Microsoft has effectively crippled VeraCrypt by suspending the lead developer’s account, triggering Driver Signature Enforcement (DSE) blocks across Windows installations. This move disrupts critical disk encryption for thousands, highlighting the systemic fragility of open-source security tools dependent on proprietary vendor trust anchors and account-based verification.
This isn’t a bug. It’s a structural failure of the “Root of Trust.” When your security depends on a third-party tool, but that tool’s ability to function depends on a single corporate account’s standing with a trillion-dollar vendor, you aren’t actually in control of your data. You’re renting permission to encrypt it.
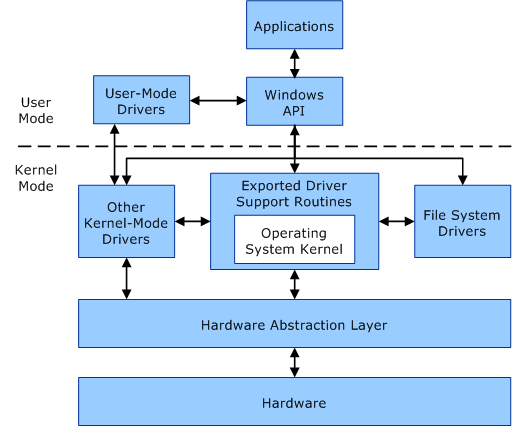
For the uninitiated, VeraCrypt operates at the kernel level. To encrypt a drive or create a hidden volume, the software must load a driver into the Windows kernel—the most privileged part of the operating system. Microsoft requires these drivers to be digitally signed via the Windows Hardware Quality Labs (WHQL) process. If the developer’s account is nuked or the certificate is revoked, Windows sees the driver as unsigned or malicious. The result? A total lockout.
The Kernel-Mode Kill Switch and the DSE Paradox
The mechanism at play here is Driver Signature Enforcement (DSE). In a modern x86-64 Windows environment, DSE ensures that only verified code can execute in kernel mode. Here’s a critical defense against rootkits and boot-level malware. Yet, when applied to open-source projects, DSE becomes a centralized kill switch. By suspending the developer’s account, Microsoft didn’t have to patch the code or issue a CVE; they simply revoked the “passport” the software uses to enter the CPU’s inner sanctum.
This creates a dangerous paradox. We apply VeraCrypt to protect data from prying eyes—including, potentially, the OS vendor itself. Yet, the particularly act of implementing that protection requires the OS vendor’s explicit, ongoing blessing. If the blessing is withdrawn, the software is rendered inert.
Consider the architectural impact. When Microsoft’s Driver Signing requirements are enforced, the OS checks the signature against a revoked certificate list (CRL). Once the developer’s account was flagged, the certificate became a liability. For users with Hypervisor-Protected Code Integrity (HVCI) enabled, the block is absolute. The system simply refuses to load the driver, leaving users unable to mount their encrypted volumes.
The 30-Second Verdict: Why This Is a Crisis
- Single Point of Failure: One account suspension can brick the utility of a global security tool.
- Trust Erosion: It proves that “open source” on Windows is still subject to proprietary gatekeeping.
- Data Accessibility: Users cannot access their encrypted containers without disabling core OS security features.
Ecosystem Lock-in and the War on Third-Party Encryption
This incident is a microcosm of the broader trend toward “walled garden” security. We see this mirrored in Apple’s notarization process for macOS, where every binary must be signed and “notarized” by Apple before it can run without a scary warning. While the stated goal is user safety, the side effect is absolute platform control.
By tightening the screws on kernel access, Microsoft is pushing the ecosystem toward BitLocker. BitLocker is integrated, seamless, and—most importantly—controlled entirely by Microsoft. When the “alternative” (VeraCrypt) becomes unstable due to administrative whims, the path of least resistance is to migrate to the native solution. This isn’t just a technical hurdle; it’s a market dynamic designed to eliminate friction for the proprietary product by introducing friction for the open-source rival.
“The centralization of trust in modern operating systems has created a precarious environment for security researchers and open-source developers. When the identity provider is too the platform provider, ‘neutrality’ is an illusion.”
The implications for enterprise IT are severe. Organizations relying on VeraCrypt for compliance-mandated encryption now face a choice: stay on a platform that could be revoked at any moment or migrate their entire data architecture to a vendor-locked solution. The risk of “administrative lockout” is now a legitimate threat vector in risk assessments.
Technical Mitigation and the Danger of ‘Test Mode’
For users currently locked out, the only immediate workaround is to disable Driver Signature Enforcement. This is typically done by booting into the Windows Recovery Environment (WinRE) and enabling “Disable Driver Signature Enforcement” mode. Alternatively, one can use bcdedit /set testsigning on to put Windows into Test Mode.
But here is the catch: doing this opens a massive hole in your security posture. Test Mode disables the very protections that prevent malware from installing its own kernel-mode drivers. To save your encrypted data, you must essentially advise your OS to stop checking who is allowed to touch the hardware.
Below is a comparison of the trust models currently competing in the Windows ecosystem:
| Feature | BitLocker (Proprietary) | VeraCrypt (Open Source) | Linux LUKS (Open) |
|---|---|---|---|
| Root of Trust | Microsoft / TPM | Developer Certificate | Kernel / User Key |
| Execution Path | Native Kernel | Signed Driver (DSE) | Native Kernel |
| Account Dependency | Microsoft Account/AD | Developer MS Account | None |
| Revocation Risk | Low (Internal) | High (External) | Negligible |
The Path Forward: Moving Beyond the Certificate
The VeraCrypt crisis proves that we require a decentralized approach to driver verification. Relying on a single corporate account to vouch for a project used by millions is a design flaw. The community should be pushing for a multi-sig approach to driver signing or a community-governed Certificate Authority (CA) that Microsoft recognizes as a trusted entity, rather than tying the fate of the software to one individual’s account status.
Until then, the lesson is clear. If you are using VeraCrypt or any other third-party kernel-level tool on Windows, you are operating on borrowed time. The “Open” in open-source only applies to the code; the execution is still a proprietary privilege.
For those who cannot afford this risk, the move toward Linux-based encryption like LUKS (Linux Unified Key Setup) is no longer just a preference for “power users”—it is a strategic necessity for data sovereignty. In the battle between the open-source community and the platform giants, the giants hold the keys to the kingdom. And they aren’t afraid to change the locks.

