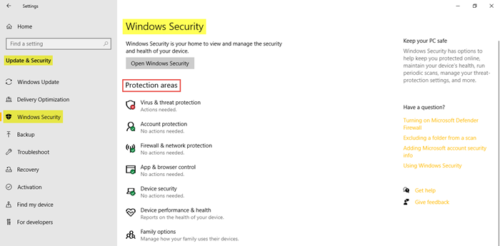
Critically, this does not disable the Windows Update service (wuauserv) nor block access to the Microsoft Update cloud endpoints—it merely instructs the client to defer evaluation of available updates. Security updates remain available for manual installation via the Settings → Windows Update → Check for updates button or through WSUS/Configuration Manager, preserving the ability to patch critical CVEs on a controlled schedule. This distinction matters: unlike disabling the service entirely—which breaks Store apps, driver updates, and Windows Defender signature refreshes—this method maintains a dormant but functional update pipeline.
Enterprise Implications: Stability vs. Security in the Age of Evergreen OS
For industries reliant on long-lived, validated software stacks—such as industrial automation, medical imaging, or financial trading systems—the ability to freeze Windows updates is less a convenience and a necessity. A single cumulative update can break legacy COM objects, alter driver signing requirements, or change registry behaviors that third-party software depends on. In 2025, a study by the SANS Institute found that 22% of unplanned downtime in manufacturing environments stemmed from Windows Update-induced driver conflicts, particularly with legacy PCIe-based acquisition cards. “We’ve seen production lines halt because a KB update changed the way USB 3.0 host controllers enumerate devices,” said Marta Lengyel, Director of Industrial Systems at Siemens Healthineers, in a recent interview with Dark Reading. “Having the ability to say, ‘This system is locked at 22H2 until we requalify the next release’ isn’t laziness—it’s risk management.”

Yet cybersecurity professionals warn that permanent pauses, if mismanaged, could create silent vulnerabilities. Unlike a disconnected air-gapped system, a paused Windows machine still communicates with Microsoft’s telemetry and licensing endpoints, meaning it remains visible to asset inventories but may miss critical patches. The Cybersecurity and Infrastructure Security Agency (CISA) continues to recommend that systems not exposed to the internet follow a 30-day patch cycle for critical vulnerabilities, with exploitability increasing exponentially after 60 days. “Pause doesn’t signify forget,” cautioned Jen Ellis, VP of Community & Public Affairs at Rapid7, during a 2024 RSA Conference panel. “It means you’ve consciously accepted the risk of running outdated code—and you better have compensating controls like network segmentation, application allowlisting, or behavioral monitoring in place.”
Breaking the Vendor Lock-In Narrative: A Rare Concession to User Agency
This move stands in stark contrast to Microsoft’s historical posture of enforcing update compliance as a non-negotiable pillar of its “secure by default” strategy. For years, the company argued that automatic updates were essential to combat the long tail of unpatched systems exploited by ransomware groups like Conti and LockBit. The shift suggests either a recognition of user fatigue—Windows Update remains one of the top three sources of frustration in Microsoft’s own Customer Experience surveys—or a strategic calculation that enterprise control reduces support burden more than it increases risk. Notably, the change does not extend to Windows Update for Business deferral policies, which still cap quality updates at 30 days and feature updates at 360 days, indicating the concession is primarily aimed at power users and specialized environments rather than mainstream consumers.
From an ecosystem perspective, the decision indirectly benefits open-source projects that rely on Windows as a deployment target. Tools like Chocolatey, used for package management in DevOps pipelines, often require stable OS baselines to avoid breaking changes in PowerShell execution policies or .NET Framework versions. Similarly, projects like MSYS2, which provides a Unix-like environment on Windows, depend on consistent subsystem behavior that cumulative updates can disrupt. By allowing users to freeze the OS state, Microsoft reduces friction for these communities without abandoning its update mandate for the broader user base.
The Bigger Picture: Who Really Controls Your PC?
This change is not merely about convenience—it’s a tacit acknowledgment that the era of unilateral vendor control over endpoint behavior is evolving. As regulatory scrutiny intensifies around digital autonomy—evidenced by the EU’s Digital Markets Act and ongoing FTC investigations into software lock-in—Microsoft’s move may be less altruistic and more preemptive. By giving users the illusion of control (while still requiring manual intervention for security patches), the company navigates a middle path: appeasing power users without compromising the security baseline for the 1.4 billion active Windows devices.
For now, the permanent pause remains a tool for the knowledgeable—a setting buried in Group Policy, not a toggle in the consumer-facing Settings app. But its existence shifts the conversation: Windows is no longer an evergreen service that updates you whether you like it or not. It is, conditionally, a platform you can choose to pause. And in the balance between security and sovereignty, that distinction may prove more consequential than any patch Tuesday.
